Doctor Web detects malicious apps on Google Play with over 2 million downloads
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
November 13, 2017
Doctor Web specialists detected Android.RemoteCode.106.origin in nine programs, which on average have been downloaded by at least 2,370,000 users and up to more than 11,700,000 users. The Trojan has been found in the following applications:
- Sweet Bakery Match 3 – Swap and Connect 3 Cakes 3.0;
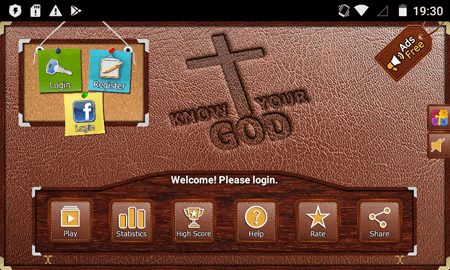
- Bible Trivia, version 1.8;
- Bible Trivia – FREE, version 2.4;
- Fast Cleaner light, version 1.0;
- Make Money 1.9;
- Band Game: Piano, Guitar, Drum, version 1.47;
- Cartoon Racoon Match 3 - Robbery Gem Puzzle 2017, version 1.0.2;
- Easy Backup & Restore, version 4.9.15;
- Learn to Sing, version 1.2.
Our analysts informed Google about the presence of Android.RemoteCode.106.origin in the detected applications. At the moment this news article was posted, some of them had already been updated, and the Trojan was no longer detected in them. Nevertheless, the remaining programs still contain the malicious component and pose a threat.
Before starting its malicious activity, Android.RemoteCode.106.origin performs a number of checks. If an infected mobile device lacks a specific number of photos, contacts and phone calls in the call log, the Trojan does not act. If the specific conditions are met, it sends a request to a command and control (C&C) server and attempts to follow the link received in an incoming message. If successful, Android.RemoteCode.106.origin makes use of its main functionality.
The Trojan downloads from its C&C server a list of modules it needs to run. One of them was added to the Dr.Web virus database as Android.Click.200.origin. It automatically opens a website in a browser, and the website address is received via the command center. This function can be used to inflate the traffic stats of Internet resources; it can also be used to perform phishing attacks if the Trojan is tasked with opening a fraudulent webpage.
The second Trojan module, dubbed Android.Click.199.origin, ensures the operation of the third component, which was added to the virus database as Android.Click.201.origin. The main task of Android.Click.199.origin is to download, launch, and update Android.Click.201.origin.
Android.Click.201.origin, in turn, after its launch, connects to the C&C server from which it receives its tasks. These tasks contain website addresses for the Trojan to open in invisible mode in WebView. After following one of the target addresses, Android.Click.201.origin independently clicks on the advertising banner indicated in the command or on an arbitrary element of the opened page. It performs these actions until it attains the assigned number of clicks.
Thus, the main purpose of Android.RemoteCode.106.origin is to download and launch additional malicious modules used to inflate website traffic stats, and also to follow advertising links. These actions bring cybercriminals a profit. In addition, the malicious program can be used to perform phishing attacks and steal confidential information.
Dr.Web for Android successfully detects all the applications containing Android.RemoteCode.106.origin, as well as its auxiliary modules, so these malicious programs do not pose any threat to our users. When software containing Android.RemoteCode.106.origin is detected, Android smartphone and tablet owners should either remove it or check to see whether an updated version, one that does not contain the Trojan’s functionality, is available.
Your Android needs protection
Use Dr.Web
- The first Russian Anti-virus for Android
- More than 100 million downloads on Google Play alone
- Free for users of Dr.Web home products