New backdoor attacks Windows users
Real-time threat news | Hot news | All the news | Virus alerts
May 6, 2016
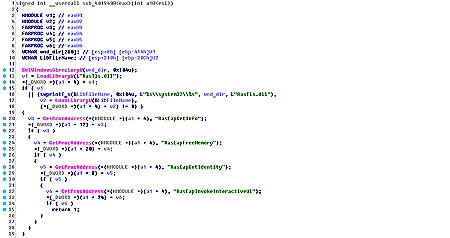
The Trojan is distributed via a dropper in the form of the Microsoft Excel file with a special macros. This macros collects a self-extracting archive by bytes and runs it. The archive consists of an executable file, which has a valid digital signature registered to Symantec, and a dynamic library, in which all the main functions of the Trojan are implemented. BackDoor.Apper.1 registers the executable file in autorun. Once launched, this file loads the malicious library into the memory of the infected computer.
BackDoor.Apper.1 is mainly designed to steal files from the machine. When the malicious application is registered to autorun, the Trojan removes the original file.
After being launched, BackDoor.Apper.1 acts as a keylogger—logs key strokes and records them into an encrypted file. In addition, the Trojan can monitor the file system. If the computer has a configuration file containing paths to folders whose status is to be monitored by the Trojan, BackDoor.Apper.1 logs all changes of these folders and sends them to the server.
Before connecting to the server, the backdoor collects the following data on the infected computer: its name, version of the operating system, and information about the processor, RAM, and drives. This information is then transmitted to the server. After that, the Trojan gathers more detailed data on the computer’s drives, which is sent to cybercriminals, together with the kelogger file. BackDoor.Apper.1 then waits for commands from the server.
To receive instructions, the Trojan sends a special request to the server. Upon a command, the malware can send a particular file or information about the specified folder, to delete or rename a file, to create a new folder, and to take a screenshot and send it to attackers.
Dr.Web successfully detects and removes BackDoor.Apper.1, and, therefore, this malicious program poses no threat to our users.