Android.SmsSend modifications increased ten-fold in 2011
Virus reviews | Real-time threat news | All the news
August 24, 2011
A research by Doctor Web's analysts shows that the makers of Trojan horses from the Android.SmsSend family, known since August 2010, use the same fraudulent scheme as the one adopted to distribute Trojan.SmsSend for desktops.
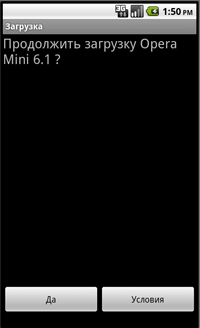
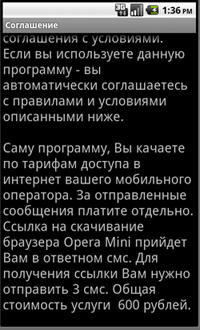
A victim downloads an application from a web-site, e.g. the downloaded program is Opera Mini. During installation the user is prompted to send several short messages to continue the installation. A reply usually contains a link and a password that the victim needs to enter on a bogus web-site. After that, they are given an opportunity to download the full distribution of the software they need. The essence of the fraud is that the user can download the application free of charge from its developer's site rather than pay criminals for downloading.
 |
 |
 |
The simple architecture of Android.SmsSend allowed virus makers to design a large number of Android.SmsSend modifications.
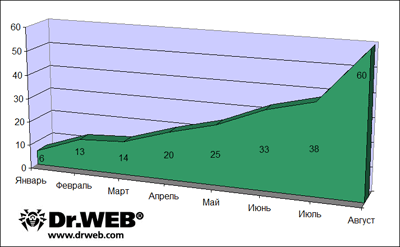
Special "partner" programmes and constructors enable children unfamiliar with programming basics to make their own versions of Android.SmsSend. At the beginning of 2011 the Dr.Web virus databases listed a total of six variants of this Trojan horse, but for now they number over 60. In other words, the number of Android.SmsSend increased tenfold in seven months. The number of new modifications sent to Doctor Web's virus laboratory in August 2011 also rose dramatically— 22 previously unknown versions of the Trojan horse have been found since the beginning of the month against the average 5-7 per month. Thus, we can talk about a 36-percent rise in the number of Android.SmsSend versions in August 2011.
Obviously, such a sharp increase goes along with the popularity of the cost-effective fraud scheme which includes production and distribution of these Trojan horses and easy profit obtained by deceiving careless users whose mobile devices have been infected. It is likely that this trend will persist. The graph below shows how the number of detections of new Android.SmsSend versions grew through the year.
Virus writers periodically change the source code of their applications in order to avoid detection by anti-virus software. Currently, Dr.Web for Android Anti-virus&Anti-spam and Dr.Web for Android Light equppped with the unique technology Origins Tracing™automatically detect these threats and their modifications. Users of mobile devices running Android are recommended to search the web for information about programs they want to install and never send messages to pay for applications they know to be available free of charge. Additionally, download applications only from trusted resources such as the official Android Market to make sure no malware gets onto your device.