Doctor Web’s August 2023 virus activity review
September 27, 2023
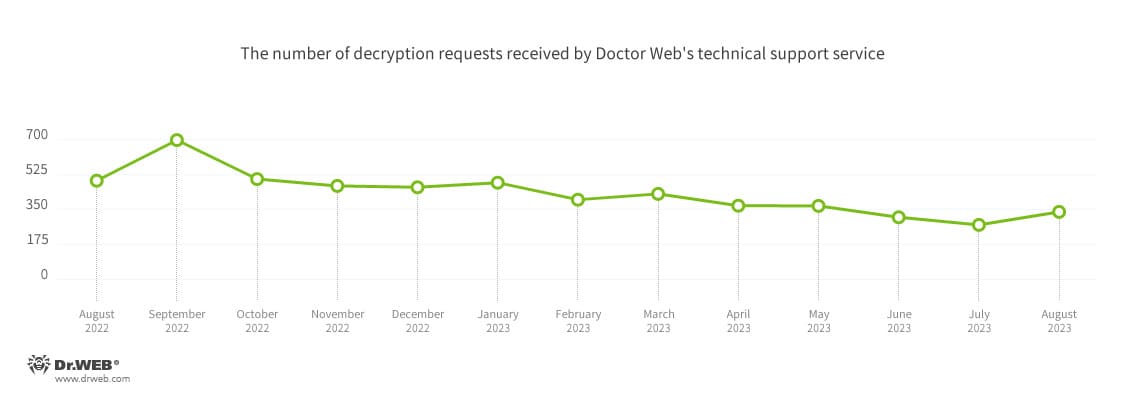
The number of user requests to decrypt files affected by encoder trojans increased by 23.99%, compared to July. The most common encoder was Trojan.Encoder.3953, with a share of 20.80% of all incidents recorded. July’s leader, Trojan.Encoder.26996, dropped to second place; it attacked users in 17.26% of the cases. Third place was taken by Trojan.Encoder.35534, with a share of 8.85%.
In August, the Android.HiddenAds.3766 trojan app was detected on Google Play. This malware displayed unwanted ads.
Principal trends in August
- An increase in the total number of detected threats
- An increase in the number of user requests to decrypt files affected by encoder trojans
- The emergence of a new malicious app on Google Play
According to Doctor Web’s statistics service
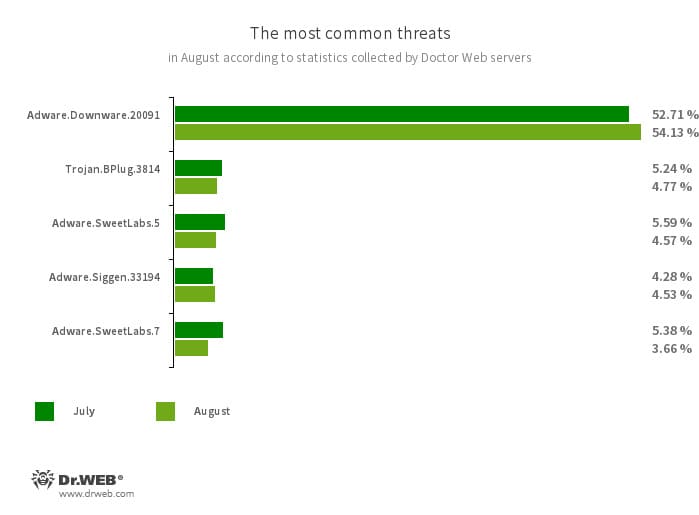
The most common threats in August:
- Adware.Downware.20091
- Adware that often serves as an intermediary installer of pirated software.
- Trojan.BPlug.3814
- The detection name for a malicious component of the WinSafe browser extension. This component is a JavaScript file that displays intrusive ads in browsers.
- Adware.SweetLabs.5
- Adware.SweetLabs.7
- An alternative app store and an add-on for Windows GUI (graphical user interface) from the creators of “OpenCandy” adware.
