October 2015 virus activity review from Doctor Web
October 30, 2015
October proved to be a quiet month in terms of information security events. However, over the course of the second autumn month, a number of popular Internet resources still fell victim to attacks of cybercriminals—the hacked websites were used to distribute a dangerous program disguised as an anti-virus utility created by a well-known developer. Moreover, October witnessed emergence of new Trojans for Android and iOS—in particular, Android.BankBot.80.origin that was spread as an official online banking application of a Russian financial organization and IPhoneOS.Trojan.YiSpecter.2 designed to display advertisements and stealthily download other programs to compromised devices.
PRINCIPAL TRENDS IN OCTOBER
- A number of websites got hacked by cybercriminals to distribute malware
- Emergence of a new Trojan designed to perform web injections
- Distribution of new malicious programs for Android
Threat of the month
In the middle of October, Doctor Web security researchers registered several cases of websites being hacked by cybercriminals. Among those resources was a webpage dedicated to one popular Russian TV series. If the user opened the link to the website from Google search results, and if certain conditions were met, a new tab with a webpage opened in the browser window. A special malicious script incorporated into that webpage by cybercriminals prevented the user from closing it. If the victim pressed any key or clicked anywhere in the window, an annoying dialog was displayed prompting the victim to install a browser extension supposedly created by an anti-virus developer.
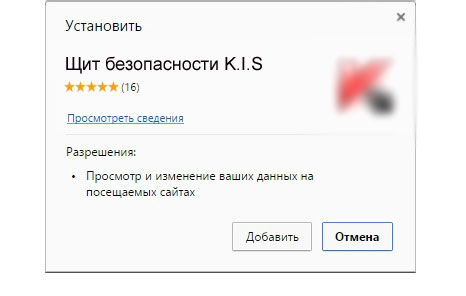
The extension detected by Dr.Web as Trojan.BPLug.1041 serves the purpose of injecting arbitrary content into webpages browsed by the user. Moreover, on all websites, the malicious program blocks third-party advertisements from any domains, except for those listed in the configuration file. If the user logs in to the Odnoklassniki (“Одноклассники”) social networking website, Trojan.BPLug.1041 will try to provide a certain application with access to the API of this website on behalf of the user. As a result, the victim's data can be used to promote groups, send spam messages, and influence some poll results. For more information regarding this malicious program, refer to the news article published by Doctor Web.
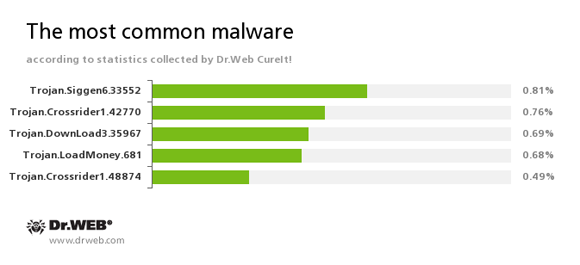
According to the statistics gathered by Dr.Web CureIt!
Trojan.Siggen6.33552
A malicious program designed to install other dangerous software on the infected computer.Trojan.Crossrider1.42770
A Trojan designed to display various advertisements to Internet users.Trojan.DownLoad3.35967
A Trojan that can download other malicious programs from the Internet and install them on the infected computer.Trojan.LoadMoney
A family of downloader programs generated by servers belonging to the LoadMoney affiliate program. These applications download and install unwanted software on the victim's computer.
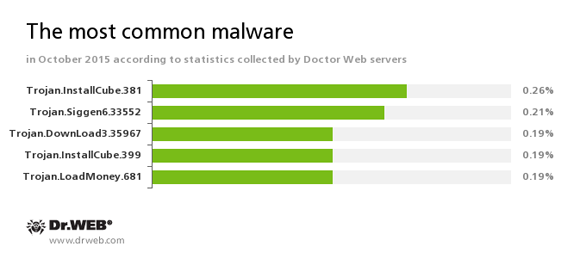
According to Doctor Web statistics servers
Trojan.InstallCube
A family of downloader programs designed to install unwanted and useless applications on the user’s computer.Trojan.Siggen6.33552
A malicious program designed to install other dangerous software on the infected computer.Trojan.DownLoad3.35967
A Trojan that can download other malicious programs from the Internet and install them on the infected computer.Trojan.LoadMoney
A family of downloader programs generated by servers belonging to the LoadMoney affiliate program. These applications download and install unwanted software on the victim's computer.
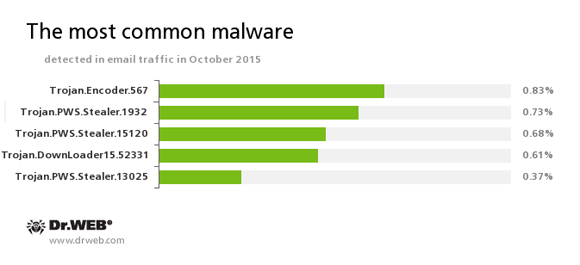
Statistics concerning malicious programs discovered in email traffic
Trojan.Encoder.567
A malicious program belonging to the family of encryption ransomware Trojans that encrypt files and demand a ransom for decryption of compromised data. This program can encrypt important user files, for example, of the following types: .jpg, .jpeg, .doc, .docx, .xls, xlsx, .dbf, .1cd, .psd, .dwg, .xml, .zip, .rar, .db3, .pdf, .rtf, .7z, .kwm, .arj, .xlsm, .key, .cer, .accdb, .odt, .ppt, .mdb, .dt, .gsf, .ppsx, .pptx.Trojan.PWS.Stealer
A family of Trojans designed to steal passwords and other confidential information stored on the infected computer.Trojan.DownLoader15.52331
A Trojan that can download other malicious programs from the Internet and install them on the infected computer.
