March 2009 virus activity review from Doctor Web
Virus reviews | All the news
April 2, 2009
Doctor Web presents a review of activities of malicious programs in March 2009. The last month saw increased usage of malware by online fraudsters, growing botnets with their creators applying more aggressive techniques to expand networks of zombie machines and spammers advertising their own business.
Botnets
New techniques introduced by virus makers to increase efficiency of Tdss and Shadow botnets made them main nuisances in March. Time-tested ways of spreading malware on removable data-storage devices and over network resources worked as well as before showing that most users didn’t follow security recommendations of anti-virus vendors.
On the other hand Doctor Web does its best to keep users and technical specialists updated on latest threats and provides them with Internet security tips. At the same time creators of botnets also know that certain vulnerabilities if open allow security experts and administrators to suggest that the system has been compromised. A new feature of Win32.HLLW.Shadow.based based enables it to close certain vulnerabilities in infected systems making it harder to detect if a system has been compromised.
The latest modification of Win32.HLLW.Shadow.based also features a domain name generator that uses a certain algorithm to generate 50 000 domain names every 24 hours and picks out 500 domains from the list to look for updates. Now it is much harder to disrupt operation of the botnet since one can’t find out addresses of all malicious servers and force their shutdown lawfully.
BackDoor.Tdss that expands the Tdss botnet uses other spreading and disguise techniques. Each subsequent version of the backdoor features more sophisticated rootkit technologies that allow it to evade detection and disrupt operation of anti-virus file monitors. To get into a system it exploits one of Windows vulnerabilities or can be downloaded and launched as a video codec by a user. Even though the codec trick has been known for quite a while it still remains efficient.
Cyber fraud
Once again an increased number of fraud schemes involving use of malware was registered in March.
Customers of sRussian banks using ATMs were worried by the news about viruses that compromised ATMs of certain Russian banks. The malicious programs collected information stored on credit cards and account information sent by the bank to the ATM upon a request of the customer.
The name of the program in the Dr.Web classification of malware is Trojan.Skimer. The Dr.Web virus database contains entries for ten modifications of the Trojan. It should be noted that banks received instruction on how to close the vulnerability from the manufacturer of ATMs before the Trojan was discovered by anti-virus vendors. See the detailed description of Trojan.Skimer in the virus library at the web-site of Doctor Web.
Even though anti-virus vendors provide detailed information about fake anti-viruses, cyber-criminals still implement schemes tricking users into paying for a program that actually does nothing. Now when elements of professional web-design are implemented on bogus web-sites spreading fake anti-viruses, the sites tend to look more and more like web-resources of real anti-virus vendors. Such fake anti-viruses as Antivirus XP 2008 are known to almost every Internet user.
Popularity of social networking web-sites in Russia provides virus makers with infinite opportunities. Another Trojan discovered in March was spread as a piece of software that would enable users of a social network to increase their rating.
Spam
The main subject of spam messages in the last month was advertisement of spam mailings. Probably the offer exceeded demand on the spam market. Apart from self-advertising spam messages also promoted healthcare products, expensive new mobile phones at great discounts and replicas of luxury watches. Some messages urged users to participate in conferences and take advantage of various training programmes.
Malicious programs or links to malicious web-sites provided by spam messages became smaller in number in recent months. Absence of mass spam mailings related to spread of malware caused different side-effects. Programs that usually didn’t spread via e-mail could get top positions in anti-virus statistics. It happened because users of compromised machines added infected files to attachments they sent via e-mail.
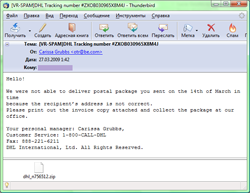
As for mailings that aimed to spread malware, virus analysts of Doctor Web registered a short-term mailing (several hours) of Win32.HLLW.Brutus.3 and a mailing of Trojan.PWS.Panda.114 that lasted a bit longer but used smaller amount of mail traffic. The latter came with a message supposedly from DHL. It informed a user that his message could not be delivered due to invalid delivery address. A user was offered to visit a DHL office with a printed invoice attached to the message. Of course the attached invoice was nothing more than a malicious file.
