Doctor Web’s November 2023 review of virus activity on mobile devices
December 21, 2023
At the same time, malicious actors again distributed malware via Google Play. Our specialists uncovered over 20 trojan apps from the Android.FakeApp family that are used for fraudulent purposes. In addition, they found a trojan that subscribed Android device users to paid services.
PRINCIPAL TRENDS IN NOVEMBER
- A decrease in adware trojan activity
- A decrease in banking malware and spyware trojan activity
- The distribution of new malicious apps via Google Play
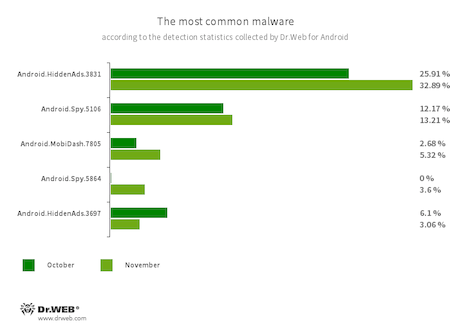
According to statistics collected by Dr.Web for Android
- Android.HiddenAds.3831
- Android.HiddenAds.3697
- Trojan apps designed to display intrusive ads. Trojans of this family are often distributed as popular and harmless applications. In some cases, other malware can install them in the system directory. When these infect Android devices, they typically conceal their presence from the user. For example, they “hide” their icons from the home screen menu.
- Android.MobiDash.7805
- A trojan that displays obnoxious ads. It is a special software module that developers incorporate into applications.
- Android.Spy.5106
- The detection name for a trojan that presents itself as modified versions of unofficial WhatsApp messenger mods. This malicious program can steal the contents of notifications and offer users other apps from unknown sources for installation. And when such a modified messenger is used, it can also display dialog boxes containing remotely configurable content.
- Android.Spy.5864
- The Dr.Web anti-virus uses this virus record to detect a trojan hidden in some third-party modifications of the WhatsApp messenger. Threat actors use this malware to spy on users. For instance, they can search files on victims’ devices and upload them to a remote server, obtain information from the phonebook, collect data about the infected device, record audio to eavesdrop on the surroundings, etc.
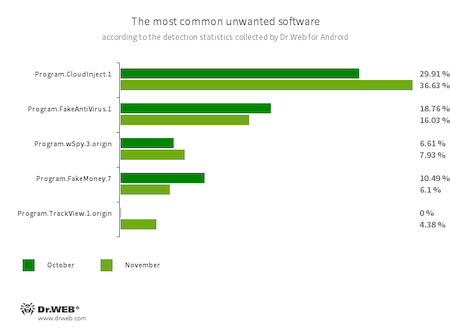
- Program.CloudInject.1
- The detection name for Android programs that have been modified using the CloudInject cloud service and the eponymous Android utility (the latter was added to the Dr.Web virus database as Tool.CloudInject). Such programs are modified on a remote server; meanwhile, the modders (users) who are interested in such modifications cannot control exactly what will be added to the apps. Moreover, these programs receive a number of dangerous system permissions. Once modification is complete, users can remotely manage these apps. They can block them, display custom dialogs, and track when other software is being installed or removed from a device, etc.
- Program.FakeAntiVirus.1
- The detection name for adware programs that imitate anti-virus software. These apps inform users of nonexistent threats, mislead them, and demand that they purchase the software’s full version.
- Program.wSpy.3.origin
- A commercial spyware app designed to covertly monitor Android device user activity. It allows intruders to read SMS and chats in popular messaging software, listen to the surroundings, track device location and browser history, gain access to the phonebook and contacts, photos and videos, and take screenshots and pictures through a device’s built-in camera. It also has keylogger functionality.
- Program.FakeMoney.7
- The detection name for Android applications that allegedly allow users to earn money by watching video clips and ads. These apps make it look as if rewards are accruing for completed tasks. To withdraw their “earnings”, users allegedly have to collect a certain sum. But even if they succeed, in reality they cannot get any real payments.
- Program.TrackView.1.origin
- The detection name for a program that allows users to be monitored via their Android devices. Malicious actors can utilize it to track a target device’s location, use the camera to record video and take photos, eavesdrop via the microphone, record audio, etc.
