May 2018 virus activity review from Doctor Web
May 31, 2018
In May Doctor Web finished examining several Trojans threatening users of the popular gaming platform Steam. The Trojans were stealing the account data of computer gaming fans and replacing the collectibles exchanged during deals. Also during May numerous fraudulent websites were detected. Their addresses have been added to our databases of non-recommended web resources. Among those addresses, webpages exploiting the topic of the upcoming 2018 FIFA World Cup appear frequently. In early May virus analysts examined several stealers engaged in pilfering confidential information from infected devices.
Principal Trends in May
- The spread of Trojans posing a threat to Steam users
- The detection of numerous fraudulent websites
- The emergence of spyware that steals personal information
Threat of the month
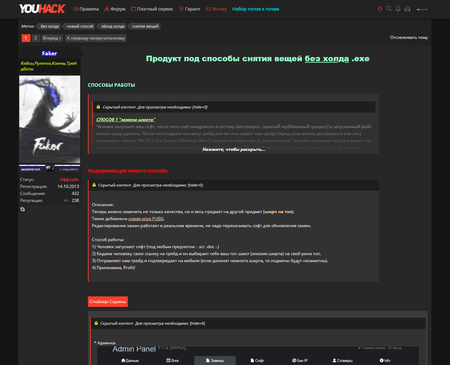
The creator of the malicious programs added to the Dr.Web virus database as Trojan.PWS.Steam.13604 and Trojan.PWS.Steam.15278 has developed a special scheme for their distribution. Cybercriminals wanting to acquire illegal earnings are not required to provide anything except money and, in some cases, a domain: the virus writer provides them with the Trojan, access to an administrative panel, and technical support.
Once it infects a computer, Trojan.PWS.Steam.13604 displays a fake Steam authorization window. If the victim enters their login credentials, the Trojan tries to use them to authorize on Steam. If this attempt is successful and Steam Guard—a two-factor authentication system for protecting user accounts—is enabled on the computer, the Trojan displays a fake window for inputting the authorization code. All this information is sent to the cybercriminals’ server.
Another malicious program by the same author, Trojan.PWS.Steam.15278, is aimed at stealing Steam inventory. For this purpose, on numerous exchange platforms, the Trojan uses web injections to substitute who receives the collectibles, resulting in the items ending up with cybercriminals. When exchanging inventory items with the help of the official steamcommunity.com website, the malicious program intercepts and modifies traffic to replace the collectibles displayed on the victim’s computer. As a result, the user will think that they are purchasing some valuable item, when in reality their gaming account gets a totally different and much cheaper item.
For more information on the distribution methods of these Trojans and the principles of their operation, refer to this article on our website.
According to Doctor Web’s statistics servers
- JS.BtcMine.36
- A JavaScript designed to stealthily mine cryptocurrencies (mining).
- JS.Inject
- A family of malicious JavaScripts. They inject malicious script into the HTML code of webpages.
- Trojan.PWS.Stealer
- A family of Trojans designed to steal passwords and other confidential information stored on an infected computer.
- Trojan.MulDrop8.25070
- A dropper Trojan that installs other malicious programs to the system.
- Win32.HLLW.Shadow
- A worm that replicates itself through removable media and network drives. In addition, it can be spread via a network through the use of the standard SMB protocol. It can download executable files from a command and control server and run them.
Statistics concerning malicious programs discovered in email traffic.
- Trojan.Dimnie.14
- A spyware Trojan capable of stealing confidential information from an infected device and providing illegal access to an infected computer. It also has a built-in banking module.
- JS.DownLoader
- A family of malicious JavaScripts. They download and install malicious software on a computer.
- JS.Inject
- A family of malicious JavaScripts. They inject malicious script into the HTML code of webpages.
- JS.BtcMine.36
- A JavaScript designed to stealthily mine cryptocurrencies (mining).
- Trojan.DownLoader
- A family of malicious programs designed to download other malware to the compromised computer.
Encryption ransomware
In May, victims of the following modifications of encryption ransomware most frequently contacted Doctor Web’s technical support service:
- Trojan.Encoder.11464 — 15.90% requests;
- Trojan.Encoder.858 — 11.33% requests;
- Trojan.Encoder.24249 — 6.16% requests;
- Trojan.Encoder.10700 — 3.78% requests;
- Trojan.Encoder.13671 — 3.70% requests;
- Trojan.Encoder.4592 — 2.39% requests.
