Doctor Web’s July 2020 overview of malware detected on mobile devices
August 10, 2020
In July, the number of threats detected on Android devices decreased by 6.7% compared to June. The number of active malware lowered by 6.75%, unwanted applications by 4.6%, riskware by 8.42% and adware by 9.83%.
Throughout the month, Doctor Web malware analysts uncovered yet more malicious apps on Google Play. The Android.Banker.3259 banking trojan, disguised as an SMS manager, was one of them. New modifications of the Android.HiddenAds adware trojan family, capable of displaying advertisement banners, were among other threats. Furthermore, a new member of the dangerous Android.Joker trojan family, designed to subscribe users to premium services and execute arbitrary code, has also been spotted.
PRINCIPAL TRENDS IN JULY
- The number of threats detected on Android mobile devices has decreased
- The discovery of new threats on Google Play
According to statistics collected by Dr.Web for Android
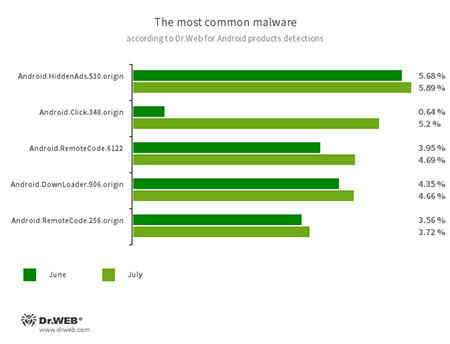
- Android.HiddenAds.530.origin
- A trojan designed to display obnoxious ads and distributed as popular applications. In some cases, it can be installed in the system directory by other malware.
- Android.Click.348.origin
- A trojan that automatically loads websites and clicks on links and advertisement banners. It can be spread as a harmless app so that users will not consider it as a threat.
- Android.RemoteCode.6122
- Android.RemoteCode.256.origin
- Malicious applications that download and execute arbitrary code. Depending on their modification, they can load various websites, open web links, click on advertisement banners, subscribe users to premium services and perform other actions.
- Android.DownLoader.906.origin
- A trojan that downloads other malware and unwanted software. It can be hidden inside seemingly harmless apps found on Google Play or malicious websites.
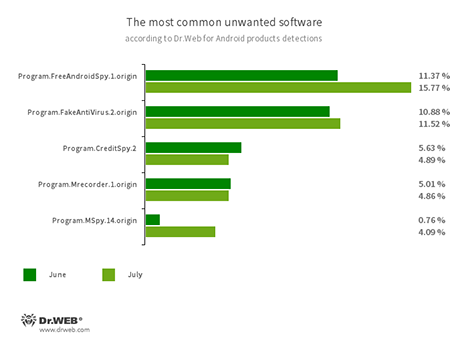
- Program.FreeAndroidSpy.1.origin
- Program.Mrecorder.1.origin
- Program.MSpy.14.origin
- Software that monitors Android user activity and may serve as a tool for cyber espionage. These apps can track device locations, collect information from SMS and social media messages, copy documents, photo and video, spy on phone calls, etc.
- Program.FakeAntiVirus.2.origin
- Detection name for adware programs that imitate anti-virus software. These apps inform users of non-existing threats, mislead them and demand they purchase the full version of the software.
- Program.CreditSpy.2
- Detection name for programs designed to assign credit ratings to users based on their personal data. These applications upload SMS, contact information from phonebooks, call history and other information to the remote server.
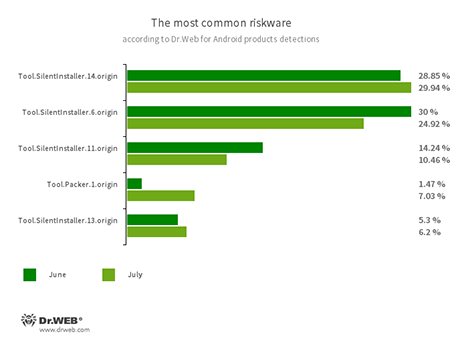
- Tool.SilentInstaller.6.origin
- Tool.SilentInstaller.11.origin
- Tool.SilentInstaller.13.origin
- Tool.SilentInstaller.14.origin
- Riskware platforms that allow applications to launch APK files without installation. They create a virtual runtime environment that does not affect the main operating system.
