Dangerous Android Trojan “hides” from anti-viruses
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
March 18, 2015
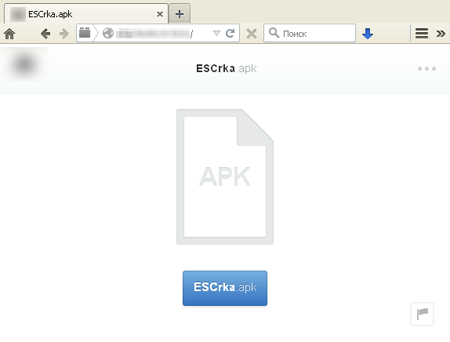
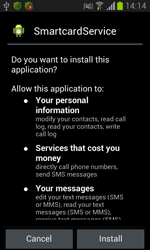
A new Trojan for Android, named Android.Titan.1, is intended to attack South Korean users and is distributed by cybercriminals using unsolicited SMS messages. These short messages contain information about allegedly delayed mail and a link to obtain detailed information about a so-called “problem”. In fact, this link leads to a page of one of the popular file-sharing services, where virus writers placed Android.Titan.1. If potential victims visit the specified web address, instead of the expected information, the apk file of the malicious application will be automatically downloaded on their mobile devices. However, to infect the operating system, the Trojan needs incautious users to perform its installation.
After successful installation, Android.Titan.1 creates a shortcut on the home screen of the mobile device and expects to be launched by the user of the infected Android handheld. After the first successful launch, the malicious application removes its previously created icon and continues to run in the background. At the same time, the Trojan removes victim's last SMS dialogue stored in the device memory. In most cases, this SMS dialogue is the spam message that provided the Trojan with access to the target device. From then on, Android.Titan.1 operates without user intervention and starts by itself, loading at startup.
 |
 |
Android.Titan.1 operates with the help of several malicious system services that are started by the Trojan as it executes. In particular, one of the services checks whether Android.Titan.1 is a default SMS Manager, and if it is not, tries to change the system settings.
Then the Trojan waits for Internet connection, connects to the command and control server and loads detailed information about the compromised mobile device, including device model, OS version, network connection, MAC address, IMEI and IMSI, as well as the mobile number of the victim.
In return, the malware can get one of the commands from the server:
- To start the service that searches and kills all processes related to the com.kakao.talk application
- To start the service that spoofs phone numbers in the phone book
- To change the device's mode dial (silent, vibro call or ordinary) and set the dial volume level
- To start the service that sends SMS messages with parameters specified in a command
- To start the service that calls to a specified number (during the call, the screen of the device stays inactive similarly to standby mode)
- To send the information (names and corresponding phone numbers), that is stored in the contact list, to the server
- To start the service that demonstrates a specified text and accompanying images in the notification bar
With the ability to cover phone calls as well as periodically monitor the activity of the infected device's screen, Android.Titan.1 enables cynercriminals to instruct the Trojan to make a call when the infected device is kept in standby mode for a long time. Upon that, just after the start of the phone call, the screen is locked again, so the user is unlikely to have any suspicion that cybercriminals make an unwanted call.
Android.Titan.1 is able to monitor all inbound SMS messages and hide from the user those ones that match the virus writers' criteria. In addition, the command and control server receives detailed information about all inbound SMS including information about the sender, date and time of sending as well as their contents. If it is not possible to send the information, the malicious program places the received data in a special database stored on the device locally, and waits for the Internet connection to load the queued information to the server.
In addition, Android.Titan.1 implements another dangerous feature. Every minute the Trojan checks whether the user makes a call. If so, the call is recorded into the amr file and the result is stored in Trojan’s working directory. In future, this file together with the detailed information about the user's calls is uploaded to a remote server, and if there is no connection to the Internet, it is queued as in the case of intercepted short messages. The Trojan can also block inbound or outbound calls from certain numbers, answer to the calls and remove them from the system log.
The main feature of this Trojan is that its basic functionality is implemented as a separate Unix library (detected as Android.Titan.2), while the majority of known malicious programs for Android usually contain such features in a standard executable dex-file. In the case with Android.Titan.1, dex-file is used only as an auxiliary component that contains the minimum necessary features for Trojan's operation. Such technique is quite rare when creating malicious application for Android, and because of that, many anti-virus programs are unable to detect this dangerous application.
According to Doctor Web security researchers, Android.Titan.1 is still under development because it contains a number of bugs and some of its features remain unimplemented. Therefore, we cannot exclude the occurrence of even more functional version of this dangerous malicious application in future.
Doctor Web security researchers informed the tech support of the file-sharing service where the Trojan was placed, and now the page from which it was downloaded is unavailable. However, nothing prevents the cybercriminals from hosting the Trojan at any similar site. Dr.Web for Android and Dr.Web for Android Light successfully detect and remove Android.Titan.1, so the users of Doctor Web mobile anti-virus solutions are under the reliable protection.