December 2015 mobile malware review from Doctor Web
December 25, 2015
PRINCIPAL TRENDS IN DECEMBER
- Distribution of dangerous banking Trojans
- Emergence of new SMS Trojans
- Detection of a new dangerous Trojan for iOS
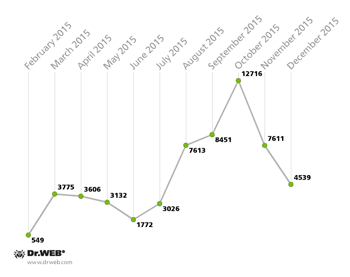
Number of entries for malicious and unwanted software targeting Android OS in Dr.Web virus database
| November 2015 | December 2015 | Dynamics |
|---|---|---|
| 16,070 | 17,610 | +6.18% |
Mobile threat of the month
In December, cybercriminals continued to distribute various modifications of a dangerous banking Trojan named Android.Zbot that was detected by Doctor Web security researchers this February. In the past month, this malicious program infected more than 4,500 mobile devices. In total, its activity was registered more than 31,000 times since being discovered.
This Trojan is distributed under the guise of benign applications and can be downloaded once a user visits fraudulent websites, or another malicious application can download it to a device. The main purpose of Android.Zbot is to steal confidential data, such as logins and passwords for online banking applications, and covertly transfer money from users’ bank accounts to cybercriminals’. For more information about this Trojan, refer to the article published by Doctor Web.
Banking Trojans for Android
In addition to Android.Zbot, other banking Trojans posed a serious threat to Android devices users in December. In particular, this month, the Doctor Web virus database was updated with several new entries for modifications of the Android.BankBot and Android.Banker families.
The number of entries for banking Trojans of the Android.Banker family in Dr.Web virus database:
| November 2015 | December 2015 | Dynamics |
|---|---|---|
| 305 | 316 | +3.6% |
The number of entries for banking Trojans of the Android.BankBot family in Dr.Web virus database:
| November 2015 | December 2015 | Dynamics |
|---|---|---|
| 151 | 163 | +8% |
SMS Trojans
As before, Android devices users are threatened by numerous SMS Trojans that send messages to premium numbers and subscribe users to chargeable services without their victims' knowledge. In December, a large number of suchlike malicious programs were detected.
The number of entries for SMS Trojans of the Android.SmsSend family in the Dr.Web virus database
| November 2015 | December 2015 | Dynamics |
|---|---|---|
| 6,884 | 7,292 | +5.93% |
Trojans for iOS
Cybercriminals become more and more interested in targeting iOS system. Thus, in the past month, yet another Trojan for Apple devices, IPhoneOS.Trojan.TinyV, was registered. This malicious program was distributed via modified harmless applications and was downloaded to a device once a user visited websites related to mobile software. The Trojan was installed on a jailbroken Apple device and, upon receiving a command from the server, was able to covertly download and install various software and modify the hosts file. As a result, users could be redirected to non-recommended websites.
[% END %]