An overview of the most dangerous Android banking Trojans targeting South Korea
Virus reviews | Real-time threat news | Hot news | Threats to mobile devices | All the news
July 31, 2014
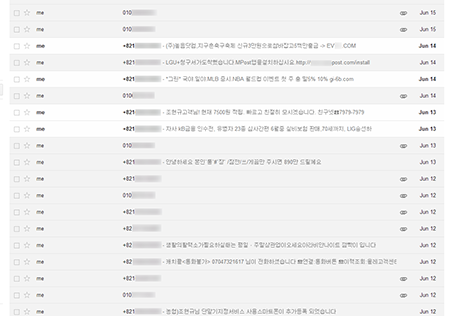
Many Android Trojans detected in over the past few months could steal all sorts of confidential information, including logins, passwords and secret codes related to accessing bank accounts and online transactions. A large portion of these Trojans not only provide criminals with information required to access victims' accounts but also enable them to covertly carry out transactions using the compromised devices.
Android.BankBot.20.origin is one such program. Distributed in the guise of various applications, it targets customers of South Korean credit organizations such as NH Bank, Shinhan Bank, Woori Bank, KB Kookmin Bank, Hana Bank, ePOSTBANK, KFCC and Busan Bank.
When launched, the Trojan prompts the user for permission to access the administrative features of the mobile device, and then removes its icon from the list of applications on the Home screen. Then the malware uses a POST HTTP request to send the following data to the remote server at http://xxx.xxx.66.249/common/servlet/SendDevice:
- Phone number;
- SIM card serial number;
- Handheld model;
- OS version;
- List of installed applications from the target financial institutions;
- Mobile operator.
Furthermore, information about the contacts found in the phone book is sent in JSON format to http://xxx.xxx.66.249/common/servlet/ContactsUpload. The request structure is as follows:
{"contacts":[{"mobile":"Example_number","name":"Example_contact"}],"mobile":"self_number"}. Here the parameter 'self_number' indicates the serial number of the compromised device's SIM card.
Upon a corresponding command from attackers, Android.BankBot.20.origin can block all incoming calls. It should be noted that calls are blocked during a specific time period, starting on 06.20.2014 and ending on the date specified in its settings.
The Trojan also intercepts incoming short messages during a specific period of time and uploads them to the server at http://xxx.xxx.66.249/common/servlet/SendMassage и http://xxx.xxx.66.249//common/servlet/SendMassage2.
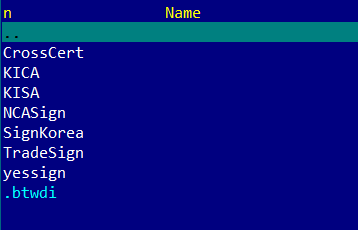
However, the main feature of Android.BankBot.20.origin is to replace legitimate remote banking applications with lookalike versions. To do this, the Trojan checks the availability of the following applications on the mobile device:
- nh.smart
- com.shinhan.sbanking
- com.webcash.wooribank
- com.kbstar.kbbank
- com.hanabank.ebk.channel.android.hananbank
- com.epost.psf.sdsi
- com.smg.spbs
- com.areo.bs
The resulting list of programs is also uploaded to a remote server at http://xxx.xxx.66.249/common/servlet/GetPkg, after which the attackers can command the Trojan to download a particular version of a fake banking application, which is placed in the directory /sdcard/Download/update. When done, the Trojan initiates installation of the downloaded software by displaying the update prompt: «새로운버전이 출시되었습니다. 재설치 후 이용하시기 바랍니다». The legitimate program, which was replaced by the fake, is removed.
The installed fakes mimic the interface of the original applications and prompt users to enter their authorisation data, so that the intruders can gain access to the bank accounts of their victims.
Intruders can also change addresses of command and control (C&C) servers by sending short messages containing new URLs: V:www.commandcenterurl.com.
