Doctor Web’s August 2021 review of virus activity on mobile devices
September 8, 2021
Over the past month, Doctor Web specialists uncovered many threats on Google Play. Fake apps from the Android.FakeApp malware family that load fraudulent sites were among them. Moreover, another trojan designed to steal logins and passwords of Facebook accounts was also found. In addition, the attackers have spread trojans from the Android.Joker family that subscribe victims to paid mobile services.
PRINCIPAL TRENDS IN AUGUST
- The discovery of new malware on Google Play
- Adware trojans and malware that download other software and execute arbitrary code remain one of the most active threat
According to statistics collected by Dr.Web for Android
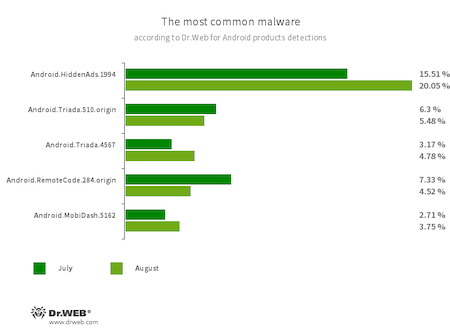
- Android.HiddenAds.1994
- Trojan designed to display obnoxious ads. Trojans of this family are often distributed as harmless applications and, in some cases, are installed in the system directory by other malware.
- Android.Triada.510.origin
- Android.Triada.4567
- Multifunctional trojans performing various malicious actions. This malware belongs to the trojan family that infects other app processes. Some modifications of this family were found in the firmware of Android devices, which attackers implanted during manufacturing. Some of them can also exploit various vulnerabilities to gain access to protected system files and folders.
- Android.RemoteCode.284.origin
- A malicious application that download and execute arbitrary code. Depending on their modification, trojans of this family can also load various websites, open web links, click on advertising banners, subscribe users to premium services, and perform other actions.
- Android.MobiDash.5162
- A trojan that displays obnoxious ads. It represents a special software module that is incorporated into the applications by the developers.
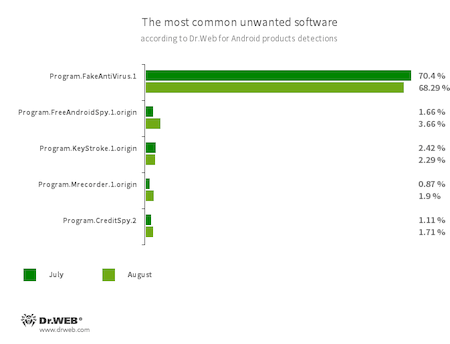
- Program.FakeAntiVirus.1
- The detection name for adware programs that imitate anti-virus software. These apps inform users of non-existing threats, mislead them, and demand they purchase the full version of the software.
- Program.KeyStroke.1.origin
- An Android application capable of intercepting keystrokes. Some modifications of this software can also track incoming SMS, control calls history, and record phone calls.
- Program.FreeAndroidSpy.1.origin
- Program.Mrecorder.1.origin
- Applications that spy on Android users and can be used for cyber espionage. Depending on their modification and version, they can control the location of the device, collect the information on calls, SMS, and social media chats, gain access to a phone book and user contact list, record the surroundings, and can also copy multimedia and other files, such as photos, videos, documents, etc.
- Program.CreditSpy.2
- The detection name for programs designed to assign credit ratings to users based on their personal data. These applications upload SMS, contact information from phonebooks, call history, and other information to the remote server.
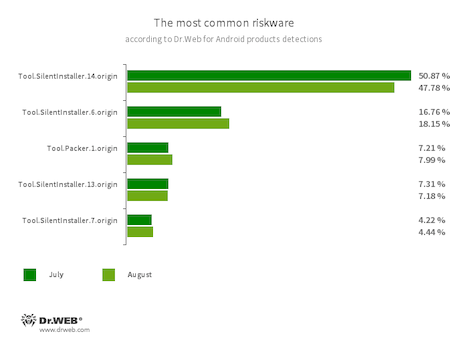
- Tool.SilentInstaller.14.origin
- Tool.SilentInstaller.13.origin
- Tool.SilentInstaller.6.origin
- Tool.SilentInstaller.7.origin
- Riskware platforms that allow applications to launch APK files without installation. They create a virtual runtime environment that does not affect the main operating system.
- Tool.Packer.1.origin
- A packer tool designed to protect Android applications from their unauthorized modification and reverse engineering. This tool is not malicious by itself, but it can be used to protect both harmless and malicious software.
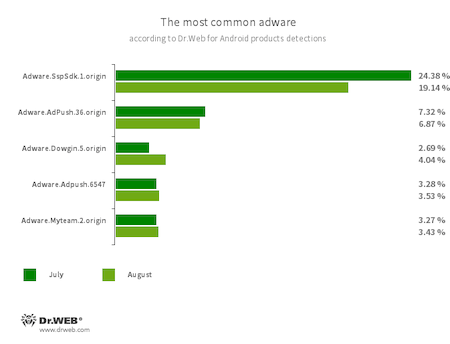
Program modules incorporated into Android applications and designed to display obnoxious ads on Android devices. Depending on their family and modifications, they can display full screen ads and block other apps’ windows, show various notifications, create shortcuts, and load websites.
