Unwanted installer application targets users of OS X
Real-time threat news | Hot news | All the news | Virus alerts
May 18, 2015
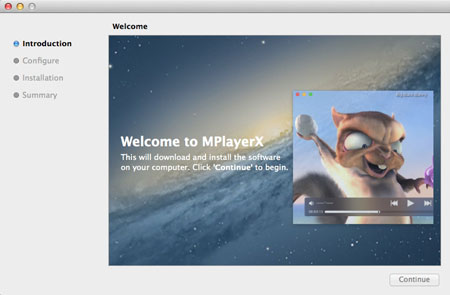
The unwanted application Adware.Mac.InstallCore.1 is an installer containing three main folders (bin, MacOS, and Resources. The first folder encompasses an application detected by Dr.Web anti-virus as Tool.Mac.ExtInstaller. It serves the purpose of installing add-ins for browsers, changing the home page or the search engine used by default. The MacOS folder contains the binary file of the installer; the Resources folder includes the main part of SDK in the form of JavaScripts. These scripts can be either encrypted with the AES algorithm or not.
In particular, among the SDK files, there is the configuration file config.js that has a special section with the information regarding what applications should be downloaded. This section possesses the information on how many applications must be installed on the system, presence of which programs and virtual machines prevents from the installation of additional programs, and the list of the components to be installed. The configuration file included in the application is not the only one the program uses for its operation. Another file is received from the remote server, whose address is specified in the local configuration file. Data downloaded from the network is encrypted with the XOR algorithm and compressed using GZIP. The decrypted file contains various data and language parameters necessary for the correct display of the interface elements.
The scripts.js file serves the purpose of checking the computer for the presence of virtual machines and some already installed applications. The malware will not urge the user to install additional programs if it runs on VirtualBox, VMWare Fusion, or Parallels or if either a development environment package XCode or the Charles application used for debugging is detected. There have been some cases, when the unwanted application did not prompt the user to install additional programs if one of the following anti-viruses was detected: AVG, Avast, BitDefender, Comodo, ESET, Kaspersky, Sophos, Symantec, Intego, ClamAV, or F-Secure. In addition, the black list of Adware.Mac.InstallCore.1 contains some other applications.
The following list presents some programs and utilities, which Adware.Mac.InstallCore.1 can install on the system:
- Yahoo Search
- MacKeeper (Program.Unwanted.MacKeeper)
- ZipCloud
- WalletBee (Adware.Mac.DealPly.1)
- MacBooster 2 (Program.Unwanted.MacBooster)
- PremierOpinion (Mac.BackDoor.OpinionSpy)
- RealCloud
- MaxSecure
- iBoostUp
- ElmediaPlayer
The signature of Adware.Mac.InstallCore.1 has been added to the Dr.Web virus databases for OS X. Therefore, our users are under reliable protection from malicious activities of this program.