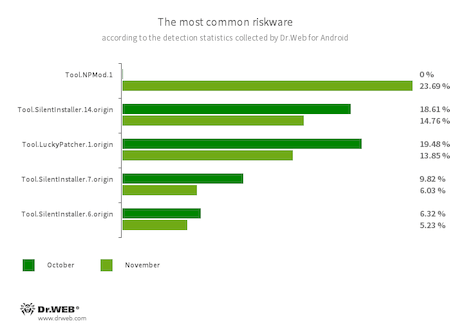
- Tool.NPMod.1
- The detection name for Android programs that have been modified using the NP Manager utility. A special module is embedded in such apps. It allows them to bypass digital signature verification once they have been modified.
- Tool.SilentInstaller.14.origin
- Tool.SilentInstaller.7.origin
- Tool.SilentInstaller.6.origin
- Riskware platforms that allow applications to launch APK files without installing them. They create a virtual runtime environment in the context of the apps in which they are integrated. The APK files, launched with the help of these platforms, can operate as if they are part of such programs and can also obtain the same permissions.
- Tool.LuckyPatcher.1.origin
- A tool that allows apps installed on Android devices to be modified (i.e., by creating patches for them) in order to change the logic of their work or to bypass certain restrictions. For instance, users can apply it to disable root-access verification in banking software or to obtain unlimited resources in games. To add patches, this utility downloads specially prepared scripts from the Internet, which can be crafted and added to the common database by any third-party. The functionality of such scripts can prove to be malicious; thus, patches made with this tool can pose a potential threat.
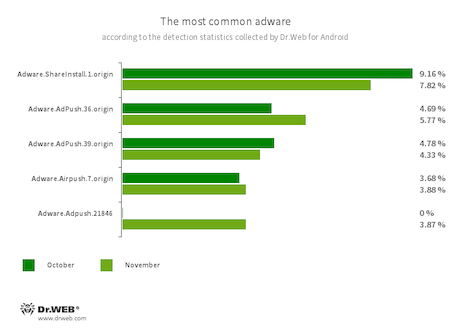
- Adware.ShareInstall.1.origin
- An adware module that can be built into Android applications. It displays notifications containing ads on the Android OS lock screen.
- Adware.AdPush.36.origin
- Adware.AdPush.39.origin
- Adware.Adpush.21846
