Trojan.Gapz.1 infecting Windows in a new manner
Real-time threat news | All the news | Virus alerts
November 12, 2012
Trojan.Gapz.1 is capable of running under both 32-and 64-bit versions of Windows. During the infection process, the Trojan checks which version of the system is being used on the infected computer. Accordingly, the very installation procedure of this malicious program varies depending on the platform. The Trojan is also able to actively exploit the vulnerabilities of a number of system components, which allows it to execute a specially generated code—something very unusual for this class of threats.
The bootkit installer attempts to bypass the UAC (User Accounts Control), which prevents an unauthorized launch of executable files in the system through the exploitation of Windows graphics’ vulnerabilities. It is notable that similar technology (the use of a specially prepared Dexter Regular font) was applied in the once-famous Trojan.Duqu, a trojan that was thoroughly studied by experts of various anti-virus companies.
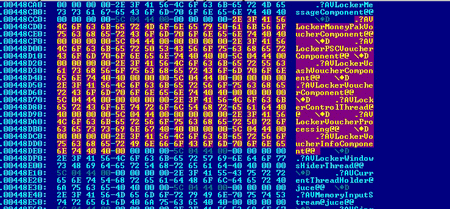
Trojan.Gapz.1 then analyzes the structure of the infected computer's hard drive, creates a special image, and writes it in the reserved sectors of the disk. After that, the Trojan modifies one field in the MBR, thus making the boot loader load and run a malicious application.
Actually, the Trojan.Gapz.1 rootkit is a core of a complex malware whose main objective is to create a suitable environment for the rest of the Trojan components to be downloaded. Once launched, Trojan.Gapz.1 loads a binary image that contains a set of several modules and a configuration data unit. These modules are blocks of a specially assembled code which, when being executed, interacts with the rootkit's own API. The features and functions of these components are still not fully understood; for example, one of the modules can connect to a remote command center and download executable files from there. Thus, Doctor Web specialists have recorded the downloading of a malicious application designed to operate with the UCash payment system.
At the moment, research of Trojan.Gapz.1 is still in progress. Special tools to cure this threat have been added to Dr.Web anti-virus products, which is why this rootkit is not a serious risk to our users.