Turkish backdoor receives commands by analysing web-page code
Real-time threat news | Hot news | All the news | Virus alerts
June 10, 2014
BackDoor.Zetbo.1 is installed into a system under the guise of the Windows Power Management service (winpwrmng) which has the following description: Allows Users to Manage the Power Options. The backdoor is saved onto the hard drive as the executable taskmgr.exe which stores all its files in %APPDATA%\Roaming\. When installed, BackDoor.Zetbo.1 displays the following message in Turkish: rundll bu dosyay? acam?yor. Dosya cok buyuk, which can be translated as "rundll cannot open this file. The file is too big".
Once started on an infected PC, the malicious service ensures that the backdoor is working; if not, it forces it to be launched. If a user tries to stop the service, the Trojan terminates Windows and displays the message “Windows had to be closed”. Windows Power Services is turned off.
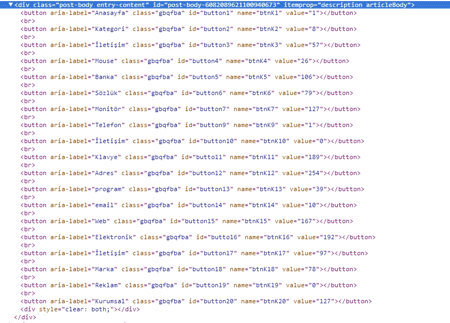
The main objective of this malicious program—to execute various commands from a command and control (C&C) server on an infected machine—is quite typical of backdoors. The server address is hardcoded in the bot's body, and the instructions the Trojan carries out include updating, deleting files, searching for its own components on the hard drive and shutting down the system. The backdoor can also transmit to the server various system information (e.g., the hard drive serial number). It should be noted that the malware uses a non-trivial method to acquire its operational parameters from the C&C server. BackDoor.Zetbo.1 connects to a remote host and requests a special web page featuring several buttons. By analysing the HTML code responsible for displaying these buttons, the malware defines the parameters necessary for its operation.
The signature of BackDoor.Zetbo.1 has been added to the Dr.Web virus database, so this malware poses no danger to systems protected by Doctor Web anti-virus products.