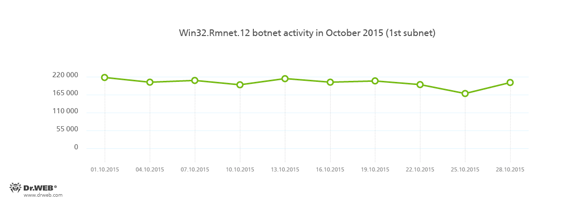
Botnets
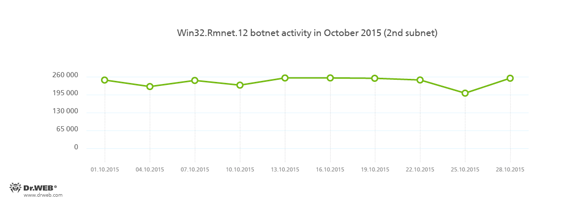
Doctor Web security researchers continue to monitor botnets created by cybercriminals using the Win32.Rmnet.12 file infector. The average daily activity of these botnets is shown in the following graphs:
Rmnet is a family of viruses spread without any user intervention. They can embed content into loaded webpages (this theoretically allows cybercriminals to get access to the victim's bank account information), steal cookies and passwords stored by popular FTP clients, and execute other commands issued by cybercriminals.
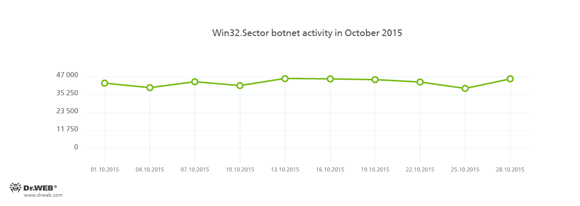
The botnet consisting of computers infected with Win32.Sector is also still active. Its average daily activity can be seen in the following picture:
The malware can perform the following actions:
- Download various executable files via P2P networks and run them on infected machines.
- Inject its code into running processes.
- Prevent some anti-viruses from operating and block access to the websites of their respective developers.
- Infect files on local disks, removable media (where the malware creates the autorun.inf file during the infection process), and in shared folders.
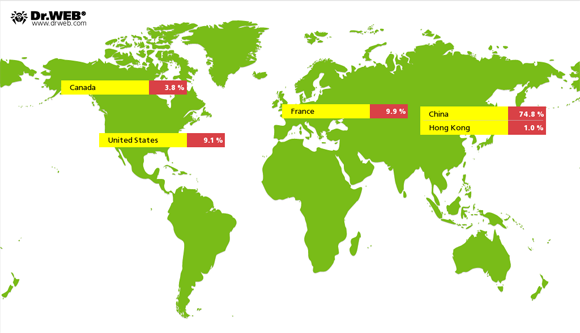
In October, cybercriminals controlling the Linux.BackDoor.Gates.5 botnet became considerably less active—in comparison with the previous month, the number of attacked IP addresses decreased by 33.29 per cent and was estimated 5,051. As before, most targets of the attacks were located in China, while the second and the third places were taken by France and the United States respectively.
Encryption ransomware
The number of requests for decryption received by Doctor Web technical support service
| September 2015 | October 2015 | Dynamics |
|---|---|---|
| 1,310 | 1,471 | +12.29% |
The most common ransomware program in October 2015 was Trojan.Encoder.567.
Dr.Web Security Space 11.0 for Windows
protects against encryption ransomware
This feature is not available in Dr.Web Anti-virus for Windows
| Data Loss Prevention | |
|---|---|
 |  |
Dangerous websites
During October 2015, 264,970 URLs of non-recommended websites were added to Dr.Web database.
| September 2015 | October 2015 | Dynamics |
|---|---|---|
| +399,227 | +264,970 | -33.6% |
Online stores selling some strange items or goods of questionable quality can be usually found among Internet resources added by Doctor Web analysts to the database of non-recommended websites over the course of a month. From time to time such websites become main “heroes” of news articles issued by our company, as resourceful fraudsters never cease to amaze security researchers constantly coming up with various mind-blowing ideas for new products. Read about threads protecting from evil eye, lip enhancers, and other “magical” goods sold in online stores in the news article published by Doctor Web.
Malicious and unwanted programs for mobile devices
In October, cybercriminals continued to target mobile devices' users. In particular, at the beginning of the month, security researchers detected a new Trojan for iOS—at that, this malicious program could be installed on smartphones and tablets with or even without “jailbreak”. Moreover, yet another Trojan managed to bypass Google protection mechanisms and get into Google Play. In the middle of the month, Doctor Web specialists registered a new case of Android firmware being infected with a malicious application and, some time later, detected a new banking Trojan designed to steal money from owners of smartphones and tablets.
Among the most noticeable events related to mobile malware we can mention
- Detection of a dangerous Trojan targeting iOS devices
- Detection of yet another malicious program on Google Play
- New case of Android firmware being infected with a malicious application
- Distribution of new banking Trojans for Android
Learn more with Dr.Web
Virus statistics Virus descriptions Virus monthly reviews Laboratory-live
[% END %]