Android.ZBot banking Trojan uses "web injections" to steal confidential data
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
December 15, 2015
Android.ZBot’s first modification was detected this February. Doctor Web security researchers named it Android.ZBot.1.origin. From that time, they have been keeping a close watch on its activity.
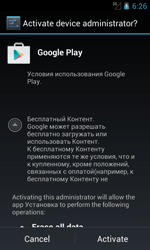
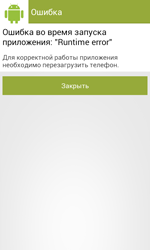
Like many other Trojans for Android, Android.ZBot.1.origin masquerades as a benign program (in this case—as the Google Play application) that can be downloaded once a user visits fraudulent or hacked websites, or other malware can download it to a device. Once the banking Trojan is installed and launched, it prompts the user to grant it administrator privileges. If the privileges are successfully granted, the Trojan displays an error message and urges the user to reboot the system.
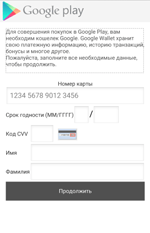
In case the user refuses to grant the necessary privileges, Android.ZBot.1.origin immediately tries to steal the detailed information on their bank card including its number, expiration date, CVV, and the card holder name. To do that, the Trojan displays a bogus dialog simulating the input form of the legitimate Google Play application. It should be noted that the Trojan shows the same dialog even if it gets administrator privileges but only in a period of time after the installation.
Then Android.ZBot.1.origin removes its icon from the home screen in order to “hide away” from the user and starts to control all system events. Thus, the Trojan is launched automatically after the gadget is turned on. Once the malicious program takes over control, it connects to the remote node to get new instructions from cybercriminals and register the compromised gadget on it. Depending on the received command from the server, the banking Trojan performs the following actions:
- Sends an SMS with a specific text to a specified number
- Makes a phone call
- Sends text messages to all user’s contacts
- Intercepts incoming SMS messages
- Tracks the current GPS coordinates
- Displays a special dialog on top of a specified application
For example, once a new compromised device is registered on the server, the Trojan receives the command to check the user’s bank account. If it detects availability of funds, it automatically transfers the specific sum of money to cybercriminals’ bank accounts. Thus, Android.ZBot.1.origin can get access to bank accounts of Android devices users and covertly steal money using special SMS commands specified by online banking services. Moreover, the victim will not have any idea about the theft, since the Trojan intercepts all incoming SMS with transactions verification codes from banks.
It should be noted that some malicious features of Android.ZBot.1.origin (for example, sending text messages) are implemented in a separate Linux library named libandroid-v7-support.so that is stored inside of the Trojan’s program package. It protects the Trojan from anti-virus detection and allows it to stay unnoticed on the device as long as possible.
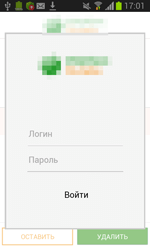
However, one of the main features of Android.ZBot.1.origin is its ability to steal logins and passwords to access online banking services using fake input forms generated on receiving the server command and designed to create an illusion that they belong to some program. Although this is a classic phishing attack, the way it is carried out in this particular case is rather unique. First, the Trojan receives the instructions that specify an application. Then it periodically begins to check whether the corresponding application is running. The Trojan currently monitors launches of the following applications:
- ru.sberbank.ivom
- ru.sberbank_sbbol
- ru.raiffeisennews
- ru.vtb24.mobilebanking.android
- PSB.Droid
- com.idamob.tinkoff.android
- ru.simpls.brs2.mobbank
- ru.kykyryza
- com.smpbank.android
- ru.ftc.faktura.sovkombank
- hu.eqlsoft.otpdirektru
- ru.ftc.faktura.sovkombank
- uk.co.danwms.fcprem
- ru.sberbankmobile
- ru.alfabank.mobile.android
- ru.alfabank.oavdo.amc
- com.openbank
- ru.ucb.android
- com.idamobile.android.hcb
- com.idamobile.android.ubrr
- com.NGSE.Ubrir
- com.citibank.mobile.ru
- com.ubrir
- ru.rshb.mbank
- com.bssys.android.SCB
- ru.bpc.mobilebank.android
- ua.privatbank.ap24.old
- ru.bspb
- com.svyaznoybank.ui
- ru.avangard
- ru.minbank.android
- ru.letobank.Prometheus
- rusfinance.mb.client.android
- com.artofweb.mkb
- com.compassplus.InternetBankingJava.wscb
- ru.stepup.MDMmobileBank
- ru.abr
- com.intervale.mobilebank.rosbank
- ru.pkb
- ru.stepup.vbank
- ru.vbrr
- com.idamobile.android.Trust
- org.bms.khmb
- ru.tcb.dbo.android
- ru.beeline.card
- ru.rocketbank.r2d2
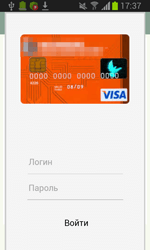
Once such application is launched, the banking Trojan, using WebView, creates a special web form, the content of which is downloaded from the сommand and сontrol server.