- Adware modules that can be built into Android apps. They display notifications containing ads that mislead users. For example, such notifications can look like messages from the operating system. In addition, these modules collect a variety of confidential data and are able to download other apps and initiate their installation.
- Adware.Airpush.7.origin
- A member of a family of adware modules that can be built into Android apps and display various ads. Depending on the modules’ version and modification, these can be notifications containing ads, pop-up windows or banners. Malicious actors often use these modules to distribute malware by offering their potential victims diverse software for installation. Moreover, such modules collect personal information and send it to a remote server.
Threats on Google Play
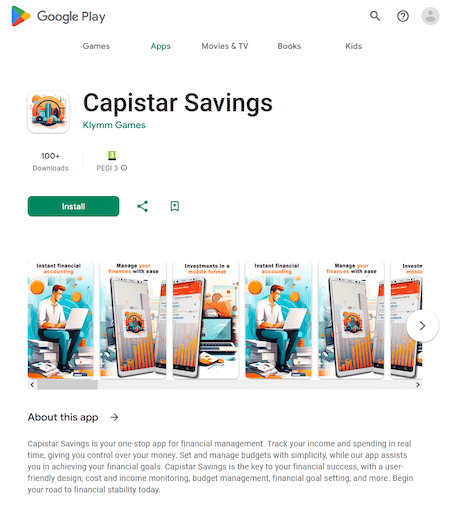
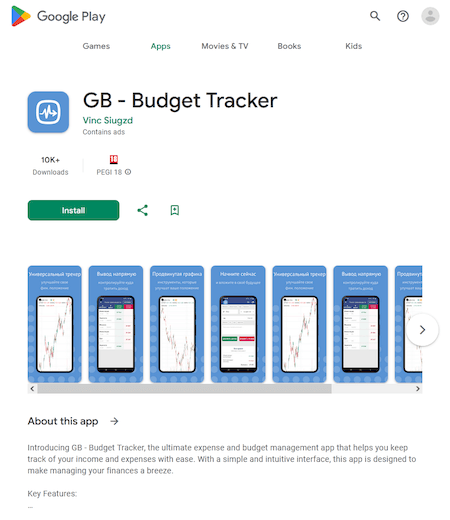
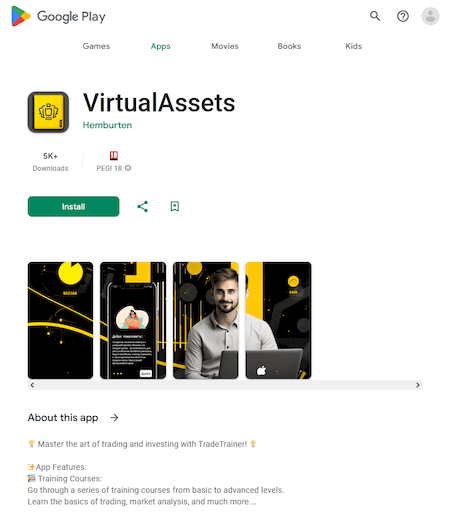
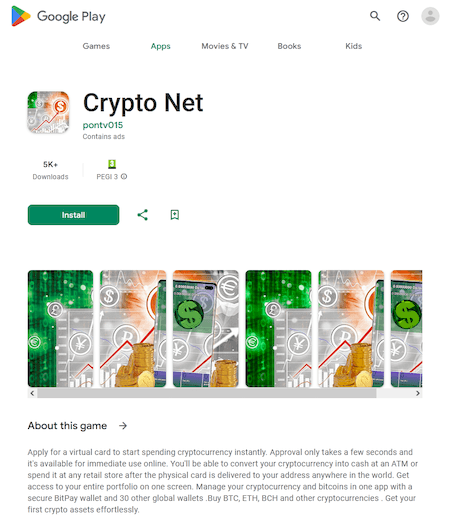
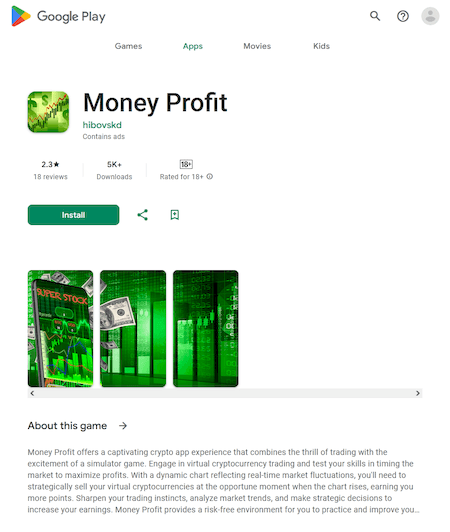
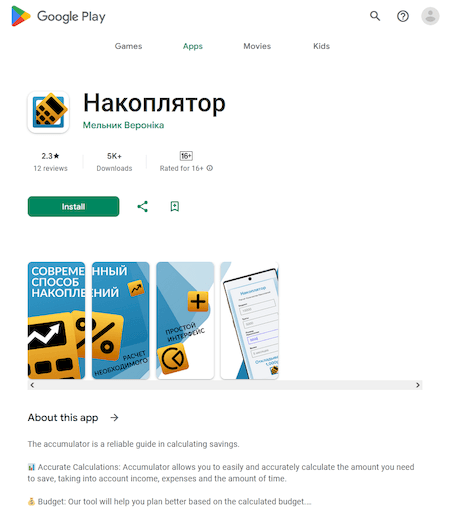
In November, Doctor Web’s virus laboratory discovered more malicious programs from the Android.FakeApp family on Google Play. Some of them were distributed under the guise of financial apps, like home accounting solutions, reference books, directories and teaching aids, programs for accessing investment services, etc. Among these were Android.FakeApp.1497, Android.FakeApp.1498, Android.FakeApp.1499, Android.FakeApp.1526, Android.FakeApp.1527, and Android.FakeApp.1536. Their main task is to load fraudulent websites where users are invited to become investors. For this, they need to provide their personal information.