- Adware.SspSdk.1.origin
- Adware.AdPush.36.origin
- Adware.Adpush.6547
- Adware.Dowgin.5.origin
- Adware.Myteam.2.origin
Threats on Google Play
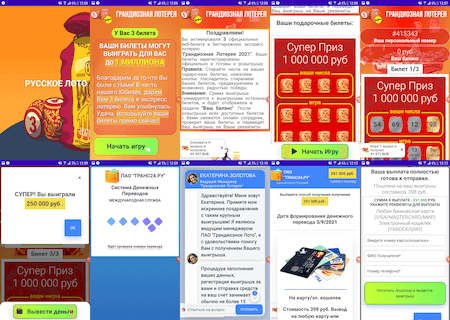
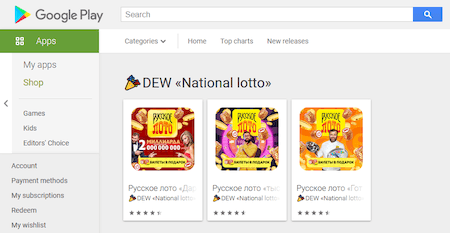
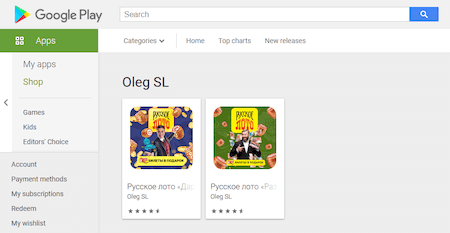
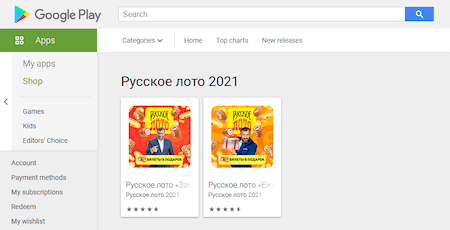
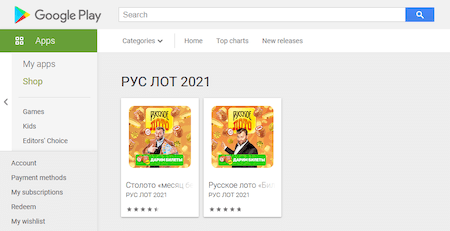
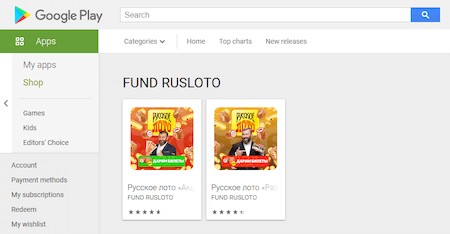
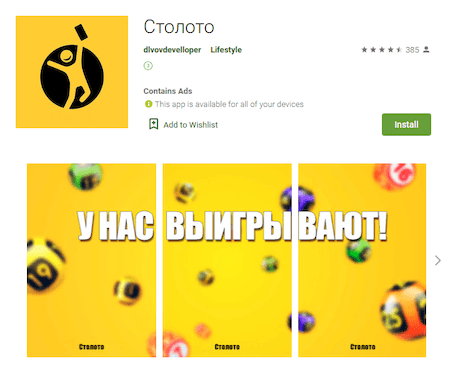
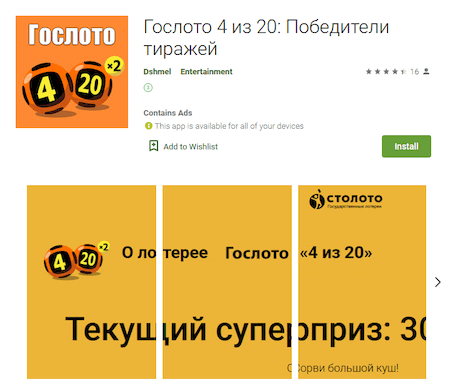
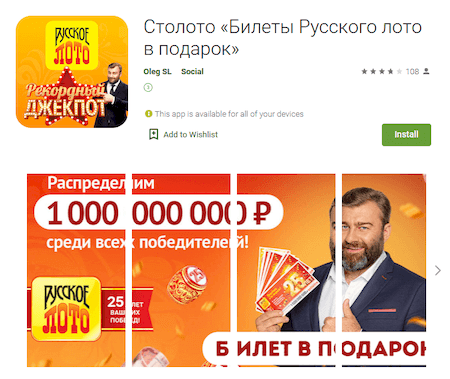
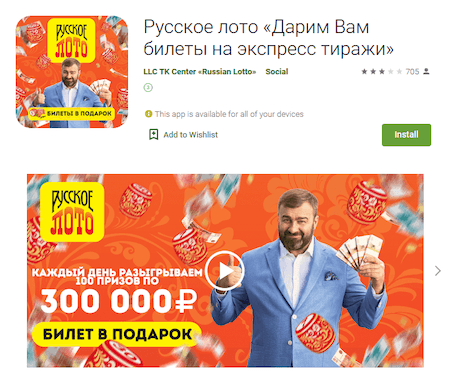
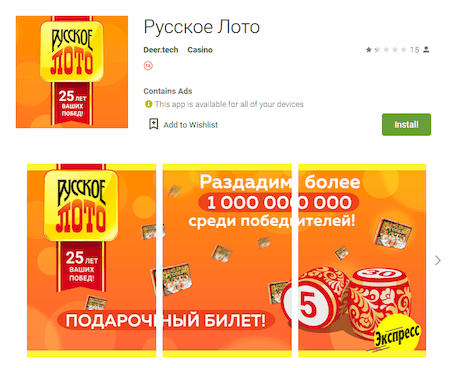
In August, a large number of malware was found on Google Play. Fake apps of the Android.FakeApp family that are used in various scam schemes were among them. For example, some of them were again spread under the guise of official software for popular Russian lotteries “Русское лото” (Russian Lotto) and “Гослото” (Gosloto), as well as their official distributor “Столото” (Stoloto). These fakes were added to the Dr.Web virus base as Android.FakeApp.307, Android.FakeApp.308, Android.FakeApp.309, Android.FakeApp.310, Android.FakeApp.311, Android.FakeApp.312, Android.FakeApp.325, Android.FakeApp.328, Android.FakeApp.329, Android.FakeApp.330, Android.FakeApp.332, Android.FakeApp.333, Android.FakeApp.334, Android.FakeApp.335, and Android.FakeApp.341.