- Tool.Packer.1.origin
- A packer tool designed to protect Android applications from their unauthorised modification and reverse engineering. This tool is not malicious by itself, but it can be used to protect both harmless and malicious software.
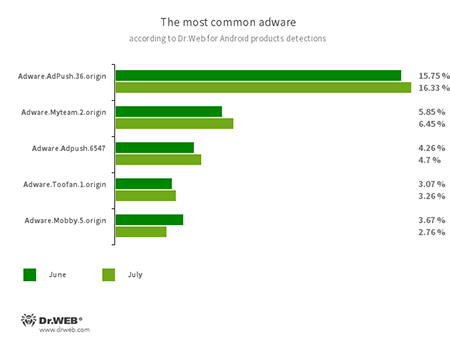
- Adware.Adpush.36.origin
- Adware.Adpush.6547
- Adware.Myteam.2.origin
- Adware.Mobby.5.origin
- Adware.Toofan.1.origin
- The first Russian anti-virus for Android
- Over 140 million downloads—just from Google Play
- Available free of charge for users of Dr.Web home products
Program modules incorporated into Android applications and designed to display obnoxious ads on Android devices. Depending on their family and modifications, they can display full screen ads and block other apps’ windows, show various notifications, create shortcuts and load websites.
Threats on Google Play
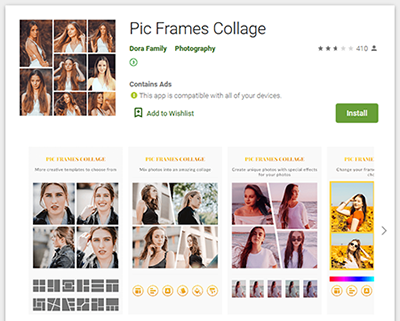
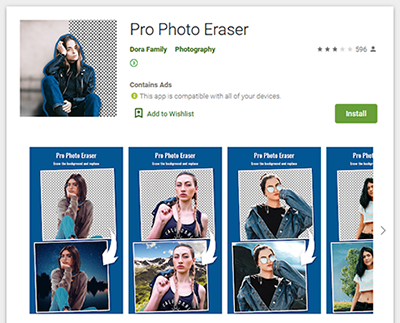
Among the threats found on Google Play in July were the new modifications of the Android.HiddenAds malware family, dubbed Android.HiddenAds.2190 and Android.HiddenAds.2193. Their authors spread them as an image editing software.
Upon their launch, they hid their icons from the apps list on the main screen, similar to other trojans of this family. They do so to make it more difficult for the users to delete them. After that, they start to display obnoxious advertisement overlays on top of other apps and the operating system UI.
Another trojan discovered by Doctor Web malware analysts was dubbed Android.Joker.279. It hid under the guise of an application designed to work with SMS. Upon its launch, it subscribed victims for premium services and was able to run arbitrary code.
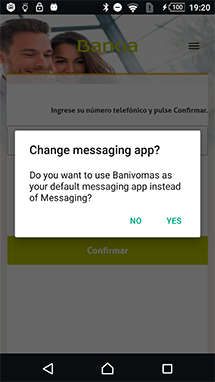
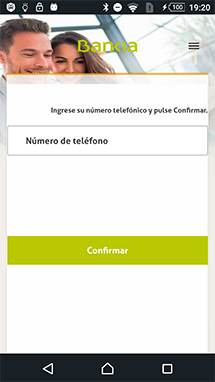
Moreover, our specialists uncovered a new banking trojan dubbed Android.Banker.3259. Malware writers based this banker on an open source SMS messenger.
Upon its launch, the trojan connects to the remote server and waits for further commands. Based on the received response, it either continues to operate as a harmless application or tries to steal personal data from the user by displaying a phishing window. In addition, Android.Banker.3259 saves all the incoming and outgoing SMS to the Firebase cloud database. Cybercriminals can then use the information, obtained from these messages, in future attacks.
To protect your Android device from malware and unwanted programs, we recommend installing Dr.Web for Android.