- Adware.Siggen.33194
- The detection name for a freeware browser that was created with an Electron framework and has a built-in adware component. This browser is distributed via various websites and loaded onto users’ computers when they try downloading torrent files.
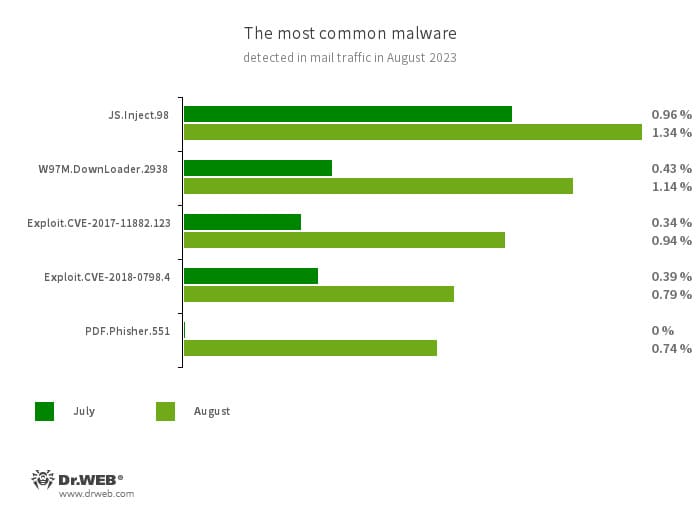
Statistics for malware discovered in email traffic
- JS.Inject
- A family of malicious JavaScripts that inject a malicious script into the HTML code of webpages.
- W97M.DownLoader.2938
- A family of downloader trojans that exploit vulnerabilities in Microsoft Office documents. They can also download other malicious programs to a compromised computer.
- Exploit.CVE-2017-11882.123
- Exploit.CVE-2018-0798.4
- Exploits designed to take advantage of Microsoft Office software vulnerabilities and allow an attacker to run arbitrary code.
- PDF.Phisher.551
- PDF documents used in phishing newsletters.