Upon launch, the apps loaded fraudulent sites where potential victims were offered to get allegedly free lottery tickets and to play the game to win prizes. However, it was nothing but a scam. The so-called “game” was scripted and the “winners” were asked to pay a “fee” or a “custom”, and this money then ended up going to the fraudsters' pockets.
An example of how one of these fake applications operates is shown below:
The following are examples of how such apps can be seen on Google Play:
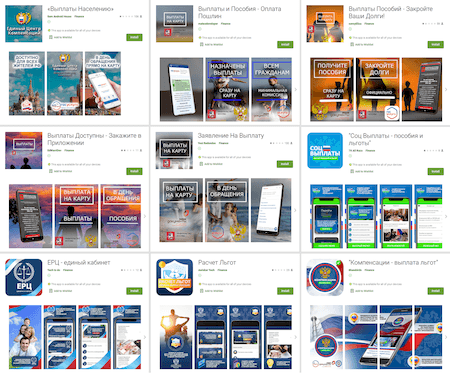
Other fakes were apps that were allegedly designed to help Russian users to search for information about state social benefits and to receive this financial support to their bank accounts and cards. Similar to fake lottery schemes, such apps only loaded fraudulent websites, where, to receive the “funds”, potential victims were asked to pay a “fee”.
The trojans were added to the Dr.Web virus base as Android.FakeApp.306, Android.FakeApp.313, and Android.FakeApp.325.
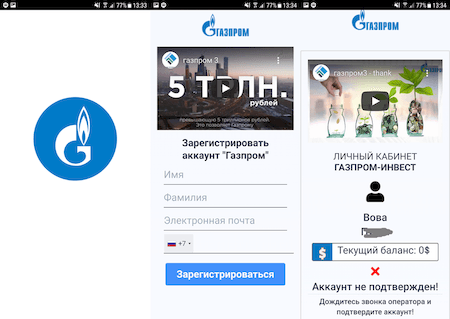
Moreover, new scam software disguised as investing and trading software was also discovered. Some of these apps were spread under the name of famous companies.
The trojans, dubbed Android.FakeApp.305, Android.FakeApp.314, Android.FakeApp.315, and Android.FakeApp.316, loaded various “financial” decoy sites where users were offered to register to start earning the money. In some cases, the victims were asked to provide their first and last name, their email address, and mobile number. In others, only the mobile number was requested. Next, users could be redirected to other fraudulent sites, received a notification that there is no more room for new clients, or were asked to wait for the “operator” calling back.
The examples of how these apps operate are shown below:
Using such fake investing apps, the malicious actors not only collect victims’ personal information and steal their money but can also drag them into other scam schemes by selling obtained personal data to a third party, for example.
New trojans from the dangerous Android.Joker family were among discovered threats as well. They were added to the Dr.Web virus base as Android.Joker.320.origin, Android.Joker.858, and Android.Joker.910. The first one was spread as an animated wallpaper called 3D Live Wallpaper. The second one was disguised as a music app called New Music Ringtones. And the third one was labeled, Free Text Scanner app, designed to scan texts and create PDF documents. All these apps subscribed Android users to paid mobile services and could also load and execute arbitrary code.
In addition, our malware analysts have found a new trojan designed to steal Facebook accounts’ logins and passwords. It was spread as an application that protects installed apps from unauthorized access. This trojan was added to the Dr.Web virus base as Android.PWS.Facebook.34.
To protect your Android device from malware and unwanted programs, we recommend installing Dr.Web for Android.

Your Android needs protection.
Use Dr.Web
- The first Russian anti-virus for Android
- Over 140 million downloads—just from Google Play
- Available free of charge for users of Dr.Web home products