Dr.Web Security Space for Windows protects against encryption ransomware
Dangerous websites
With the FIFA World Cup approaching, numerous network fraudsters have sprung into action to capitalize on the intense public interest in the topic of the World Cup. To attract visitors, the fraudsters are using the official FIFA World Cup symbols on their websites. They are inviting anyone who is interested to participate in prize drawings that have supposedly been organized by FIFA, major banks and international investment funds.
The cybercriminals are promising prizes of expensive cars, significant amounts of money, overseas package tours, and, of course, free FIFA World Cup tickets. The scheme being used by the cybercriminals is not new: a potential victim is notified of a big prize that can only be received by transferring several hundred rubles to the cybercriminals’ account. There’s no prize for guessing that after transferring the money, the fraud victim is not going to get any prize. In May 2018, Doctor Web specialists updated the Parental and Office Control databases with several dozen addresses of such resources. However, websites similar in content and design continue to appear frequently.
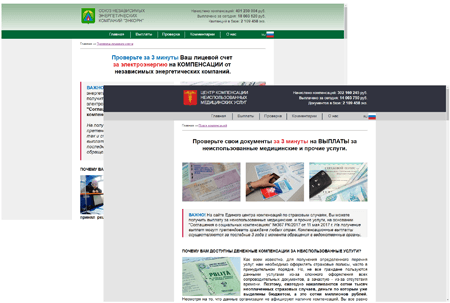
In May cases of links to fraudulent websites being spread via SMS and messengers became increasingly commonplace. The fraudsters involved offer potential victims the opportunity to be compensated for overpaying for community facilities, medical services, or compulsory insurance services.
To “check” whether they are eligible to receive compensation, website visitors are asked to enter into a special form the last digits of a document and their first and last names. It doesn’t matter what data the user indicates; the website displays a message confirming their eligibility to receive a payment, and the cybercriminals ask the user to transfer a small amount of money for this purpose.
During May 2018, Doctor Web added 1,388,093 URLs into the Dr.Web database of non-recommended sites.
| April 2018 | May 2018 | Dynamics |
|---|---|---|
| + 287,661 | + 1,388,093 | + 382.5% |
Other events in information security
In May, Doctor Web virus analysts examined several new modifications of Trojans that steal confidential information. One of them was dubbed Trojan.PWS.Stealer.23370. It scans the discs of the infected device, searching for saved passwords and cookie files of Chromium-based browsers. In addition, this Trojan steals information from Telegram and FileZilla FTP client and also copies images and office documents according to a predetermined list. The Trojan packs the obtained data into an archive and saves it to Yandex.Disk.
Another modification of this spying Trojan was named Trojan.PWS.Stealer.23700. It steals passwords and cookie files from Google Chrome, Opera, Yandex.Browser, Vivaldi, Kometa, Orbitum, Comodo, Amigo and Torch. It also copies the SSFN files from the config subfolder of Steam and other data required to access the Telegram account. In addition, the spyware creates copies of images and documents stored on the Windows Desktop. All the stolen information is packed into an archive and loaded into the cloud storage pCloud.
The third stealer modification was named Trojan.PWS.Stealer.23732. This Trojan consists of several components. One of them is a spyware module, and, like its predecessors, it was written in Python and transformed into an executable file. It steals confidential information. All the other Trojan components are written in Go. One of them scans discs, searching for folders in which browsers are installed, and another packs stolen data into archives and loads them into pCloud storage.
For more information on the distribution methods of these malicious programs, refer to this article on our website.
Malicious and unwanted programs for mobile devices
In May, a considerable number of new malicious and potentially dangerous programs for mobile devices were detected. Many of them were being spread via the official program catalog for Android. In early May, Doctor Web virus analysts detected Android.Click.248.origin on Google Play. It loaded fraudulent websites on which users subscribed to expensive services. Later, our specialists detected Android.FakeApp on Google Play. It followed links it received from virus writers and loaded websites, artificially inflating their traffic. Also on Google Play, malicious programs from the Android.HiddenAds family were being spread. These programs are designed to display advertisements. Also among the Trojans detected in May were the spyware Trojans Android.Spy.456.origin and Android.Spy.457.origin, which are used to spy on users. In late May Doctor Web virus analysts updated the virus database to include a signature for detecting the commercial spyware program Program.Onespy.3.origin.
The following are the most notable May events related to mobile malware:
- The detection of new Android Trojans on Google Play;
- The detection of a new version of a potentially dangerous spyware program for Android.
Find out more about malicious and unwanted programs for mobile devices by reading our special overview.