March 2, 2012
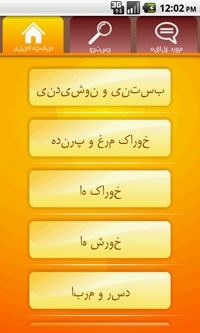
This malware has allegedly been developed in Iran and spreads under the Iranian Foods name via third-party sites providing access to a collection of software for Android. Unlike many other Trojan horses for this platform, Android.Moghava doesn't aim at bringing profit to criminals.
The malicious payload is contained in a module installed as a service named stamper. This service starts periodically and searches for JPEG images on a memory card connected to the device, particularly in the /DCIM/Camera/ folder, which by default stores photos made with the phone camera. If the Trojan horse finds image files in the folder, it adds a Ruhollah Khomeini portrait to all the images.
|

|

| |
Despite the fact that the threat signature has been added to the virus database used by Dr.Web for Android Anti-virus + Anti-spam and Dr.Web for Android Light and the Trojan horse is successfully removed during scanning, damaged photos in most cases will not be restored. In addition, unauthorized modification of image files significantly increases their size, which reduces memory card free space significantly or may leave no free space at all.

![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments