Doctor Web: Android.Xiny Trojans have learned how to infect system processes
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
September 21, 2016
Anti-virus specialists have been acquainted with the Android.Xiny Trojans since March 2015. As Doctor Web announced earlier, virus makers actively distribute them through popular websites offering downloadable software and even through official application stores like Google Play.
Once saved to smartphones and tablets, Android.Xiny Trojans attempt to acquire root privileges so that they can silently download and install various software programs. Moreover, they can display annoying advertisements. One key feature of these malicious programs is that they employ an innovative mechanism that protects them from being deleted. The mechanism is based on the fact that the Trojan’s apk files are made to be immutable. However, cybercriminals kept improving Android.Xiny Trojans and gave them the ability to inject themselves into system applications in order to launch various malicious plug-ins from them.
One of these upgraded Trojans examined by Doctor Web security researchers was named Android.Xiny.60. It gets installed in a system directory by other programs belonging to the Android.Xiny family. Once launched, Android.Xiny.60 extracts several malicious components from its resource folder and copies them to system directories.
- /system/xbin/igpi;
- /system/lib/igpld.so;
- /system/lib/igpfix.so;
- /system/framework/igpi.jar.
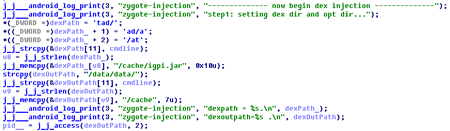
Next, using the igpi module (dubbed Android.Xiny.61), the Trojan injects the igpld.so library (dubbed Android.Xiny.62) into the system application processes of Google Play (com.android.vending) and Google Play Services (com.google.android.gms, co.google.android.gms.persistent). In addition, this malicious module can also be injected into the zygote process, but this feature isn’t used in the current version of the Trojan.
Once the zygote process is infected, Android.Xiny.62 starts tracking the launch of any new applications. As a result, if the Trojan detects a newly launched process, it injects the igpi.jar malicious module (Android.Xiny.60) into it. This very same module is also injected after system processes of Google Play and Google Play Services applications have been infected.
The igpi.jar module’s main job is to download cybercriminal-specified plug-ins and launch them in the infected environment. The module monitors a mobile device’s status and, when certain system events occur (e.g. home screen activity, change in network connection, charger usage, etc.), it connects to the command and control server and sends it the following information about the infected device:
- IMEI
- IMSI
- MAC address of the network adapter
- OS version
- Mobile device model;
- Current system language
- Application package name
In response, Android.Xiny.60 can download and launch malicious plug-ins that work as part of the infected app. Security analysts have not detected distributions of these malicious modules yet; however, if cybercriminals create them, the Trojan’s attack will be massive. Some possible scenarios appear below.
- If Android.Xiny.60 infects a Google Play process, it will download into it the software-installation module.
- If Android.Xiny.60 infects a messenger, it will be able to intercept and send messages.
- If Android.Xiny.60 infects a banking program’s process, it will launch the required plug-in and will then be able to steal confidential information, such as logins, passwords, credit card numbers, etc., and even covertly transfer money to cybercriminal-owned bank accounts.
Doctor Web's security researchers continue to monitor Trojans belonging to the Android.Xiny family. Meanwhile, we recommend using Dr.Web for Android which successfully detects all known modifications of these malicious programs.