November 23, 2018
By itself, Trojan.Click3.27430 is of no particular interest; it is a regular Trojan clicker that artificially increases website traffic. What is much more interesting is the method attackers use to install the malware on the devices of their potential victims.
The Trojan targets users of DynDNS software, which allows a subdomain to be bound to a computer that has no static IP address. The virus writer created a dnsip.ru webpage from which this program can allegedly be downloaded for free. The virus writer also owns the dns-free.com domain, and it automatically redirects visitors to dnsip.ru.
The website does indeed make an archive available for download. The archive contains the executable file setup.exe, which in reality is not a DynDNS installer, but a downloader. It stores the name of the file downloaded from the Internet; in our sample this was Setup100.arj.
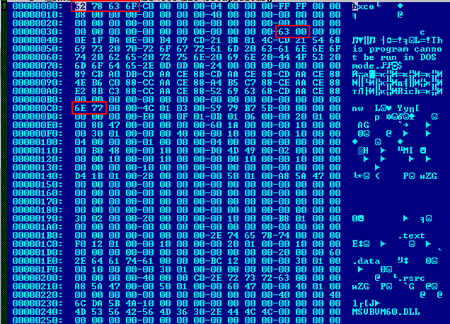
Despite the telltale extension, Setup100.arj is not an ARJ archive, but an executable MZPE file that has had three of its values modified so that it is not recognized as MZPE by automated analysis tools and other applications.
First, it uses PowerShell to disable Windows Defender, and, for greater reliability, it makes changes to the registry keys running this program.
Then the dropper saves the files instsrv.exe, srvany.exe, dnshost.exe, and yandexservice.exe to the System32 folder. Instsrv.exe, srvany.exe, and dnshost.exe are Microsoft utilities for creating user-defined services in Windows, while yandexservice.exe is the Trojan.Click3.27430 itself. Then the dropper registers the executable file yandexservice.exe, which implements the malicious features of Trojan.Click3.27430 as a service named “YandexService”. Upon installation, the service is added to the Windows Autorun list. When the dropper saves and launches the malicious service, it installs the DynDNS application. If the user decides to uninstall it from their infected computer, only DynDNS will be removed; meanwhile, Trojan.Click3.27430 will remain in the system and continue its malicious activity.
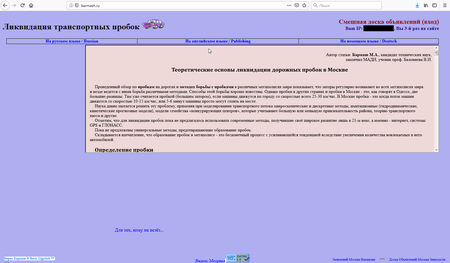
The malware analysts also investigated another component of the Trojan: the executable file dubbed dnsservice.exe, which is also installed on the infected computer as a Windows service named DNS Service. The specific debug lines that the virus writer forgot to delete in his malware programs are a giveaway:
C:\Boris\Программы\BDown\Project1.vbp
C:\Boris\Программы\BarmashSetService\Project1.vbp
C:\Boris\Программы\Barmash.en.new\Project1.vbp
C:\Boris\Программы\Barmash_en_Restarter3\Project1.vbp
This component is distributed as the file dnsservice.arj, which is disguised as an archive from barmash.ru.
All known modifications of Trojan.Click3.27430 are detected and removed by Dr.Web, and the websites dnsip.ru, dns-free.com, and barmash.ru have been added to the SpIDer Gate web anti-virus’s list of non-recommended Internet resources.
According to data gathered by Doctor Web, as of now, about 1,400 users have been affected by this Trojan, with the first infections occurring in 2013. The complete list of indicators of compromise can be found here.
#clicker #Trojan
![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments