Bunch of Trojans provide access to compromised computers
Real-time threat news | Hot news | All the news | Virus alerts
November 11, 2015
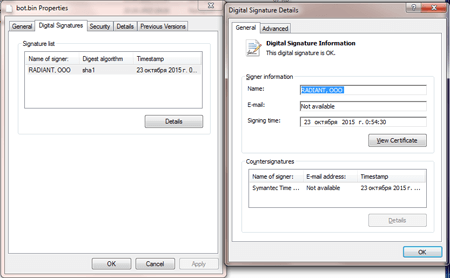
With the help of Exploit.CVE2012-0158.121, cybercriminals managed to distribute a whole pack of malicious programs that was named BackDoor.RatPack and was disguised as an RTF document. Once the document was opened, a malicious file was decrypted and saved to the victim's computer. It should be noted that the file, which is, in fact, an installer, has a valid digital signature (like almost any other file from BackDoor.RatPack).
Once launched, the installer scans the system for virtual machines, monitoring programs, and debuggers. Then it initiates a search for online banking applications of several Russian financial organizations. If all the checks are successful, the installer connects to a remote server and downloads and runs another installer in NSIS (Nullsoft Scriptable Install System) format that contains a number of executable files and several password-protected archives. The second installer extracts executable files and runs them.
The installer payload bears a modification of a shareware program called Remote Office Manager—Doctor Web security researchers have detected at least three versions of this program that differ in configuration settings. By intercepting a number of system functions, the malicious program is able to conceal the tool's shortcuts in the Windows taskbar and notification area preventing the user from detecting the program. One can assume that cybercriminals employ BackDoor.RatPack to steal banking information and other confidential data by remotely controlling the compromised machine.
Signatures of all malicious files belonging to BackDoor.RatPack have been added to Dr.Web virus databases, and, therefore, they pose no threat to our users.