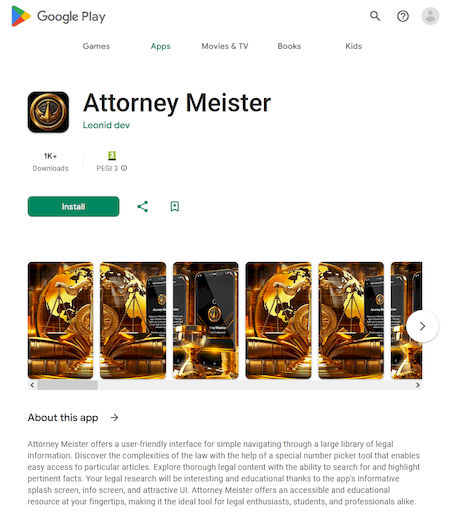
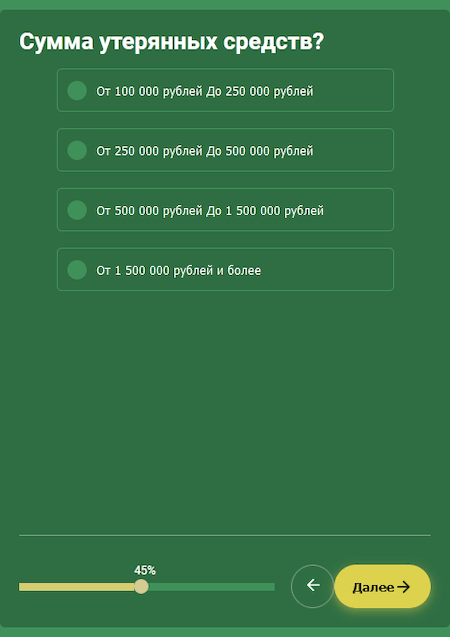
Another fake app, Android.FakeApp.1496, was hiding in a directory program for accessing legal information. It could load a website that allegedly could help victims of investment scammers get back their lost money.
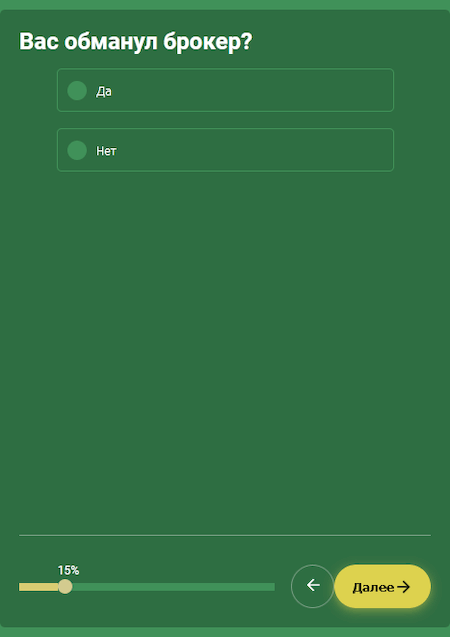
The website this trojan loaded is shown below. The visitor must answer several questions and then fill out a form to “get a free consultation with a lawyer”.