In particular, cybercriminals can specify the size of the displayed dialog, its appearance including a heading and a related text, the number of text fields for data input, images, and etc. The displayed form is “tied” to the attacked application. It means that if the victim of phishing tries to get rid of the shown message and return to the legitimate application dialog by tapping “Back”, Android.ZBot.1.origin will redirect the user to the home screen and close the application. As a result, the owner of the compromised device can assume that this prompt really belongs to the corresponding legitimate application and they should enter the required data. Once the Trojan gets the user’s login and password, it uploads them to the C&C server providing cybercriminals with full control over user accounts in online banking applications.
Virus makers themselves often label these malicious features as web injections, but, in fact, it is not the case—due to restrictions on Android, Trojans cannot inject an external HTML code into dialog forms of the attacked applications.
At the moment, Doctor Web security researchers have registered several modifications of Android.ZBot.1.origin that cybercriminals employ mainly against Russian users. Particularly, the first version of this Trojan detected in February is still active: only during last November Dr.Web Anti-virus products for Android detected the banking Trojan on more than 1,100 gadgets. In total, throughout the whole period of observations the Trojan was detected 25,218 times.
Android.ZBot.2.origin—another modification of the malicious program—was detected by Doctor Web security researchers in June. This version has the same features as Android.ZBot.1.origin, but its code is encrypted in order to complicate the detection procedure. In November Android.ZBot.2.origin was found on 6,238 mobile gadgets, and 27,033 cases of Android devices being infected with the malware were registered after the Trojan had been added to Dr.Web virus database.
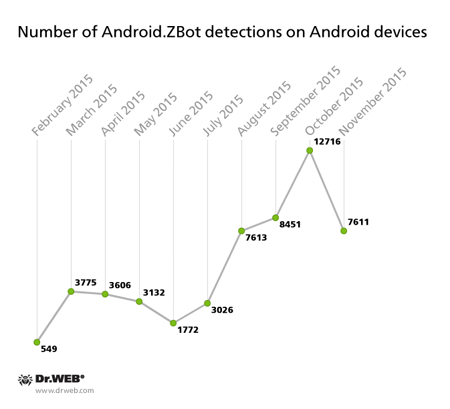
The following diagram demonstrates the dynamics of Android.ZBot detection on mobile Android devices:
During the examination of the Trojan, Doctor Web security researchers discovered that all its modifications are controlled by virus makers via different servers, the addresses of which are stored in a special database of the malicious program. As a result, devices infected by various modifications of Android.ZBot.1.origin are connected only to their remote nodes creating independent botnets. In total, Doctor Web security researchers have detected more than 20 command and control servers of the Trojan, and at least 15 of them are still active. Our security researchers have managed to get access to three subnets of the Android.ZBot.1.origin botnet. Every botnet consists of dozens and even thousands of compromised devices with their number varying from 140 to 2,300.
The large number of the active Android.ZBot.1.origin.origin’s subnets means that this Trojan is a commercial product and is distributed through underground hacker markets where it can be purchased by a single cybercriminal or by organized group of virus makers. It is also proved by the fact that the administration panel for the botnets that were created based on the devices infected by Android.ZBot.1.origin has a limited license and is used as a subscription service. We cannot exclude the possibility that fraudsters will not limit their targets to Russian users only, and not expand the geography of these attacks to other countries including Europe and the United States.
Doctor Web recommends owners of Android devices that you download applications only from trusted sources and do not install suspicious programs. Dr.Web Anti-virus successfully detects all the known modifications of Android.ZBot.1.origin for Android, so they do not pose any threat to our users.