Doctor Web’s May 2020 overview of malware detected on mobile devices
June 19, 2020
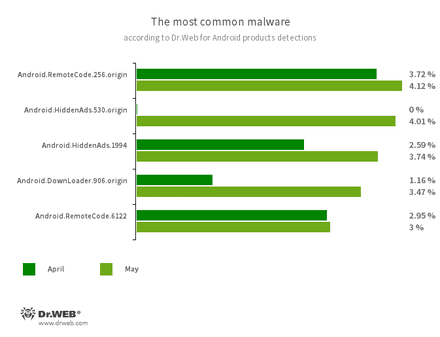
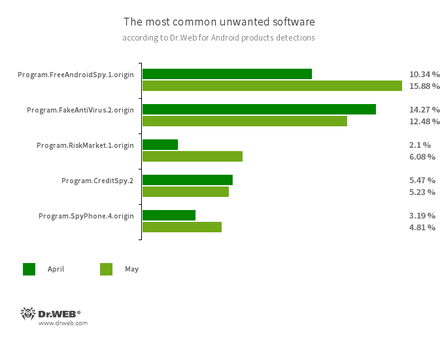
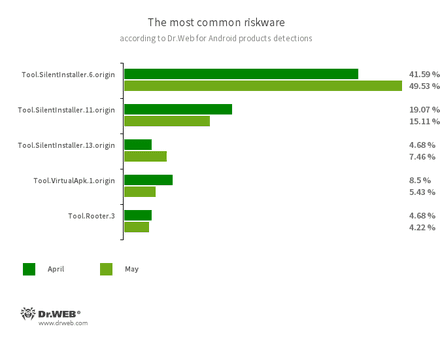
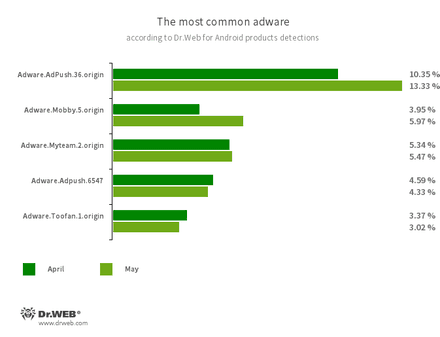
In May, the number of threats detected on Android devices increased by 3.35% compared to April. The number of identified malicious programs increased by 3.75%, riskware by 8.77%, and adware by 1.62%. With this, the number of unwanted software found on Android devices decreased by 1.77%.
At the end of May Doctor Web warned about the Android.FakeApp.176, trojan, which scammers were spreading as a mobile version of Valorant game. Using this malware, cybercriminals earned money by participating in various online affiliate programs.
New modifications of the Android.Joker trojan family, capable of executing arbitrary code and subscribing Android device users to premium services, have been found on Google Play. In addition, our malware analysts have discovered new modifications of the Android.HiddenAds trojan family, designed to display advertisements. Apps with unwanted adware modules, as well as a new member of the Android.Circle trojan family, have also been found on Google Play. The latter could display ads, was able to run BeanShell scripts and load various websites where it could click on banners and links. Malware authors have spread other mobile threats throughout the month.
PRINCIPAL TRENDS IN MAY
- Minor increase in the number of threats discovered on Android devices
- Discovery of new threats on Google Play
Threat of the month
In May, Doctor Web reported on the discovery of the fake mobile version of the Valorant game. In reality, it was nothing but a modification of the Android.FakeApp.176 trojan. For a long time, scammers were spreading it as famous applications and using it to illegally profit through various affiliate programs.
To get full access to the game, the trojan invites its target victims to complete several tasks found on the website of one of the affiliate services. For example, the trojan can offer to install and run other games. Scammers receive a financial reward for each successfully finished task, while victims receive nothing.
According to statistics collected by Dr.Web for Android
- Android.RemoteCode.256.origin
- Android.RemoteCode.6122
- Malicious applications that download and execute arbitrary code. Depending on their modification, they can load various websites, open web links, click on advertisement banners, subscribe users to premium services and perform other actions.
- Android.HiddenAds.530.origin
- Android.HiddenAds.1994
- Trojans designed to display obnoxious ads. They are distributed disguised as popular applications. In some cases, they can be installed in the system directory by other malware.
- Android.DownLoader.906.origin
- A trojan that downloads other malware and unwanted software. It can be hidden inside seemingly harmless apps found on Google Play or malicious websites.
- Program.FreeAndroidSpy.1.origin
- Program.SpyPhone.4.origin
- Software that monitors Android user activity and may serve as a tool for cyber espionage. These apps can track device locations, collect information from SMS and social media messages, copy documents, photo and video, spy on phone calls, etc.