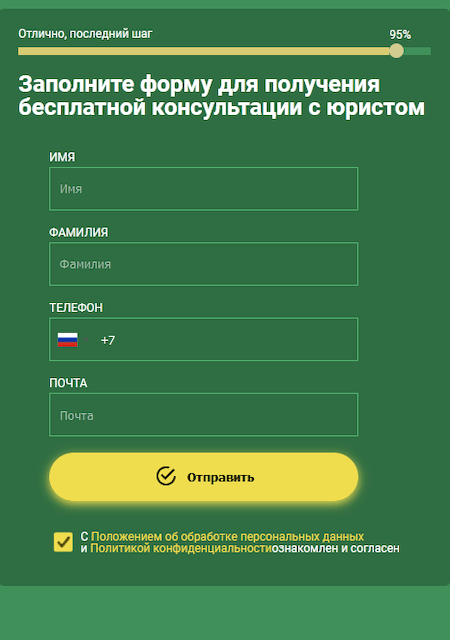
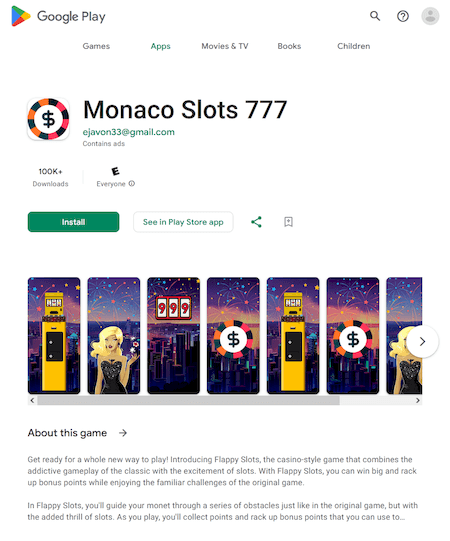
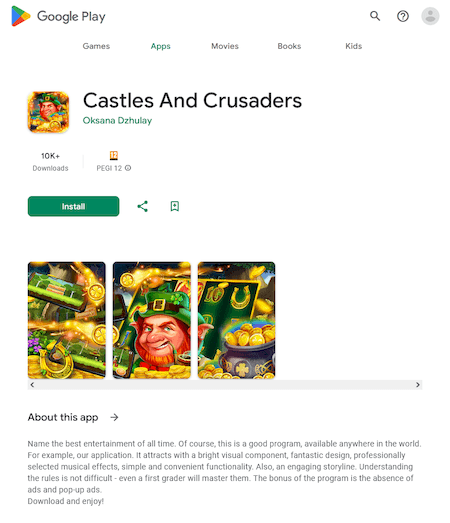
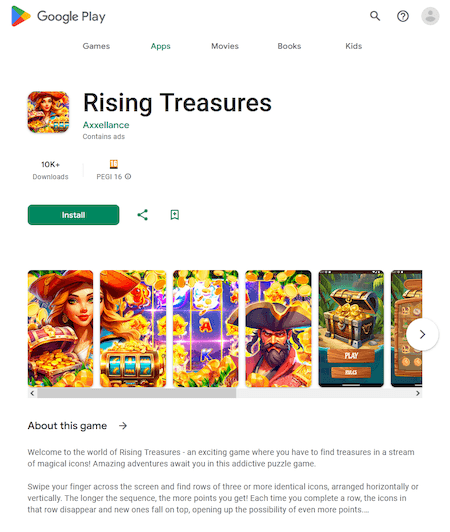
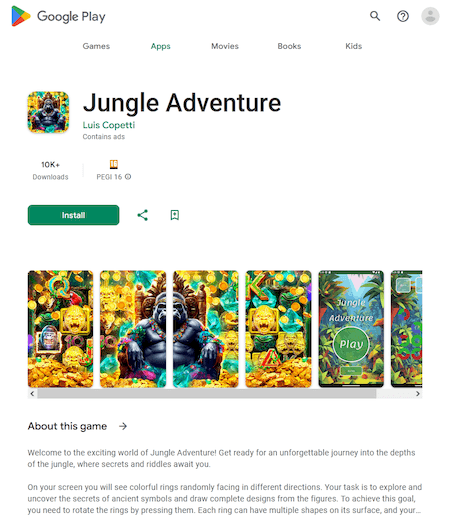
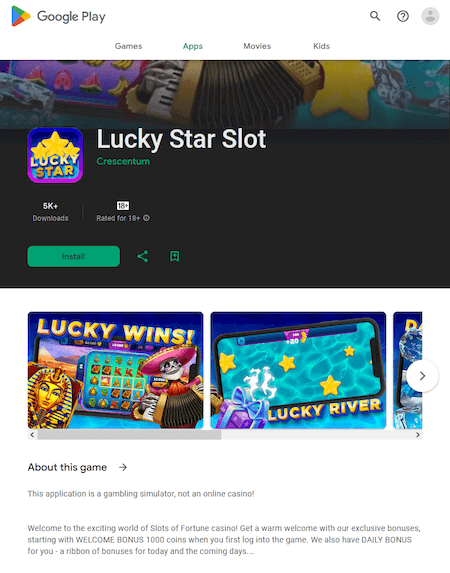
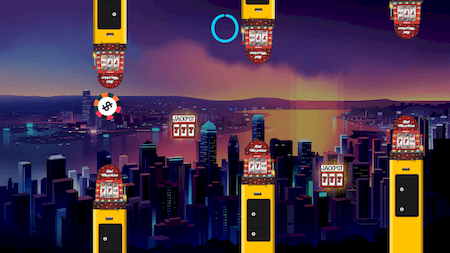
Malicious actors passed off other fake apps as games. For example, Android.FakeApp.1494, Android.FakeApp.1503, Android.FakeApp.1504, Android.FakeApp.1533, and Android.FakeApp.1534. In some cases, these actually can work as games, but their primary task is to load online casino and bookmaker websites.
