Trojan.Encoder heads West
Real-time threat news | Hot news | All the news | Virus alerts
April 12, 2012
Trojan encoders are well known to Russian Windows users: the first Trojan.Encoder.94 modification widespread in January 2011and took a special place in the ransomware niche along with blocker Trojans. Encoder search for user's files, in particular, Microsoft Office documents, music, photos, images and archives on disks available in the infected system and then encrypt them. Criminals demand that the user pay a certain amount to decrypt the files.
For a long time only users in Russia and other CIS countries suffered from the actions of such Trojans, but a few days ago, three new Trojan.Encoder.94 modifications targeting users in other European countries were discovered. We can assume that their authors have chosen to follow makers of Trojans Winlock malware who for a long time distributed their "works" exclusively on the Russian territory, and only at a certain moment decided to advance to the international market.
The Trojan features the English interface, but infections have been registered in Germany, Italy, Spain, England, Poland, Austria, Norway, Bulgaria and other countries. First requests from Trojan.Encoder.94 victims outside Russia were received on April 9-10, 2012.
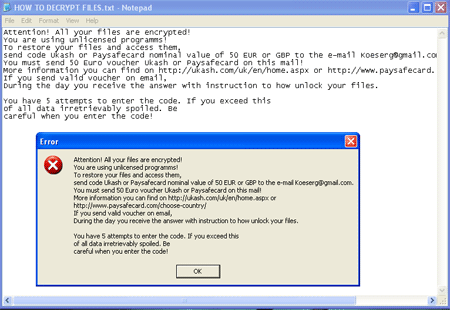
Once user files are encrypted , the Trojan displays a demand to pay 50 euros or pounds to criminals via Ukash or Paysafecard. Three English-language versions of the Trojan known to Doctor Web differ only in the encryption keys they use and operate in a similar way.
The penetration mechanism used by Trojan.Encoder.94 modifications to get to users' computers is still not thoroughly understood, but it can be assumed that attackers resort to Trojan downloaders and exploit known vulnerabilities. Doctor Web analysts are investigating this issue.
To minimize the damage from an infection by Trojan.Encoder.94, Doctor Web recommends users to back up all the files they need for their work. If your files have been compromised by the Trojan, use the following guidelines to avoid possible data losses:
- Never attempt to solve the problem by reinstallling the operating system.
- Do not delete any files from the hard drives.
- Do not try to restore the encrypted data on your own.
- Contact Doctor Web's technical support. When file a request, select Request for curing. This service is provided free of charge.
- Attach a doc or. txt file encrypted by the Trojan to the ticket.
- Wait for a response from a virus analyst. Due to the large number of requests it may take some time.