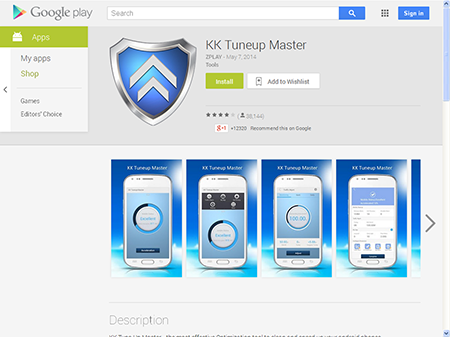
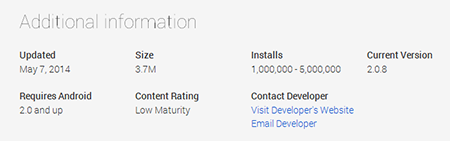
Dangerous application downloaded over a million times from Google Play
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
May 26, 2014
The program in question is another optimisation utility that can modify a device's settings and facilitate access to some of its features. In particular, the program works as an application manager (installing and removing programs and creating backups); it can 'clean the memory' and control Internet traffic.
However, in addition to these features, it can also carry out some covert actions; for example, it can download applications and send messages to premium-rate numbers. For these purposes, the utility uses several suspicious services that are activated after its launch. One of them is used to communicate with a remote server to which it relays information about the device (the IMEI and IMSI) and receives such directives as:
- Generate an application download list;
- SMS message parameters (text and recipient number);
- Create a list to intercept specific incoming messages (this list contains the sender's numbers and SMS text).
Another service is directly involved in installing applications. Using the command pm install, it uses the previously generated apk-file list to download and discreetly install programs. This command is available on devices with enabled root access. If the necessary system privileges are not available, the installation can be performed in standard mode, requiring confirmation from the device's user.
Despite the fact that background installation can be used for legitimate purposes, such as porting applications from one mobile device to another, it can also be employed to install programs without user consent. As for automatic SMS sending, this feature is directly activated by an order issued by the command and control server and can't be controlled by the user. Due to the presence of these dangerous features, Doctor Web's virus analysts decided to classify this utility as malicious and to add it to the virus database as Android.Backdoor.81.origin.
At the time of the program’s discovery on Google Play, it had been downloaded more than one million times, and many users have already run into the problem of SMS messages being sent to premium numbers without their consent. As of May 26, the program was still available for download via Google Play.
To avoid the unpleasant consequences of actions taken by malicious and potentially dangerous programs, users are advised to check what privileges a program requires before installing it on their device and also to use a current anti-virus for Android.