Trojan targeted dozens of games on Google Play
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
January 28, 2016
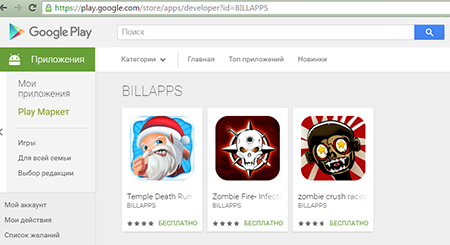
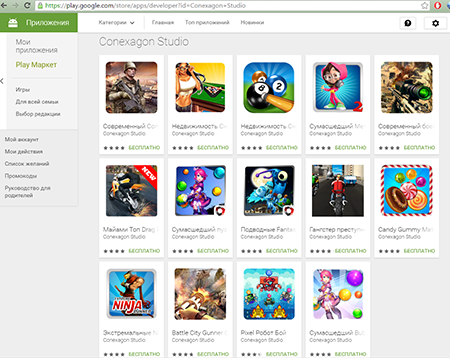
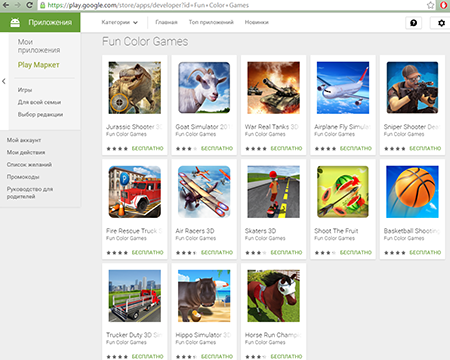
The Trojan was incorporated into more than 60 games that were then distributed via Google Play in the names of more than 30 game developers, including Conexagon Studio, Fun Color Games, BILLAPPS, and many others. Although Doctor Web has already informed Google about this incident, to this day, the affected applications are still available on Google Play. It is recommended that you do not download games from the store to devices without anti-virus software in the next few hours.
At first glance, these affected games look similar to numerous such-like applications; and they are games indeed, with just one difference—while a user is playing a game, the Trojan is performing its malicious activity.
Android.Xiny.19.origin sends the following information on the affected device to the server: its IMEI identifier and MAC address, a version and a current language of the operating system, and mobile network operator name. What is more, cybercriminals get information about accessibility of a memory card, name of an application, which the Trojan is incorporated into, and whether this application is in the system folder.
However, the main threat of Android.Xiny.19.origin lies in its capability to download and dynamically run arbitrary apk files upon cybercriminals' command. However, the way it is carried out is rather unique. To masquerade the malicious program, virus makers hide it in specially created images by applying steganography. Unlike cryptography that is used for encryption of source information, which may arouse suspicion, steganography is applied to hide information covertly. Virus makers presumably decided to complicate the detection procedure expecting that security analysts would not pay attention to benign images.
Upon receiving a necessary image from the server, Android.Xiny.19.origin retrieves a hidden apk file with the help of a special algorithm and then executes it.
Android.Xiny.19.origin can perform other malicious functions, such as to download and prompt a user to install different software, or to install and delete applications without the user’s knowledge if root access is available on the device. Besides, the malicious program can display annoying advertisements.
Android.Xiny.19.origin is not yet able to gain root privileges. However, given that the Trojan is mainly designed to install software, it can download a set of exploits from the server in order to gain root access to the device for covert installation or deletion of applications.
Doctor Web security researchers would like to warn users against installing dubious applications even if they are published on Google Play. Dr.Web for Android successfully detects all the known applications containing Android.Xiny.19.origin, so they do not pose any threat to our users.