Android.BankBot.20.origin carries a payload which is similar to that of Android.Banker.22.origin. However, it can replace a greater number of applications such as:
- nh.smart
- com.shinhan.sbanking
- com.webcash.wooribank
- com.kbstar.kbbank
- com.hanabank.ebk.channel.android.hananbank
- com.epost.psf.sdsi
- com.ibk.neobanking
- com.smg.spbs
- com.kftc.citismb
- com.sc.danb.scbankapp
- com.areo.bs
By default, the Trojan communicates with a C&C server at http://xxx.xxx.197.203:80.
The interface for installing fake applications via SMS is the main distinguishing feature of Android.Banker.22.origin. ДTo install fakes, the attackers send a special message with a command that has the following format'b:bank_name'. Here 'bank_name' is replaced by the name of one of the target applications to be installed: {"NH", "SH", "WO", "KB", "HA", "EP", "NE", "SP", "CT", "SC", "BS"}.
In addition to Trojans that target the clients of multiple banks, criminals also employ more specialised malicious programs. These threats include, for example, the Trojans Android.Banker.26.origin and Android.Banker.27.origin.
For example, the malicious application Android.Banker.26.origin is used by cyber criminals to compromise accounts belonging to Kookmin Bank customers. The Trojan is distributed under the same name as the original application and features the same icon, so users are likely to run the malicious program instead of the legitimate app.
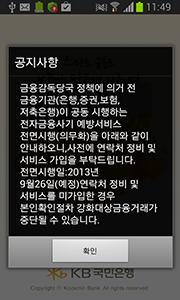
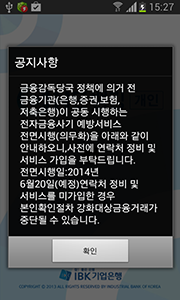
After its successful launch Android.Banker.26.origin demonstrates a fake notification informing the user that the mobile device is protected by the anti-virus AhnLab V3 Mobile Plus, thus simulating the behaviour of the original banking application which actually checks whether the system is protected.
At the same time, the Trojan checks whether NPKI-certificates are present in the root folder of the memory card of the infected device and if found, places them in zip-archives, placed next to the original files, and then displays information about the found files.
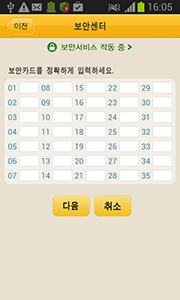
When the user taps on an item on the list, Android.Banker.26.origin prompts them to enter a password for the corresponding certificate.
The Trojan uses a very peculiar method to verify entered passwords: if the password is longer than or equal to six characters, the malware informs the victim about an error and prompts them to re-enter the password, while temporarily storing the previous value (if the input value is less than six characters, it will not be saved). If the re-entered value coincides with the previous one and is longer than six characters Android.Banker.26.origin proceeds to the next step of collecting confidential information. In particular, the malicious program prompts the user for the following credentials:
- name;
- id_first – id_second;
- account;
- account password.
If the user selects the last option—enter a password—the Trojan displays a separate field that accepts numeric values of no fewer than four characters.
Once the required data is entered, Android.Banker.26.origin invites its victim to input their credit card number.
All the confidential information collected by the malware, including certificates and the IMEI, is sent to a remote server located at http://xxx.xx.177.105:80/v/. This information is transmitted in JSON format and arranged as follows:
{:"clientId" :
"accountName" :
"accountNo" :
"accountPsw" :
"bkType" :
"certPath" :
"card" :
"transPsw" :
"certPsw" :
"personIdFirst" :
"personIdSecond" :
"fileName" :}
Android.Banker.27.origin features virtually identical payload and only differs in the target group. It is intended for customers of Hana Bank. It uploads gathered information at http://xxx.xx.78.136/PhoneManager/services/BankWebService?wsdl. This Trojan uses the library ksoap2.