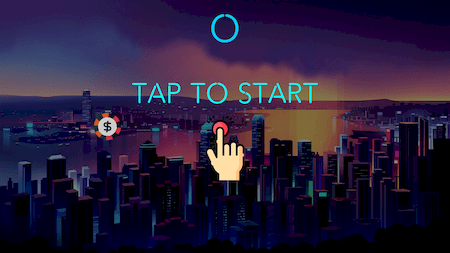
Examples of how these trojans operate as games:
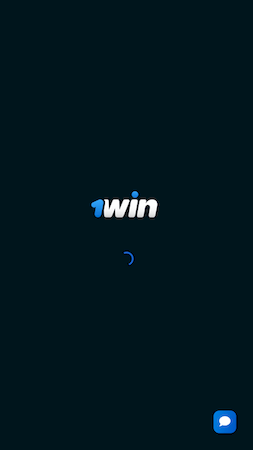
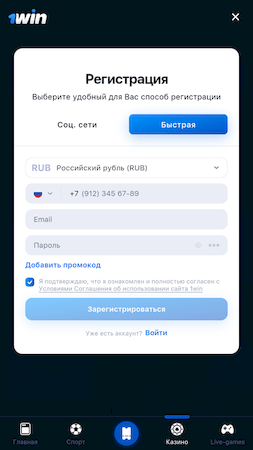
An example of a bookmaker site that one of these trojans loaded:
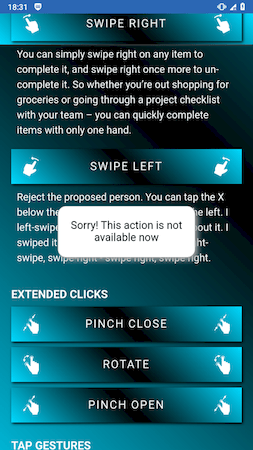
In addition, our specialists discovered another malicious program that subscribes users to paid services. Malicious actors distributed it under the guise of the Air Swipes, an app for controlling Android devices using gestures.
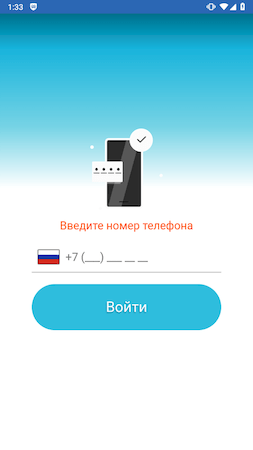
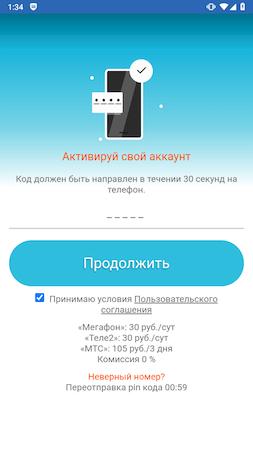
Upon launching, this trojan loads the website of an affiliate service through which the subscription is made:
If the victim launches the app when their Internet connection is disabled or if the target site is not available for loading, the trojan pretends to be the promised application. However, reporting that an error has occurred, it does not provide any useful functionality. The Dr.Web anti-virus detects this trojan application as Android.Subscription.21.
To protect your Android device from malware and unwanted programs, we recommend installing Dr.Web anti-virus products for Android.

Your Android needs protection.
Use Dr.Web
- The first Russian anti-virus for Android
- Over 140 million downloads—just from Google Play
- Available free of charge for users of Dr.Web home products