New Trojan horse for Android spreads with Angry Birds Rio Unlock
All the news | Virus alerts
June 10, 2011
The beginning of June 2011 saw the emergence of a large number of new malicious programs for the mobile operating system Android. Virus makers' Interest in this OS is not accidental. Pest applications steal confidential information about the cell phone's owner, covertly send short messages to paid service numbers and perform promotional mailings which helps enrich intruders one way or another.
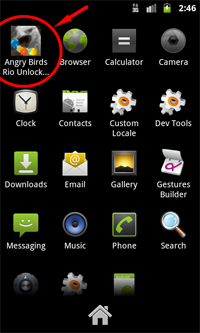
On June 9 Doctor Web's virus analysts added an entry to the virus database that concerned the new Trojan horse for Android — Android.Plankton. The threat stands out among malicious programs for Android because here a malicious object is built into the application Angry Birds Rio Unlock, opening up access to the hidden level of the popular game Angry Birds for various mobile platforms. From the Android Market alone the infected program was downloaded more than 150,000 times, and on alternative resources (in particular, at androidzoom.com, the famous collection of applications for Android) the number of downloads reached 250,000
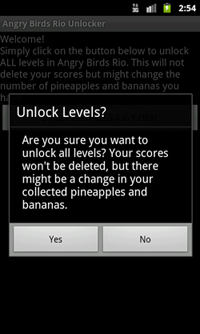
Unlike the malicious application Android.Gongfu, discovered one day earlier, the new Trojan horse Android.Plankton does not exploit known vulnerabilities in operating systems to elevate its own privileges. It attacks a system as follows: immediately after the launch of the infected application the Trojan horse in the background downloads its own service, which collects information about the compromised device (device ID, the SDK version, information about the privileges of the file) and sends it to a remote server.
Then, the malicious program gets data for the bogus site to download and install on the victim's smart phone another application whose features, according to the analysts, may vary. At present, Doctor Web knowns about several types of such malware. In particular, these are the plankton_v0.0.3.jar and plankton_v0.0.4.jar packages, designed to run on an infected device and receive commands from a control center.
To date, all known versions of the Trojan horse are added to the Dr.Web virus database, so Android.Plankton doesn't pose the danger to users of Dr.Web for Android Anti-virus + Anti-spam and Dr.Web for Android Light.
Since Android.Plankton has become extremely widespread due to a significant number of downloads of the infected applications, Doctor Web continues to closely monitors the situation. If new Android.Plankton modifications are discovered, they will be promptly added to the Dr.Web virus database.