Doctor Web’s March 2020 virus activity review
April 13, 2020
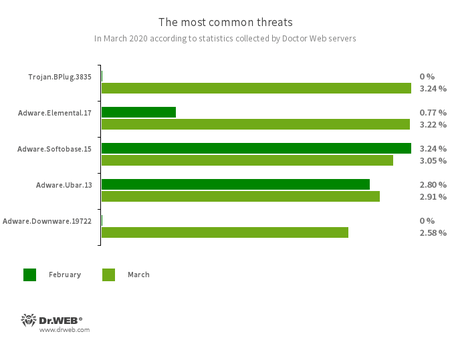
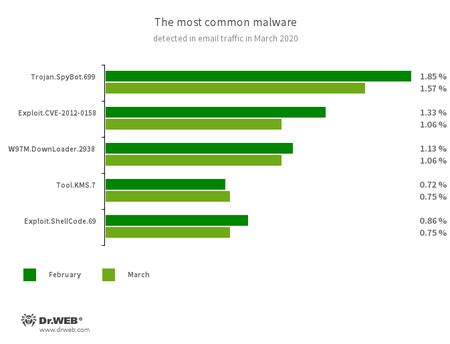
In March, analysis of Dr.Web’s statistics revealed a 12.51% increase in the total number of threats compared to the previous month. The number of unique threats increased by 8.75%. Users were mostly threatened by malware browser extensions, unwanted programs and adware. Email traffic was still dominated by the Trojan.SpyBot.699 banking trojan and malware that exploits vulnerabilities in Microsoft Office programs.
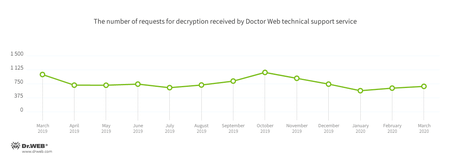
In March, the number of user requests to decrypt files affected by encoders increased by 7.63% compared with February. Trojan.Encoder.26996 was the most active encoder, accounting for 32.60% of all incidents.
Principal trends in March
- Growth in malware spreading activity
- The rise of malicious browser extensions
- An upturn in encoder activity
- A growing number of non-recommended and malicious websites
Threat of the month
In March, Doctor Web virus analysts reported that certain websites, from blogs to corporate pages created using WordPress CMS, had been compromised. The JavaScript script embedded in the hacked pages code redirected visitors to a phishing site where they were prompted to install an important security update for the Chrome browser. The downloadable file was a malware installer that allowed attackers to remotely control the infected computers and deliver auxiliary malicious modules to them.
According to Doctor Web’s statistics service
The most common threats in March:
- Trojan.BPlug.3835
- A malicious browser extension designed to perform web injections into viewed webpages and block third-party advertisements.
- Adware.Elemental.17
- Adware that spreads through file sharing services as a result of link spoofing. Instead of normal files, victims receive applications that display advertisements and install unwanted software.
- Adware.Softobase.15
- Installation adware that spreads outdated software and changes browser settings.
- Adware.Ubar.13
- A torrent client designed to install unwanted programs on a user’s device.
- Adware.Downware.19722
- Adware that often serves as an intermediary installer of pirate software.
- Trojan.SpyBot.699
- A multi-module banking trojan that allows cybercriminals to download and launch various applications on an infected device and run arbitrary code.
- Exploit.CVE-2012-0158
- A modified Microsoft Office document that exploits the CVE-2012-0158 vulnerability in order to run malicious code.
- W97M.DownLoader.2938
- A family of downloader trojans that exploits vulnerabilities in Microsoft Office documents and can download other malicious programs to a compromised computer.
- Tool.KMS.7
- Hacking tools that are used to activate illegal copies of Microsoft software.
- Exploit.ShellCode.69
- A malicious Microsoft Office Word document that exploits the CVE-2017-11882 vulnerability.
Encryption ransomware
In March, Doctor Web’s virus laboratory registered 7.63% more requests to decode files encoded by trojan ransomware than in February.
- Trojan.Encoder.26996 — 32.60%
- Trojan.Encoder.29750 — 9.07%
- Trojan.Encoder.567 — 4.66%
- Trojan.Encoder.11464 — 3.19%
- Trojan.Encoder.11539 — 1.96%
Dr.Web Security Space for Windows protects against encryption ransomware
Dangerous websites
In March 2020, Doctor Web added 186 881 URLs to the Dr.Web database of non-recommended websites.
| February 2020 | March 2020 | Dynamics |
|---|---|---|
| + 90 385 | + 186 881 | + 106.76% |
Malicious and unwanted programs for mobile devices
In March, Dr.Web’s statistics for Android devices confirmed an almost 21% increase in the total number of threats on protected devices compared to February. Doctor Web virus analysts uncovered new threats on the Google Play catalog. These include another modification of the Android.Joker family, which subscribe victims to paid services and download additional malicious components, and a new malware called Android.Circle.1. Controlled by the attackers, this trojan displayed ads and loaded websites, imitating users’ actions.
The following March events related to mobile malware are the most noteworthy:
- Detection of new threats on Google Play
- Growth in malware activity on protected devices
Find out more about malicious and unwanted programs for mobile devices in our special overview.