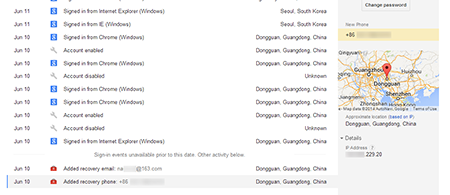
However, resourceful and energetic cybercriminals are not resting on their laurels; they are continuing to refine their devious tricks. For example, the many design concepts and technical solutions implemented in different versions of existing South Korean banking Trojans were realised in another Android threat dubbed Android.Banker.28.origin by Dr.Web. This malware is disguised as a Google Play client, and, after its launch, it requests administrator privileges on the mobile device. After that it removes its icon from the list of applications on the Home screen and displays a message about an alleged error and the removal of the program.
The Trojan then searches the root directory of the memory card for the directory NPKI, which contains the digital certificates that ensure the safety of financial transactions, and places its contents in a zip-archive, which is forwarded to the email-address jnohiugb[xxxxx]@gmail.com and uploaded to the server ml[xxx].iego.net using an embedded ajax-library.
After that Android.Banker.28.origin checks whether the following programs are installed on the compromised device:
- com.shinhan.sbanking
- com.kbstar.kbbank
- com.hanabank.ebk.channel.android.hananbank
- nh.smart
- com.webcash.wooribank
- AhnLab V3 Mobile Plus 2.0
Information about all the applications found, as well as the phone number, is transmitted to a remote server.
The Trojan then collects information about all the contacts in the phone book and puts the data into the file sdcard/phone001.txt. The file stores data in the following format:
number:"Example_phoneNumber";name:"Example_contact.
In addition, all incoming short messages are placed in the separate file sdcard/temp/sms.txt. The messages are arranged in the file as follows:
name:"Example_name";phone:"Example_phoneNumber";content:"Example_content";date:"Example_date".
Both of these files are uploaded to the intruders' server. In addition, all new incoming messages are also intercepted and forwarded to the criminals.
Unlike most South Korean banking Trojans that remove the original versions of banking applications and install fake copies of them, Android.Banker.28.origin employs a more unusual technique to steal authentication data. At regular intervals, the Trojan checks whether one of the required banking applications is running and, if it is, the malware displays several messages and then imitates a dialogue prompting the user to enter their account information, which is then archived and forwarded to attackers.
The requested information includes:
- clientId (IMEI);
- accountName;
- AccountNo (account number);
- accountPsw (password);
- bkType (bank name abbreviation);
- card (card number);
- transPsw;
- certPsw (certificate password);
- personIdFirst;
- personIdSecond.
To ensure its safety, Android.Banker.28.origin regularly checks the device for the presence of the anti-virus AhnLab V3 Mobile Plus. If the anti-virus is found, it is removed.
Criminals can send various commands to the Trojan in SMS messages. In particular, the malware can receive the following directives:
- ak49 – send all the gathered information and change the target server (the new server address is specified as a corresponding command option).
- ak40 – enable or disable the forwarding of inbound SMS to a specified email (options "1" and "2" respectively).
- wokm – broadcast SMS messages to all available contacts (message text is specified as the command option).
- ak60 – change the email address to which the collected information is sent (the address is specified as a command option).
- ak61 – change the email account password (the password is specified as a command parameter).
It is noteworthy that the instruction wokm enables Android.Banker.28.origin to operate as an SMS worm (if the sent message contains a link to download the Trojan).
In addition to these malicious programs, South Korean mobile banking users are currently being threatened by many other similar Trojans whose numbers are constantly growing. They make use of improved techniques for stealing confidential information. The following tips can help South Korean users to maintain reliable security:
- Control all operations involving your bank accounts;
- Change the password used to access your account information regularly;
- Use banking software obtained from trusted sources;
- Do not open suspicious links, and never install suspicious applications;
- Protect your Android-powered device with a modern anti-virus.
Learn more with Dr.Web
Virus statistics Virus descriptions Virus monthly reviews Laboratory-live