The New Version of Trojan.Hosts To Extort Money From Foreign Users
Real-time threat news | All the news | Virus alerts
May 23, 2012
First of all, Trojan.Hosts.5858 downloads itself on computers already infected with BackDoor.Andromeda family malware which is capable of downloading executables from malicious sites. Trojan.Hosts.5858 might also be downloaded on an infected computer together with other Trojans, such as Trojan.Spambot.11349 and BackDoor.IRC.Aryan.1.
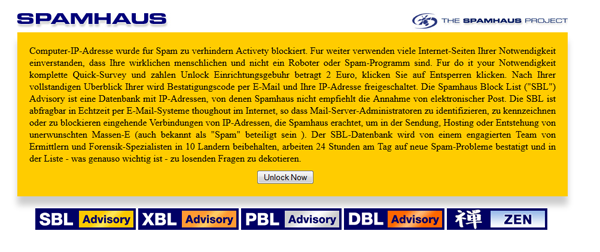
Once it runs itself in the operating system, Trojan.Hosts.5858 modifies the hosts file located in the Windows system folder and responsible for the translation of website network address into their DNS names. As a result, when trying to visit a popular online resource, such as Facebook, Google, Yahoo, etc., a browser is automatically redirected to a webpage specially created by attackers that displays a message in German that Internet access is blocked. To "unlock" the system, a user is prompted to provide virus writers with its banking card details.
The program's signature has been added to the Dr.Web virus databases. The Trojan.Hosts.5858 can be successfully removed from the system during scanning. If a browser still displays a webpage containing the requirement to pay after the computer has been scanned, the user is recommended to re-scan its computer with a free curing utility called Dr.Web CureIt!, or edit the Windows\System32\Drivers\etc\hosts file contents by deleting all unnecessary entries from there.