December 24, 2013
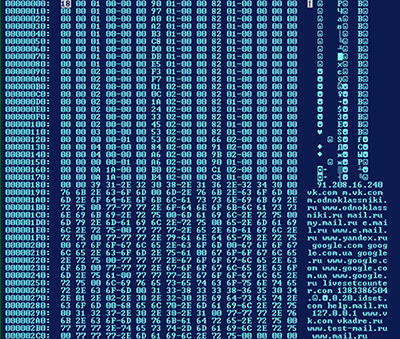
You may recall that Trojan.Mods programs were found in large numbers in the wild in spring 2013 and were primarily designed to intercept browsers' DNS queries and redirect users to malignant sites. As a result, instead of the requested sites, users end up on fraudulent pages whose URLs in the browser address bar appear to be official, so victims may not immediately recognize the fraud.
Previous versions of Trojan.Mods injected malicious code into processes of Microsoft Internet Explorer, Mozilla Firefox, Opera, Safari, Google Chrome, Chromium, Mail.Ru Internet, Yandeks.Browser, and Rambler Nichrome, while the Trojan.Mods injects its code into explorer.exe, which then searches for running browser processes and also attempts to inject malignant code into them. Previously, this code was implemented as a separate dynamic library.
Furthermore, Trojan.Mods.10 contains a module designed to mine bitcoins, which coincides with the recent major trend—it is the third mining Trojan discovered by Doctor Web in December 2013.
The signatures of the threats described above have been added to the Dr.Web virus database and therefore the Trojans pose no danger to computers protected with Dr.Web anti-virus software.

![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments