New Trojan fakes search results
Real-time threat news | All the news | Virus alerts
January 15, 2013
When launched in an infected system, BackDoor.Finder creates a copy of itself in the current user's % APPDATA% folder and makes corresponding changes in the branch of the Windows registry responsible for application startup. After that this malware injects its code into all running processes. If it manages to inject its code into Internet Explorer, Mozilla Firefox, Maxtron, Chrome, Safari, Mozilla, Opera, Netscape or Avant processes, it will intercept WSPSend, WSPRecv and WSPCloseSocket routines.
Then BackDoor.Finder generates up to 20 control server domain names and will send encrypted queries to each server, one after another. When a user of an infected machine attempts to search the Web via google.com, yahoo.com, bing.com, ask.com, search.aol.com, search.icq.com, search.xxx, www.wiki.com, yandex.com, or www.alexa.com, the query is transmitted to a malicious controlling server which returns a configuration file with a list of URLs that will be used to redirect the browser to malignant sites. As a result, instead of a search results page, a list of sites specified by criminals will be displayed to the user.
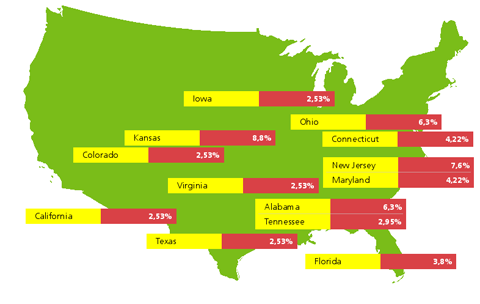
Doctor Web's analysts managed to work out the routine employed by BackDoor.Finder to generate command server names; they registered several fake servers to gather more information about the malware. It turned out that the malware is most widely spread in the U.S. where Kansas has become the undisputed leader, followed by New Jersey. Ohio and Alabama occupy third place. The smallest number of infections by BackDoor.Finder is found in Utah and Michigan.
This malicious program has been added to the Dr.Web virus databases and poses no danger to machines running Doctor Web anti-virus products.