Yet another Trojan sends out spam messages
Real-time threat news | Hot news | All the news | Virus alerts
June 3, 2015
This particular Trojan has a rather curious installation routine; that is, the malware attempts to create its copies with the names сsrss.exe, svchost.exe, and rundll32.exe in the C:\Windows\System32 system folder even though the original сsrss.exe file already exists in this directory. To solve this issue, the Trojan runs a search for the сsrss.exe process and attempts to “kill” it. If the malware acquires necessary administrator and debugger privileges, the termination of the mentioned process causes BSOD (“Blue Screen of Death”).
However, if Trojan.Proxy.27552 does not succeed in crushing Windows, it creates three files with the names сsrss.exe, svchost.exe, and rundll32.exe in the %APPDATA% folder and modifies the system registry to ensure its own autorun. In some cases, when a computer running Windows XP is infected, the malware injects its malicious code into <SYSTEM32>\rundll32.exe. In such a situation, the user can turn to the standard SFC utility to recover corrupted or missing files. This tool can help to restore an original file from its backup copy. When the next time the system is booted, all three applications created by the Trojan are launched automatically.
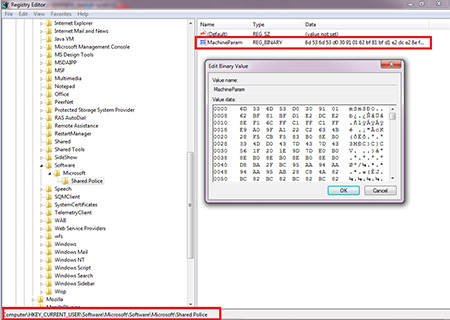
Once Trojan.Proxy.27552 is run, it checks whether there is an established Internet connection by referring to smtp.gmail.com:25 and plus.smtp.mail.yahoo.com:25. If the check returns negative result, the Trojan terminates its work. If an Internet connection is available, by sending requests to remote hosts, the malware attempts to receive a list containing valid IP addresses of command and control servers. The Trojan compares the received lists and deletes local network addresses. Then it generates a final list of command and control servers and enters this information into the Windows system registry, which is used by the malware to store such data.
Trojan.Proxy.27552 regularly updates this list. It also monitors the status of the registry branch (and, if necessary, troubleshoots any errors) responsible for the Trojan’s autorun and acts as a backconnect proxy server. The connection to the command and control servers is carried out in such a way that they actually force the infected system to maintain this connection during a specified period of time.
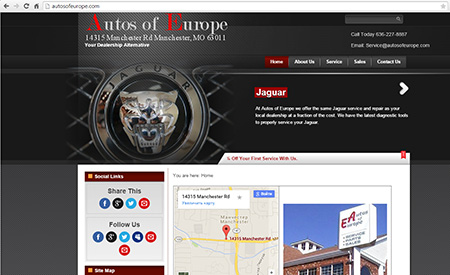
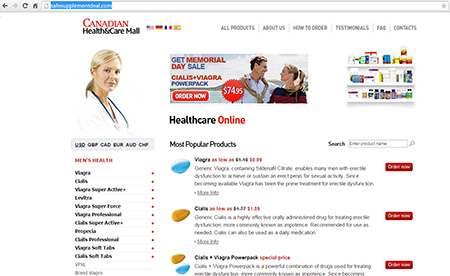
The main purpose of Trojan.Proxy.27552 is to send spam messages together with a remote spam server. Curiously enough, links from the messages sent by the Trojan direct users to hacked websites. For example, if an address contained in the message belongs to some neutral Internet resource,
...then the link redirects the user to a totally different web page.
The signature of Trojan.Proxy.27552 has been added to Dr.Web virus databases. Therefore, this malicious program poses no threat to our users.