December virus activity review from Doctor Web
Virus reviews | All the news | Virus alerts
January 11, 2009
Doctor Web presents the virus activity review for December 2008. The last month of the passed year confirmed forecasts of the annual review. In particular it saw an increase of e-mails spreading malware as well as a rising number of phishing attacks. Social networking web-sites remained among main tools of cyber-criminals seeking to lure users into downloading Trojans and other malicious programs.
Windows updates
In December Microsoft released another critical update for Windows aiming to close the vulnerability of an XML parser. The reason behind the prompt updating was an exploit spreading over the Internet. The exploit is classified by Dr.Web as Exploit.CVE2008.4844. It checks if Internet Explorer is available in Windows XP and Windows 2003 Server and creates a malformed XML tag which, when parsed, starts downloading and installation of malicious programs.
Block of access to documents
The last month of 2008 was also marked with several samples of malware that could block access to documents for a user. Trojan.Locker.8 renamed files and folders using names that violated Windows standards making the files and folders inaccessible. The Trojan was spread as a registration key generator for software by Adobe Systems
Trojan.Encoder.33 came as a modification of malicious programs that would encrypt documents. However, this Trojan also moved encrypted files to new folders created in the user profile directory. Original files were replaced with the "FileError_22001" message so that a file containing text was replaced with a text message while an image was changed for an image. Doctor Web promptly released utilities returning files compromised by the Trojans to their original state.
E-mail
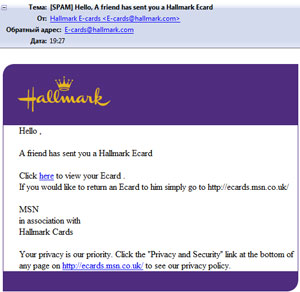
Virus makers kept spreading malicious programs as greeting cards. So e-mails supposedly sent by Hallmark provided a user with a direct link to a self-extracting archive containing a malicious program and a number of system utilities used by the malware. The program entered the Dr.Web database as Trojan.Runner.15.
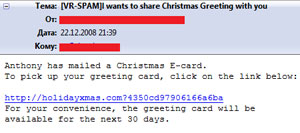
Senders of such “e-card notifications” also took advantage of Christmas. Last days of December saw a lot of messages containing links to a web-site where one could download a promised Christmas card. In truth all links provided on the bogus web-site were download links to malicious programs detected by Dr.Web software as Spambot.4202, Trojan.Spambot.4204, Trojan.Spambot.4214 and Trojan.Promo.42.
Social networking web-sites
Messaging mechanisms of social networking web-sites are also used in various fraud schemes. Many regular visitors of the Russian social networking web-site Vkontakte.ru received messages from a special account notifying a user that he could receive bonus money. A victim was directed to a fraudulent web-site featuring the same design as the original social networking web-site. Further the victim was prompted to enter his or her login and password. After that a user was displayed a piece of text describing terms of the special offer and asking to download a piece of software and install it on a cell phone.
Of course there was no bonus for a user and the installed software detected by Dr.Web as Java.SMSSend started sending paid SMS.
Phishing
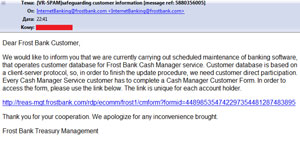
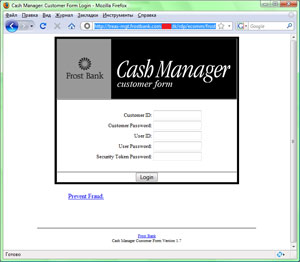
In December Internet fraudsters also often resorted to phishing e-mails targeting customers of JPMorgan Chase Bank, Frost Bank and eBay users.