Encryption ransomware
In August, the number of requests to decrypt files affected by encoder trojans increased by 23.99%, compared to July.
The most common encoders of August:
- Trojan.Encoder.3953 — 20.80%
- Trojan.Encoder.26996 — 17.26%
- Trojan.Encoder.35534 — 8.85%
- Trojan.Encoder.29750 — 2.65%
- Trojan.Encoder.30356 — 2.65%
Dangerous websites
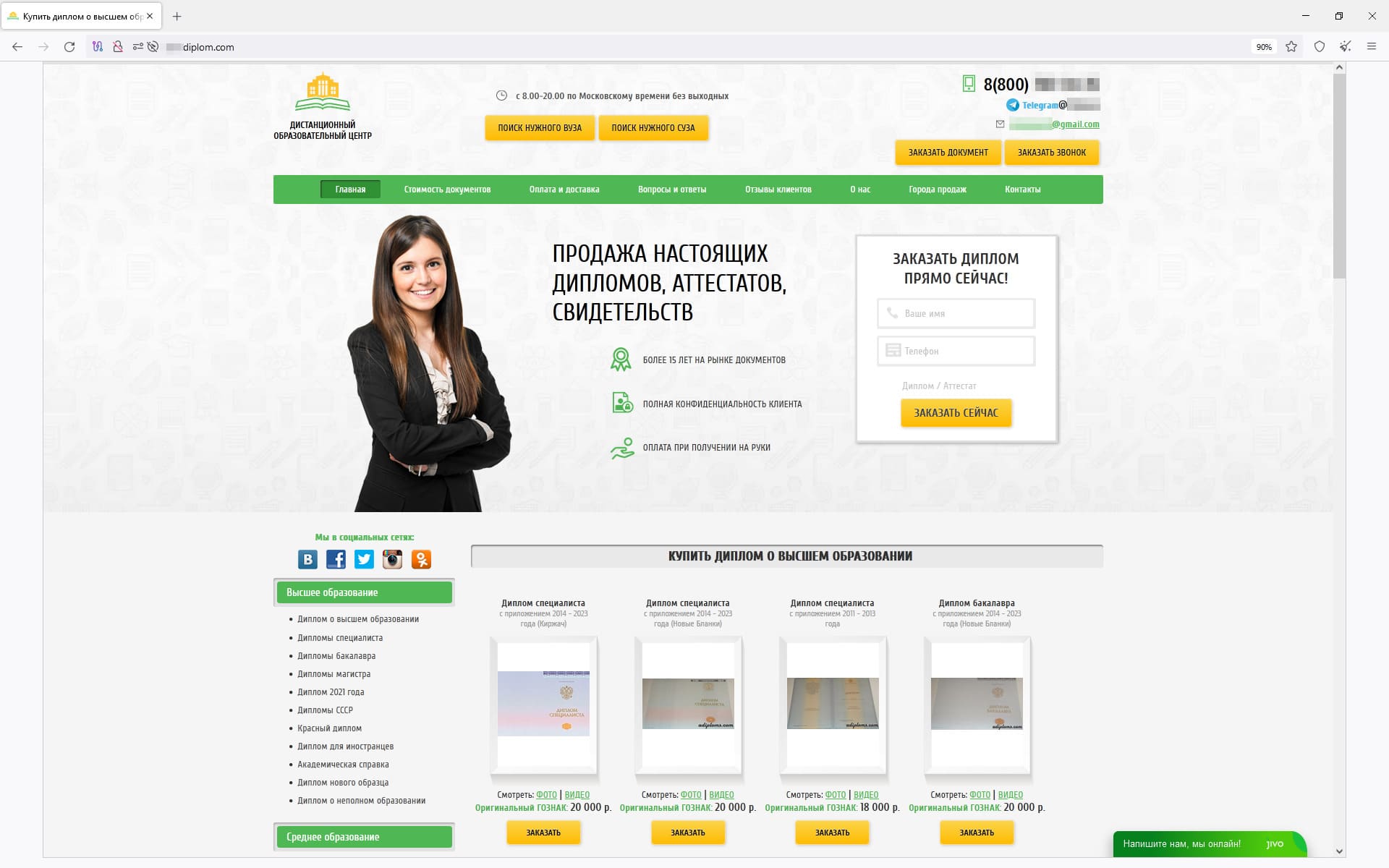
In August, Doctor Web’s Internet analysts discovered more fraudulent websites on which users could allegedly restore or buy new diplomas, passports, and other official documents. When attempting to use such “services”, users risk leaking personal data, losing money, and getting into trouble with law enforcement agencies. An example of one such site is shown in the screenshot below:
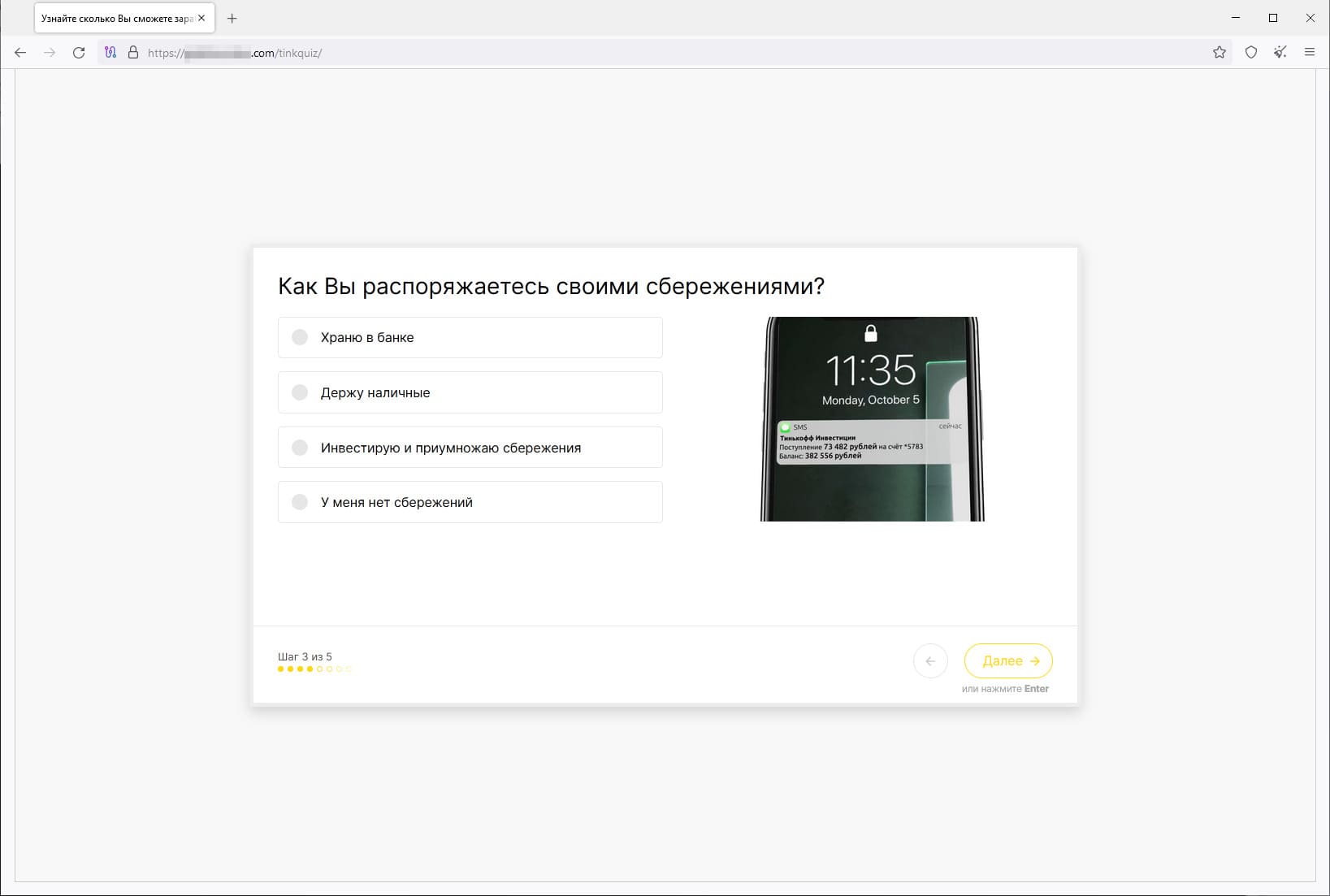
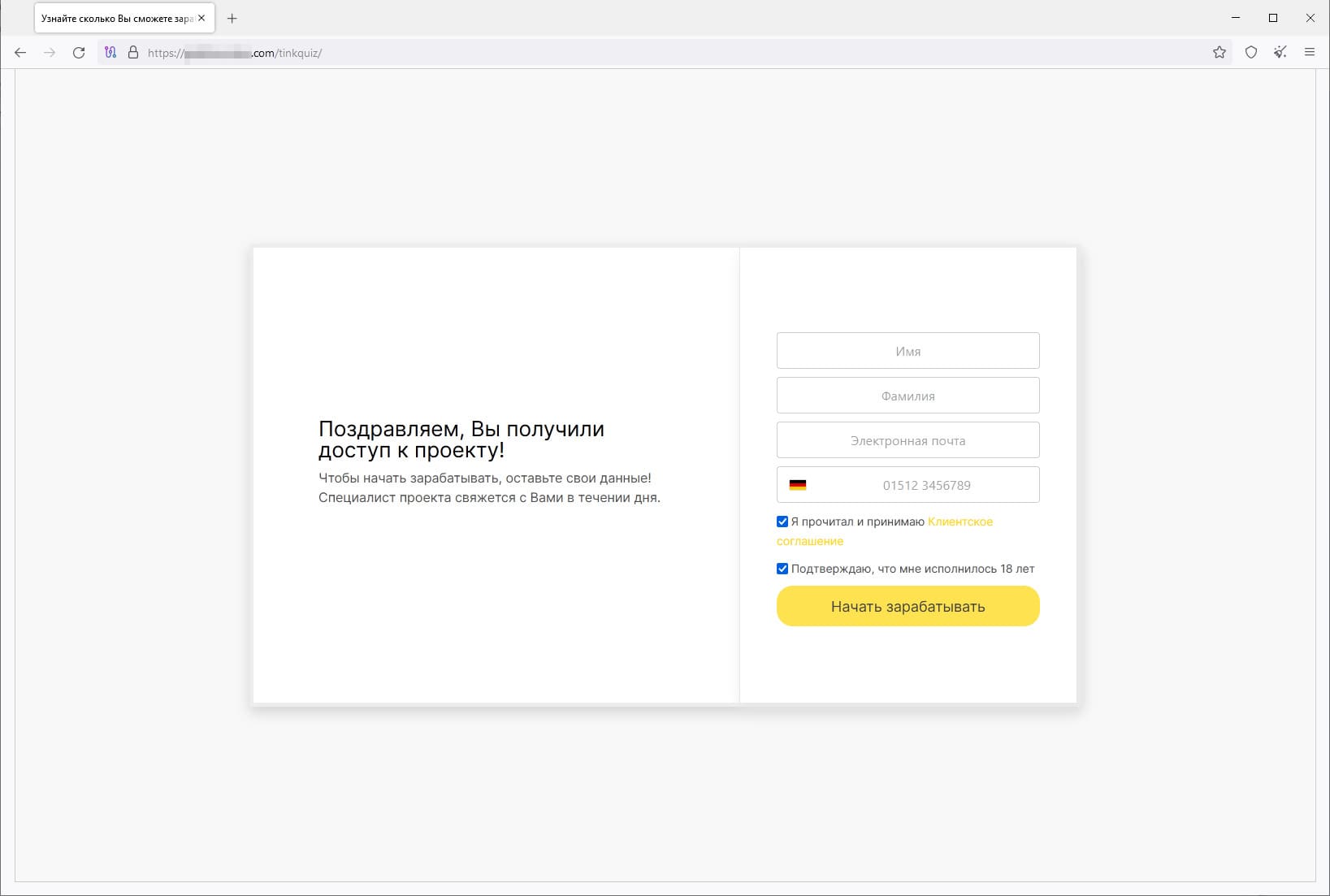