- Program.FakeAntiVirus.2.origin
- Detection name for adware programs that imitate anti-virus software. These apps inform users of non-existing threats, mislead them and demand they purchase the full version of the software.
- Program.CreditSpy.2
- Detection name for programs designed to assign credit ratings to users based on their personal data. These applications upload SMS, contact information from phonebooks, call history and other information to the remote server.
- Program.RiskMarket.1.origin
- An app store that contains trojanized software and recommends users install it.
- Tool.SilentInstaller.6.origin
- Tool.SilentInstaller.11.origin
- Tool.SilentInstaller.13.origin
- Tool.VirtualApk.1.origin
- Riskware platforms that allow applications to launch APK files without installation. They create a virtual runtime environment that does not affect the main operating system.
- Tool.Rooter.3
- A utility designed to obtain root privileges on Android devices. Users, cybercriminals and malware may all use it.
Program modules incorporated into Android applications and designed to display obnoxious ads on Android devices. Depending on their family and modifications, they can display full screen ads and block other apps’ windows, show various notifications, create shortcuts and load websites.
- Adware.Adpush.36.origin
- Adware.Adpush.6547
- Adware.Mobby.5.origin
- Adware.Myteam.2.origin
- Adware.Toofan.1.origin
Threats on Google Play
Last month, Doctor Web malware analysts discovered several new Android.Joker trojan family modifications, such as Android.Joker.174, Android.Joker.182, Android.Joker.186, Android.Joker.138.origin, Android.Joker.190 and Android.Joker.199. They were built into the document management apps, image collections apps, camera apps, system tools, messengers and other software that appeared harmless. However, upon launching these trojan apps were able to load and execute arbitrary code and subscribe victims to premium services.
Our specialists have also discovered the Android.Circle.15 trojan, which was spread as a system performance optimizing tool. Upon launching, it displayed advertisements, loaded various websites and clicked the embedded links and banners. Similar to other members of the Android.Circle malware family, it could also run BeanShell scripts.
Trojans of the Android.HiddenAds family, such as Android.HiddenAds.2134, Android.HiddenAds.2133, Android.HiddenAds.2146, Android.HiddenAds.2147, Android.HiddenAds.2048 and Android.HiddenAds.2150, were among the discovered threats. They were spread under the guise of WhatsApp sticker collections, games, image collections and various tutorial apps. Doctor Web researchers have found more than 30 modifications of these trojans, which have been installed by nearly 160,000 users.
Upon launch, these malicious apps concealed their icon from the apps list on the main screen of the Android operating system and began displaying full screen adware banners that interfere with the normal usage of infected devices.
New adware modules dubbed Adware.AdSpam.4, Adware.AdSpam.5 and Adware.AdSpam.6 have also been spread as harmless apps, such as games and image collections. Similar to the Android.HiddenAds trojan family members, they displayed banners on top of other apps. But, they didn’t conceal their icons, and users were able to locate the source of advertisements more easily to delete the apps that contained the built-in adware modules.
Other threats
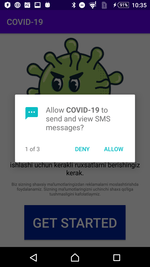
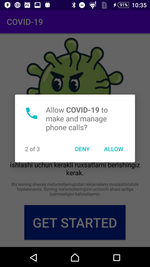
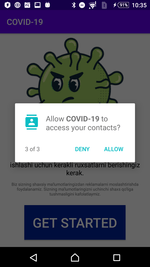
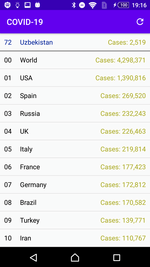
A trojan exploiting the SARS-CoV-2 pandemic, was among the threats spread in May. This malware, dubbed Android.Spy.660.origin, was spread as a tool showing the number of COVD-19 infections. But the true purpose of this this trojan was cyber espionage. Users from Uzbekistan were the main target of Android.Spy.660.origin. The trojan snooped on users’ SMS, phone calls and contacts from their phone books. Upon launching, the trojan requested the required system permissions and displayed the infection statistics so as not to raise suspicions.
Cybercrooks continued to bombard users with various banking malware attacks. For example, Vietnamese users attacked by Android.Banker.388.origin, which was spread through a fake Ministry of Public Security website. At the same time, Japanese users again faced various banking trojan families, which have been spreading through fake postal and courier service websites for a long time.
To protect your Android device from malware and unwanted programs, we recommend installing Dr.Web for Android.

Your Android needs protection.
Use Dr.Web
- The first Russian anti-virus for Android
- Over 140 million downloads—just from Google Play
- Available free of charge for users of Dr.Web home products