Brazilian users’ mobile devices attacked by a banking Trojan
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
December 6, 2018
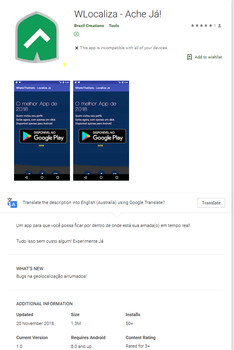
Cybercriminals were distributing Android.BankBot.495.origin under the guise of applications that supposedly allow you to monitor Android-based smartphone and tablet users. The Trojan was hidden in the following software: WLocaliza Ache Já, WhatsWhere Ache Já, and WhatsLocal Ache Já. After Doctor Web’s experts informed Google, the company promptly removed the programs from Google Play. The Trojan was downloaded by more than 2,000 users.
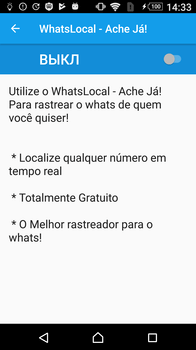
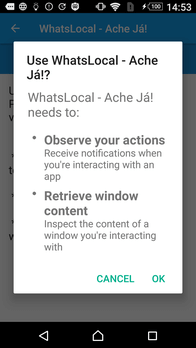
When launched, Android.BankBot.495.origin attempts to gain Android Accessibility features by opening system settings and prompting the user to activate the Accessibility option. If a potential victim agrees to grant the Trojan privileges, Android.BankBot.495.origin will be able to control the programs in the background, tap buttons, and steal the contents of the active application windows.
When the user permits the Trojan to access accessibility features, it closes the window, starts the malicious service, and uses it to continue operating in the background. Android.BankBot.495.origin then requests access to display screens over running programs. This option will later be needed to display phishing windows. The previously obtained permission to use the accessibility features helps Android.Bank.Bot.495.origin automatically tap all buttons with the text "PERMITIR" ("Allow") that appears when requesting permissions. As a result, if the system language is Portuguese, the Trojan secures the necessary privileges by itself.
Moreover, the malware uses the special features for self-defense, tracking a number of antiviruses and utilities. When they launch, it tries to close their windows by pressing the “back" button 4 times.
Android.BankBot.495.origin connects to a remote host to accept the initial settings and follows the link given by the virus writers in an invisible WebView window. After several redirections, the Trojan receives a final link with the encrypted IP addresses of two command and control servers. Android.BankBot.495.origin then connects to one of them and accepts a list with app names. The Trojan checks whether they are installed on the device and notifies the server. The Trojan then sends several specific requests one by one. Depending on the server settings, Android.BankBot.495.origin then receives a command to start one of the apps. At the time of our analysis, it could run software of the following financial institutions: Banco Itaú S.A. and Banco Bradesco S.A., as well as the default SMS application.
When the Banco Itaú is launched, the Trojan uses the accessibility feature to read the contents of its window and transfer information on the balance of the user's bank account to the attackers. It then navigates to account management in the application, where it copies and sends the iToken key, a security code used to verify electronic transactions, to the virus writers.
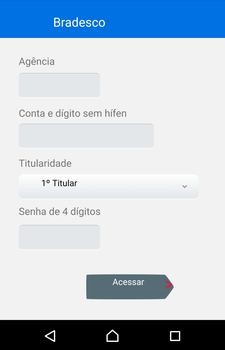
Upon startup of Bradesco, the Trojan reads the victim’s account information and tries to automatically login to it by entering the PIN code received from the command and control server. Android.BankBot.495.origin copies the balance of the user's account and, together with the account information received earlier, transfers it to cybercriminals.
Upon receiving a command to launch an SMS application, the Trojan opens it, reads and saves the text of the available messages and sends them to the server. It also recognizes the messages from CaixaBank S.A. and transmits them in a separate request.
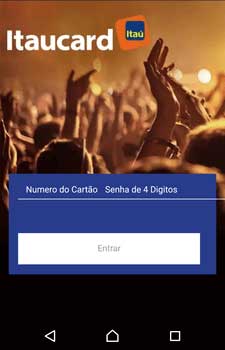
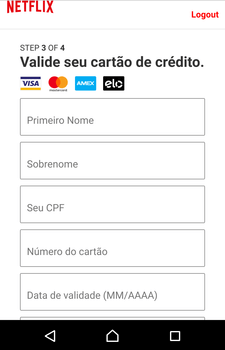
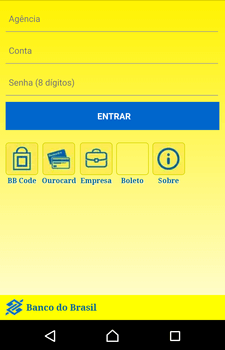
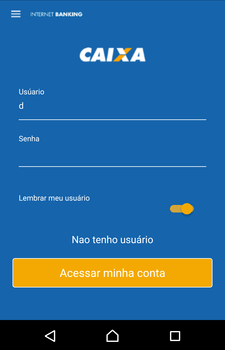
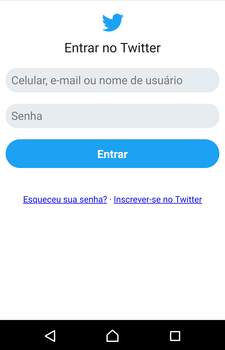
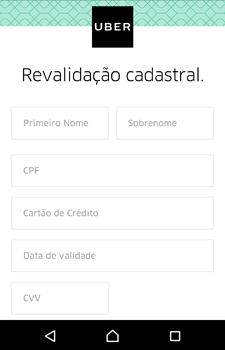
Cybercriminals also use Android.BankBot.495.origin to perform phishing attacks. The Trojan monitors the following software: Itaucard Controle seu cartão, Banco do Brasil, Banco Itaú, CAIXA, Bradesco, Uber, Netflix, and Twitter. If the Trojan detects that one of them has been launched, it displays an overlay window with a fraudulent web page simulating the attacked app, loaded from the second command and control server. The user may be prompted to enter the information on their account, bank account number, bank card details, logins, passwords, and other confidential information.
See an example of such phishing pages below:
Confidential information, entered by the victim, is transmitted to the attackers, and then the Trojan closes the fraudulent window and re-launches the compromised application in order not to raise suspicion from the user for collapsing and closing the app.
Doctor Web recommends you install Android software with extra care, even if you obtain them from Google Play. Attackers can fake well-known software, as well as create seemingly harmless applications. To reduce the risk of installing a Trojan, you should pay attention to the name of the developer, the date when the app appeared on Google Play, the number of downloads, and reviews from other users. In addition, please use an antivirus.
All known modifications to the Android.BankBot.495.origin banking Trojan have been successfully detected and removed by Dr.Web for Android, so they do not pose any threat to our users.
#Android, #Google_Play, #banking_Trojan, #phishing