March 31, 2016
PRINCIPAL TRENDS IN MARCH
- Detection of an adware Trojan for Android that infected popular applications and firmwares of several dozens of mobile devices
- Detection of an advertising spyware in more than 100 Google Play applications
- Accomplished analysis of dangerous Trojans that can inject themselves into an Android system process together with processes of other programs
Mobile threat of the month
In March, Doctor Web specialists examined Android.Gmobi.1, a malicious program for Android that was detected in such apps as TrendMicro Dr.Safety, TrendMicro Dr.Booster and Asus WebStorage, and was also preinstalled on more than 40 mobile devices. This Trojan is a specialized program SDK (Software Development Kit) platform usually used by either mobile device manufacturers or by software developers. Presumably, its authors did not intend to create a Trojan; however, this module performs typical adware functions.
Therefore, Android.Gmobi.1 can display annoying advertisements—for example, in the status bar or on top of running applications. Besides, the Trojan creates shortcuts on the home screen without user knowledge, opens pages in browsers and in Google Play, and downloads, installs and runs various software. In addition to all these malicious actions, Android.Gmobi.1 can also act as a spyware program by stealing confidential information and sending it to the server. To read more about this Trojan, refer to the news article.
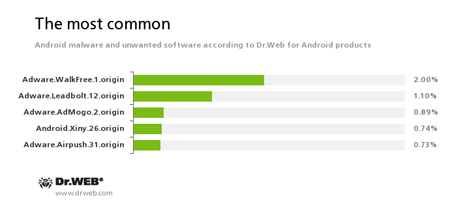
According to statistics collected by Dr.Web for Android
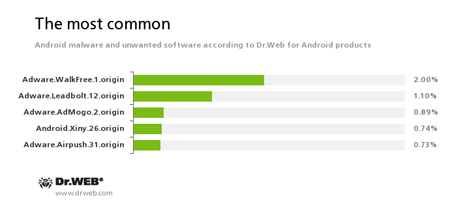
Adware.WalkFree.1.origin
Adware.AdMogo.2.origin
An unwanted program module that is incorporated into the Android applications and is responsible for advertising on mobile devices.-
A Trojan that gets root privileges, installs itself into the system registry, and then is able to install various applications without user knowledge. In addition, it displays annoying advertisements.
-
An unwanted program module that is incorporated into the Android applications and is responsible for advertising on mobile devices.
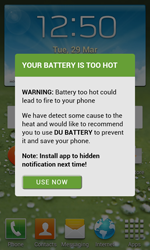
Spyware
In the end of the past month, Doctor Web specialists found an advertising spyware Trojan named Android.Spy.277.origin in more than 100 apps published on Google Play. This malware profram was mainly distributed via bogus versions of popular software. Malicious functions of Android.Spy.277.origin include sending confidential information to the server and display of annoying advertisements to the user.
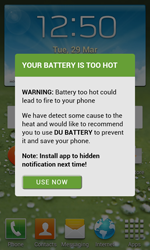

In particular, it can deliver advertisemets on top of running applications or the operating system interface, show notifications in the status bar, create shortcuts on the home screen, and automatically open webpages in browsers. For more information about this malware, refer to the news article published by Dictor Web.
Notable Trojans
In March, Doctor Web specialists examined a group of Trojans for Android belonging to the Android.Triada family. These Trojans can inject themselves into an important Android system process—Zygote—and perform their malicious actions upon cybercriminals’ command. The Zygote process is responsible for starting applications. When an application is run, the process creates its own copy that contains system libraries and other necessary components. Once the Trojans are injected into Zygote, they can infect processes of all running applications and, therefore, perform their malicious functions on behalf or with privileges of these applications.
Main malicious functions of the Android.Triada Trojans are to covertly send SMS messages and to change texts and phone numbers of messages that are sent by the user from the infected device. Nevertheless, these malware programs can download additional modules from the server to perform other malicious actions.
It is noteworthy that the Android.Triada Trojans incorporate the feature of self-protection. In particular, they try to track and terminate operation of several popular Chinese anti-virus programs. In addition, they control integrity of their components—it means that if one of malicious objects is deleted, it will be restored from the device’s RAM.
The emergence of the Android.Triada Trojans proved once again that malware for Android mobile devices is becoming more dangerous and sophisticated and is almost equal to the fanciest Trojans for Windows. Doctor Web specialists keep a close watch on Android malware landscape and timely update the Dr.Web virus database with signatures of new malicious applications.