Doctor Web’s September 2019 virus activity review
October 9, 2019
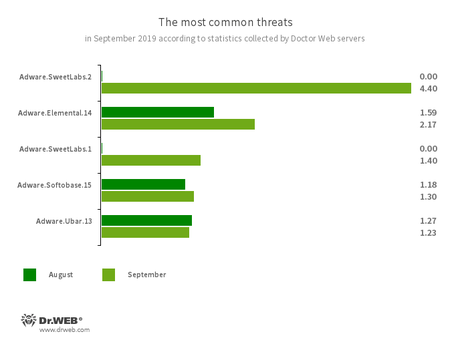
In September, Dr.Web server statistics showed an increase in the total number of threats by 19.96%, as compared with the previous month. At the same time, the share of unique threats decreased by 50.45%. Users were mostly attacked by adware, as well as software downloaders and installers. In email traffic, again, prevailed the threats that exploit Microsoft Office vulnerabilities to infect devices.
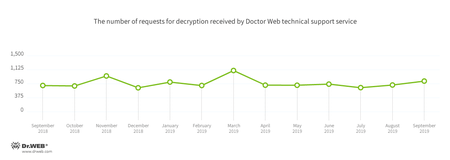
The number of requests to decrypt files affected by trojan encoders has increased. Trojan.Encoder.858 was the most active encoder, accounting for 16.60% of all incidents. Besides, the database of non-recommended and malicious websites was updated with almost twice as many Internet addresses as in August.
Principal trends in September
- Growing number of users targeted by encoders
- Advertising trojans and adware remain amongst the most active threats
According to Doctor Web’s statistics servers
The most common threats in September:
- Adware.SweetLabs.1
- Adware.SweetLabs.2
- Alternative app store and add-on for Windows GUI from the creators of Adware.Opencandy.
- Adware.Elemental.14
- Detects adware downloaded from file sharing services because of link spoofing. Instead of normal files, victims get applications that display advertising as well as install unwanted software.
- Adware.Softobase.15
- Installation adware that spreads outdated software and changes the browser’s settings.
- Adware.Ubar.13
- A torrent client designed to install unwanted programs on a user’s device.
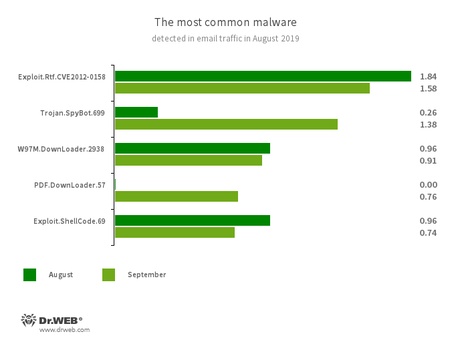
Statistics for malware discovered in email traffic
- Exploit.Rtf.CVE2012-0158
- Modified Microsoft Office document. Exploits the CVE2012-0158 vulnerability in order to run malicious code.
- Trojan.SpyBot.699
- Trojan spyware that hooks characters entered using the keyboard (keylogger).
- W97M.DownLoader.2938
- A family of trojan downloaders that exploit vulnerabilities in Microsoft Office applications and can download other malware to a compromised device.
- PDF.DownLoader.57 (new threat)
- Represents a family of trojan downloaders that spread in specifically created PDF documents.
- Exploit.ShellCode.69
- Another malicious Microsoft Office Word document, which uses the CVE-2017-11882 vulnerability.
Encoders
In September, Doctor Web’s technical support service registered 14.59% more requests to decode files encoded by trojan ransomware than in August.
The majority of cases involve the following encoders:
- Trojan.Encoder.858 — 16.60%
- Trojan.Encoder.11464 — 6.93%
- Trojan.Encoder.11539 — 5.04%
- Trojan.Encoder.25574 — 2.94%
- Trojan.Encoder.10700 — 2.52%
- Trojan.Encoder.567 — 1.89%
- Trojan.Encoder.24383 — 1.47%
Dr.Web Security Space for Windows protects against encryption ransomware
Dangerous websites
In September 2019, Dr.Web database was updated with 238,637 URLs of non-recommended websites.
| August 2019 | September 2019 | Dynamics |
|---|---|---|
| + 204,551 | + 238,637 | + 16.66% |
Malicious and unwanted programs for mobile devices
In September, we detected a lot of malware on Google Play. Earlier this month, Doctor Web virus analysts detected the banking trojan Android.Banker.347.origin that attacked users from Brazil. It hooked text messages with confirmation codes and could load fraudulent websites at the command of attackers. Another banker, found at the end of the month, was dubbed Android.Banker.352.origin. It stole the credentials of users at the YoBit cryptocurrency exchange.
Among the threats spreading via Google Play were the trojan downloaders Android.DownLoader.920.origin and Android.DownLoader.921.origin that downloaded other malicious applications. Virus analysts have also detected the Android.HiddenAds adware trojans. Besides, our experts discovered several modifications of trojans of the Android.Joker family. They subscribed users to expensive services, could hook text messages, and transmitted the contact lists of infected devices to cybercriminals. These trojans could also download and then launch auxiliary modules and were able to execute arbitrary code.
Virus analysts have also identified new versions of riskware designed for cyber spying.
The following events are among the most notable regarding mobile security in September:
- distribution of malware on Google Play;
- detection of new spyware versions.
Find out more about malicious and unwanted programs for mobile devices in our special overview.