Cybercriminals use CNET website to spread the infected VSDC installer
Real-time threat news | Hot news | All the news | Virus alerts
February 6, 2020
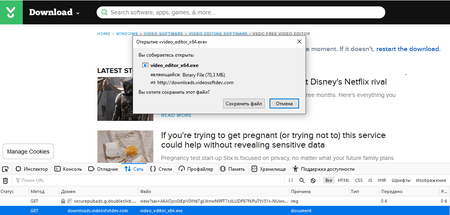
Earlier in 2019, we reported an attack on the website of the popular video editing freeware called VSDC. This time cybercriminals distribute the malicious installer through CNET's download[.]com by replacing the native download link on VSDC’s webpage with a fake one.
The compromised link leads users to downloads[.]videosfotdev[.]com, which is a spoofed domain name controlled by hackers. Target selection is based on geolocation. Non-target users are redirected to the legitimate VSDC website, while the others receive a hacked installer, but with a valid digital signature.
The infection mechanism is implemented as follows. During the installation process, in addition to the actual program’s files, the installer creates two folders in the %userappdata% directory. One folder contains a normal set of files for the TeamViewer remote control application. The second folder contains a downloader trojan that further retrieves auxiliary malicious modules from the repository. These are .dll files detected as BackDoor.TeamViewer, which allows the trojan to establish an unauthorised connection to an infected computer, as well as a script for bypassing Microsoft Windows’s built-in anti-virus protection.
Utilising BackDoor.TeamViewer, the attackers are able to deliver payload modules with malware to infected devices, such as:
- X-Key Keylogger,
- Predator The Thief stealer,
- SystemBC trojan-proxy, and
- A trojan for remote control over RDP protocol.
It should be noted that one of the repositories contains a hacked NordVPN installer. It also carries the specified malicious components and has a valid digital signature.
All mentioned threats are successfully detected and removed by Dr.Web.
Doctor Web experts recommend all VSDC users check their devices with our antivirus.