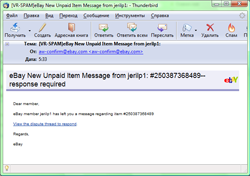
Even though the number of phishing messages in March was a bit lower than usual, virus analysts of Doctor Web registered several phishing attacks targeting customers of eBay.
 |
 |
Malicious files detected in mail traffic in March
| 01.03.2009 00:00 - 01.04.2009 00:00 | ||
| 1 | Win32.HLLW.Shadow.based | 5348 (16.27%) |
| 2 | Win32.Virut | 3942 (11.99%) |
| 3 | Win32.HLLM.MyDoom.based | 3887 (11.83%) |
| 4 | Trojan.MulDrop.13408 | 1998 (6.08%) |
| 5 | Trojan.MulDrop.18280 | 1709 (5.20%) |
| 6 | Win32.HLLM.Netsky | 1629 (4.96%) |
| 7 | Win32.HLLM.Beagle | 1252 (3.81%) |
| 8 | Trojan.MulDrop.16727 | 1137 (3.46%) |
| 9 | Win32.HLLW.Brutus.3 | 1134 (3.45%) |
| 10 | Win32.HLLW.Gavir.ini | 964 (2.93%) |
| 11 | Win32.HLLM.Alaxala | 901 (2.74%) |
| 12 | Win32.HLLM.Netsky.35328 | 511 (1.55%) |
| 13 | Win32.HLLM.MyDoom.33808 | 472 (1.44%) |
| 14 | Trojan.MulDrop.19648 | 443 (1.35%) |
| 15 | BackDoor.Poison.78 | 403 (1.23%) |
| 16 | Win32.HLLM.MyDoom.44 | 393 (1.20%) |
| 17 | Trojan.MulDrop.30412 | 379 (1.15%) |
| 18 | Trojan.MulDrop.17431 | 351 (1.07%) |
| 19 | Trojan.MulDrop.30415 | 351 (1.07%) |
| 20 | Win32.HLLW.Sinfin | 339 (1.03%) |
| Total scanned: | 407,512,378 |
| Infected: | 32,867 (0.0081%) |
Malicious files detected on user machines in March
| 01.03.2009 00:00 - 01.04.2009 00:00 | ||
| 1 | Win32.HLLW.Gavir.ini | 1292200 (11.60%) |
| 2 | Win32.HLLW.Shadow.based | 713002 (6.40%) |
| 3 | Win32.Virut | 590384 (5.30%) |
| 4 | Win32.Virut.5 | 581332 (5.22%) |
| 5 | DDoS.Kardraw | 436270 (3.91%) |
| 6 | Win32.HLLW.Autoruner.5555 | 426000 (3.82%) |
| 7 | Trojan.DownLoader.42350 | 409721 (3.68%) |
| 8 | Win32.Alman | 393549 (3.53%) |
| 9 | Trojan.Starter.881 | 253295 (2.27%) |
| 10 | Win32.Sector.17 | 246519 (2.21%) |
| 11 | BackDoor.IRC.Itan | 245957 (2.21%) |
| 12 | Exploit.PDF.56 | 235196 (2.11%) |
| 13 | Win32.Parite.1 | 176361 (1.58%) |
| 14 | Win32.HLLP.Neshta | 163406 (1.47%) |
| 15 | Win32.HLLM.Lovgate.2 | 151434 (1.36%) |
| 16 | Win32.HLLM.Generic.440 | 146493 (1.31%) |
| 17 | Win32.HLLP.Whboy | 142174 (1.28%) |
| 18 | Win32.HLLW.Autoruner.6293 | 139671 (1.25%) |
| 19 | Trojan.PWS.Wsgame.4983 | 116799 (1.05%) |
| 20 | Win32.HLLW.Autoruner.6126 | 115798 (1.04%) |
| Total scanned: | 83,190,605,938 |
| Infected: | 11,144,291 (0.0134%) |