Doctor Web’s April 2022 review of virus activity on mobile devices
May 27, 2022
Over the month, Doctor Web’s specialists uncovered new malware on Google Play. Android.FakeApp fraudulent apps and Android.Joker trojans, which subscribe victims to paid services, were among them.
PRINCIPAL TRENDS IN APRIL
- Decreased activity of the Android.Spy.4498 trojan
- Decreased activity among adware trojans
- The appearance of new malicious programs on Google Play
According to statistics collected by Dr.Web for Android
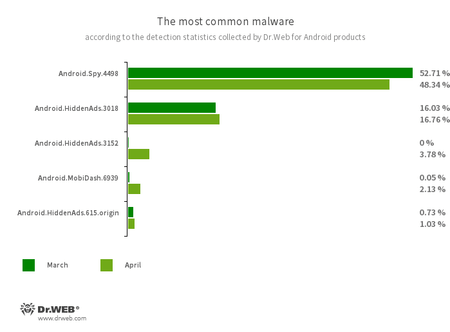
- Android.Spy.4498
- A trojan that steals the contents of other apps’ notifications. It can also download apps and offer users to install them, and it can also display various dialog boxes.
- Android.HiddenAds.3018
- Android.HiddenAds.3152
- Android.HiddenAds.615.origin
- Trojans designed to display obnoxious ads. Trojans of this family are often distributed as popular and harmless applications. In some cases, other malware can install them in the system directory. When these trojans infect Android devices, they typically conceal their presence from the user. For example, they “hide” their icons from the home screen menu.
- Android.MobiDash.6939
- A trojan that displays obnoxious ads. It is a special software module that developers incorporate into applications.
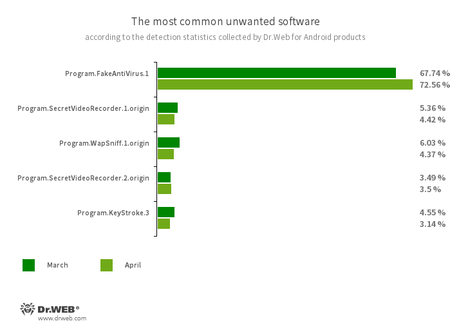
- Program.FakeAntiVirus.1
- The detection name for adware programs that imitate anti-virus software. These apps inform users of non-existing threats, mislead them, and demand that they purchase the software’s full version.
- Program.SecretVideoRecorder.1.origin
- Program.SecretVideoRecorder.2.origin
- The detection name for various modifications of an application that is designed to record videos and take photos in the background using built-in Android device cameras. It can operate covertly by allowing notifications about ongoing recordings to be disabled. It also allows the app’s icon and name to be replaced with fake ones. This functionality makes this software potentially dangerous.
- Program.WapSniff.1.origin
- An Android program designed to intercept WhatsApp messages.
- Program.KeyStroke.3
- An Android application capable of intercepting keystrokes. Some modifications of this software can also track incoming SMS, control call history, and record phone calls.
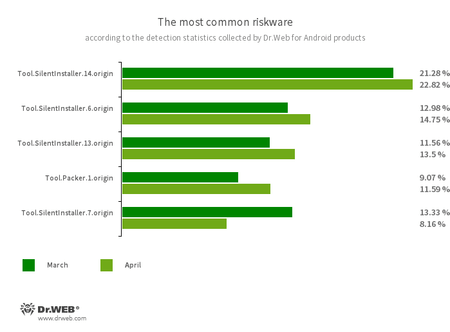
- Tool.SilentInstaller.14.origin
- Tool.SilentInstaller.6.origin
- Tool.SilentInstaller.13.origin
- Tool.SilentInstaller.7.origin
- Riskware platforms that allow applications to launch APK files without installing them. They create a virtual runtime environment that does not affect the main operating system.
- Tool.Packer.1.origin
- A packer tool designed to protect Android applications from unauthorized modifications and reverse engineering. This tool is not malicious in itself, but it can be used to protect both harmless and malicious software.
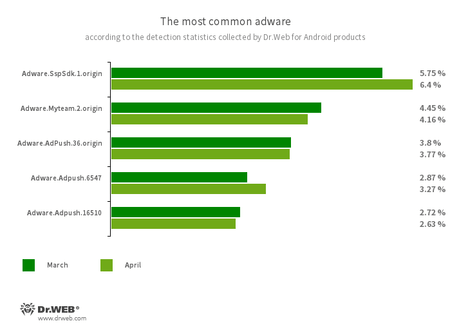
Program modules incorporated into Android applications. These are designed to display obnoxious ads on Android devices. Depending on their family and modifications, they can display full-screen ads and block other apps’ windows, show various notifications, create shortcuts, and load websites.
- Adware.SspSdk.1.origin
- Adware.Myteam.2.origin
- Adware.AdPush.36.origin
- Adware.Adpush.6547
- Adware.Adpush.16510
Threats on Google Play
Last month, Doctor Web’s malware analysts discovered yet other malicious apps on Google Play. Trojans from the Android.Joker family, capable of loading and executing arbitrary code and subscribing users to paid mobile services, were among them. One of these trojans hid in the live wallpaper app “Purple Live Wallpaper”. Another one was disguised as a “QR Code Reader” app designed to scan bar codes. They were added to the Dr.Web virus database as Android.Joker.1381 and Android.Joker.1383, respectively.
Moreover, our specialists uncovered new trojans from the Android.FakeApp family, which were dubbed Android.FakeApp.930, Android.FakeApp.931, and Android.FakeApp.933. Malicious actors have spread these as software that allegedly could help Russian users search for information on social benefits and monetary compensation and immediately receive money due to them. The trojans hid in the apps “Как получить компенсацию от РФ”, “Пособия для граждан 2022”, and “Выплаты ФРСП”.
In reality, these fakes loaded fraudulent sites which cybercriminals used to trick potential victims in order to steal their personal information and money.
To protect your Android device from malware and unwanted programs, we recommend installing Dr.Web anti-virus products for Android.

Your Android needs protection.
Use Dr.Web
- The first Russian anti-virus for Android
- Over 140 million downloads—just from Google Play
- Available free of charge for users of Dr.Web home products