Doctor Web’s overview of malware detected on mobile devices in November 2017
November 30, 2017
In November, a multitude of new malicious applications were detected on Google Play.
In early November, security specialists detected a Trojan-Miner that exploited mobile device computing power to mine cryptocurrency. Later, specialists found SMS Trojans that subscribed users to chargeable services. In mid-November, Doctor Web specialists detected a malicious program that downloaded additional Trojan modules. These modules loaded websites and tapped on advertisements and links. In addition, a Trojan was distributed via Google Play. It was designed to download different applications. Furthermore, Android bankers were detected on Google Play. These were designed to steal private user information and money from user bank accounts.
PRINCIPAL TRENDS IN NOVEMBER
- The detection of a large number of Trojans on Google Play that were embedded into benign applications
Mobile threat of the month
In November, Doctor Web security specialists found nine Google Play applications containing the Trojan Android.RemoteCode.106.origin. In total, these applications have been downloaded at least 2,370,000 times. Once launched, Android.RemoteCode.106.origin downloads and launches additional malicious modules. They are used to automatically load websites specified by a control server and tap advertisements and links on browsed web pages. For more details about Android.RemoteCode.106.origin, please refer to the article on our website.
According to statistics collected by Dr.Web for Android
- Android.HiddenAds.238
- Trojans designed to display unwanted ads on mobile devices.
- Android.Triada.63
- Android.Triada.152
- A Trojan that performs different malicious functions.
- Android.DownLoader.653.origin
- A Trojan that downloads other malware programs.
- Android.Click.171.origin
- A Trojan that periodically requests specified websites and can be used to inflate their popularity and follow advertising links.
- Adware.Jiubang.2
- Adware.Jiubang.1
- Adware.Adviator.6.origin
- Adware.Airpush.31.origin
- Adware.SalmonAds.1.origin
- Unwanted program modules incorporated into Android applications and designed to display annoying ads on mobile devices.
Trojan-Miner
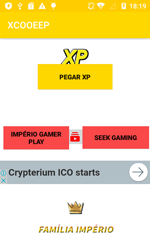
In early November, the Trojan Android.CoinMine.3 was detected on Google Play. It used the computing power of Android mobile devices to mine the Monero cryptocurrency. This malware was hidden in an application called XCOOEEP, which is designed to access the Club Cooee online chat.
In the WebView window, which is invisible to the user, Android.CoinMine.3 loaded a website containing mining script that runs automatically. The intensive mining process could cause infected mobile devices to experience decreased performance and overheat, and their batteries to drain faster.
SMS Trojans
Several SMS Trojans distributed via Google Play were among the malicious applications found in the past month. They were embedded into the Secret Notepad, Delicate Keyblard and Super Emotion applications and detected by Dr.Web as Android.SmsSend.23371, Android.SmsSend.23373 and Android.SmsSend.23374. These malicious programs tried to send expensive messages and subscribe user numbers to unwanted services.
Downloader Trojan
In November, new versions of the Android.DownLoader.658.origin Trojan were found on Google Play. When ordered by cybercriminals, it offered mobile users different applications for download and installation. It could also independently download software. Features of Android.DownLoader.658.origin:
- embedded into benign applications;
- activates malicious functionality only if a number of conditions are met (for example, if it is not running on the emulator or the mobile device’s functions for developers are turned off);
- shows notifications proposing to users that they download and install some program;
- to prevent detection and analysis, the Trojan’s authors use a special packer, detected by Dr.Web as Android.Packed.1.
Banking Trojans
In the past month, the Trojan Android.Banker.202.origin was detected on Google Play. It was hidden in benign applications. Once launched, it extracted several malicious components from its resource folder and launched the malicious program Android.Banker.1426. This Trojan downloaded from the control server an Android banker from the Android.BankBot family. This malware program was designed to steal logins, credentials and other confidential information.
A similar scheme was used in a number Android.Banker family Trojans that were also detected on Google Play in November. They extracted and launched a hidden malicious component that would also extract resources from its file and run another Trojan component. The latter, in turn, downloaded one of the banking Trojans from a remote location and tried to install it.
The detection of a large number of malicious applications on Google Play indicates that cybercriminals are still finding new ways to bypass its defense mechanisms. Doctor Web recommends that smartphone and tablet owners install Dr.Web for Android to protect their mobile devices from Trojans and other unwanted programs.
Your Android needs protection
Use Dr.Web
- The first Russian Anti-virus for Android
- More than 135 million downloads on Google Play alone
- Free for users of Dr.Web home products