Trojan.Proxy.23012 – universal spam machine
Real-time threat news | All the news | Virus alerts
October 9, 2012
Trojan.Proxy.23012 is downloaded to infected computers by other malicious programs such as Trojan.PWS.Panda.2395. The Trojan executable file is compressed with the same viral packer that is used by Trojan.PWS.Panda programs, also known as Zeus and Zbot, so often it is detected by their signature.
Once Trojan.Proxy.23012 has gotten into the system, it is unpacked and loaded into memory, and then its installation begins. The installation folder for this malicious program depends on the operating system version and the privileges of the account under which the installer is run. In any case, the installer modifies the Windows Registry to make sure the Trojan is launched automatically at Windows’ startup. The malware also tries to disable the UAC. At the final stage of the installation process, the Trojan code is injected into explorer.exe.
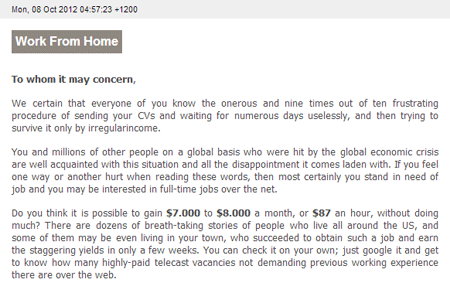
The botnet, consisting of Trojan.Proxy.23012-infected computers, is used by criminals to control proxy servers for the purpose of using them to send spam upon command An example of such a spam message is shown in the screenshot below.
Once the program establishes a connection to a remote command center, Trojan.Proxy.23012 creates upon the criminals’ command a tunnel that enables the virus writers to use SOCKS5, SOCKS4, and HTTP (including GET, POST and CONNECT routines). To send spam, criminals use gmail.com, hotmail.com, and yahoo.com smtp services.
A distinctive feature of this malware is the way bots interact with the botnet control server which selects in real time the hosts through which a particular mailing is performed. In addition, bots installed on computers without an external IP address can act as proxy servers too. This Trojan has another peculiar feature: it uses only one control server address, and if that is blocked, the Trojan can be updated via the Trojan.PWS.Panda.2395 peer network.
The signature of the threat has been added to the Dr.Web virus database, so Trojan.Proxy.23012 does not pose a serious threat to systems protected by Doctor Web products.