Doctor Web recovers files compromised by Trojan.Encoder.398
Real-time threat news | Hot news | All the news | Virus alerts
November 25, 2014
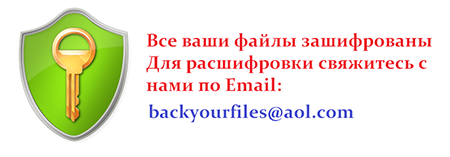
Trojan.Encoder.398 is written in Delphi and appears to be an improved version of Trojan.Encoder.225 malware. Trojan.Encoder.398 acquires encryption keys from a malicious server. When launched, the Trojan copies itself to one of the system folders as the file ID.exe, where ID is replaced by the hard drive serial number. Then Trojan.398.Encoder displays an error message about a corrupted archive and starts its own copy which then identifies the serial number of the infected system’s hard drive and forwards it to the attackers' remote server. In response, the Trojan receives an XML configuration file containing encryption parameters that include the following: The attackers' contact email and the encryption key and algorithm, as well as part of the file name extension of the compromised files. With that, the encryption process begins.
Currently, Doctor Web security researchers are aware of several Trojan.Encoder.398 modifications that can use up to 18 different encryption routines. The Trojan can encrypt files with the following extensions: .odt, *.ods, *.odp, *.odb, *.doc, *.docx, *.docm, *.wps, *.xls, *.xlsx, *.xlsm, *.xlsb, *.xlk, *.ppt, *.pptx, *.pptm, *.mdb, *.accdb, *.pst, *.dwg, *.dxf, *.dxg, *.wpd, *.rtf, *.wb2, *.mdf, *.dbf, *.psd, *.pdd, *.eps, *.ai, *.indd, *.cdr, *.jpg, *.jpeg, *.arw, *.dng, *.3fr, *.srf, *.sr2, *.bay, *.crw, *.cr2, *.dcr, *.kdc, *.erf, *.mef, *.mrw, *.nef, *.nrw, *.orf, *.raf, *.raw, *.rwl, *.rw2, *.r3d, *.ptx, *.pef, *.srw, *.x3f, *.der, *.cer, *.crt, *.pem, *.p12, *.p7b, *.pdf, *.p7c, *.pfx, *.odc, *.rar, *.zip, *.7z, *.png, *.backup, *.tar, *.eml, *.1cd, *.dt, *.md, *.dds.
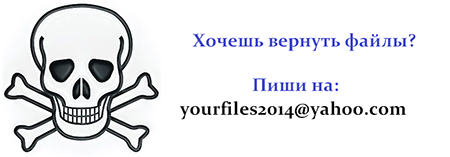
The criminals typically use the following email addresses for communication: mrcrtools@aol.com, back_files@aol.com, backyourfile@aol.com, vernut2014@qq.com, yourfiles2014@yahoo.com, restorefiles2014@yahoo.fr, filescrypt2014@foxmail.com etc.
Until recently, files compromised by Trojan.Encoder.398 couldn't be recovered; however, since May 2014, Doctor Web has been engaged in an in-depth R&D project aimed at developing effective decryption routines. Now these efforts have finally paid off. To date, Doctor Web is the only company whose researchers can with 90% probability for success recover *.filescrypt2014@foxmail.com _ * files encrypted by the malware Trojan 398 Encoder.
It should be noted that numerous offers to decrypt compromised data for a fee have appeared recently on the Web, but in most cases, the entrepreneurs behind those offers are known to turn to Doctor Web's technical support for assistance. Please note that Doctor Web recovers data free of charge for users of its commercial products. Thus, the fraudsters are actually asking this Trojan’s victims to pay for a service that can be obtained free of charge. At the very least, their fee is much higher than the price of a Dr.Web software license which, once purchased, gives users reliable protection for all their desktops, laptops and handhelds.
If your files have been compromised by this malware, follow these steps:
- Notify the police;
- Never attempt to solve the problem by reinstalling the operating system;
- Do not delete any files from the hard drives;
- Do not try to restore the encrypted data on your own;
- Contact Doctor Web technical support (this service is available free of charge);
- Attach a DOC file encrypted by the Trojan to the ticket;
- Wait for a response from a virus analyst. Due to the large volume of requests, it may take some time to receive a response.
Please note that the decryption service is only available to users who have purchased commercial licenses for Dr.Web anti-viruses. The work accomplished by Doctor Web's security researchers opens up new opportunities in the fight against encryption ransomware and gives hope that, in the future, data recovery will become available for a wider range of encryption ransomware programs.
Use Data Loss Prevention to protect your files from encryption ransomware
| Only available in Dr.Web Security Space 9 and 10 |
| More about encryption ransomware |  |
Configuration presentations tutorial |  |
Free decryption |