In addition, malicious actors continued to lure users to phishing websites appearing to provide various investment services. On such online resources, visitors are offered the opportunity to gain access to “investment products”. For this, they are asked to take a short test and provide personal information to register an account. If they agree, users are de facto giving away their personal data to an unknown party and can fall victim to scammers. The latter can, for example, pretend to be employees of financial organizations and offer to invest their victim’s money “profitably”. The next screenshots display an example of one such site:
A preliminary test/survey:
A special form for entering personal data such as the first and last names, email address, and phone number:
When a user confirms the input of their personal information and presses the “Start making money” button, the website informs them that they have registered successfully:
Malicious and unwanted programs for mobile devices
According to detection statistics collected by Dr.Web for Android, in August 2023, Android.MobiDash adware trojans were significantly more active. At the same time, users encountered Android.HiddenAds adware trojans less often.
The activity of ransomware and spyware trojans decreased, compared to July. However, the number of banking malware attacks increased.
In addition, a new malicious app was detected on Google Play.
The following August events involving mobile malware are the most noteworthy:
- A significant increase in the activity of Android.MobiDash adware trojans,
- A decrease in the activity of Android.HiddenAds adware trojans,
- A decrease in the activity of ransomware and spyware trojans,
- An increase in the number of banking malware attacks.
To find out more about the security-threat landscape for mobile devices in August, read our special overview.