April 16, 2018
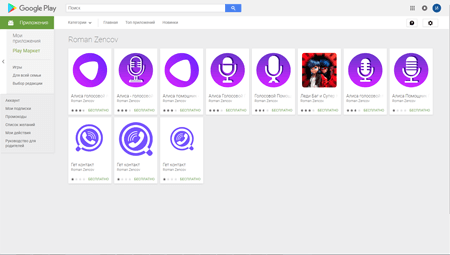
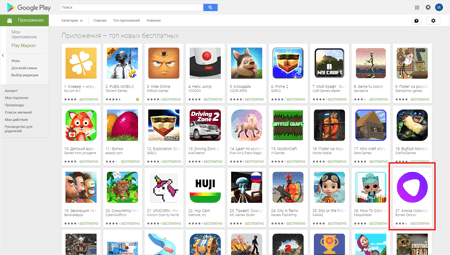
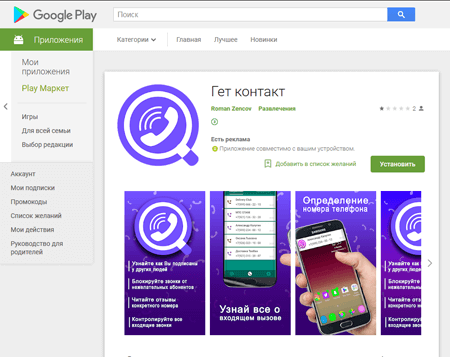
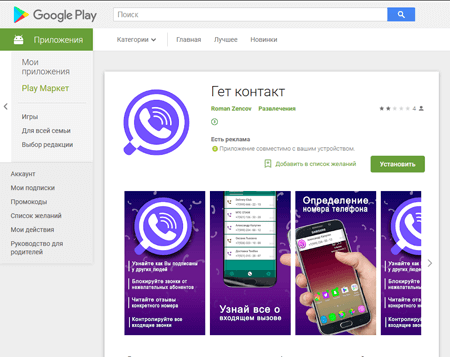
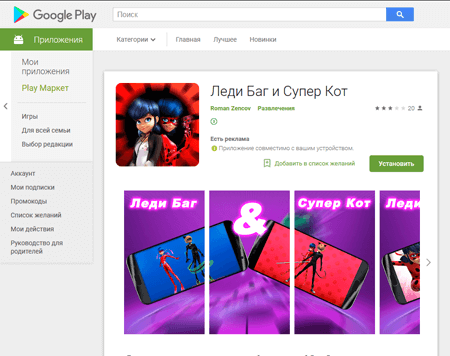
Cybercriminals distributed Android.Click.245.origin on behalf of developer Roman Zencov and disguised the Trojan as popular applications. Among them, the Miraculous Ladybug & Cat Noir game that has not been released on Android yet, the GetContact app for making calls and storing telephone numbers that became famous in the early spring, and the virtual assistant, Alice, embedded in Yandex applications, which is not available as a separate app yet. One of the Trojan programs was in the top 30 new popular apps on Google Play.
Doctor Web specialists have informed Google about the Android.Click.245.origin, and it was deleted from Google Play. Over 20,000 users downloaded fake applications. None of these programs had useful functions. Their only goal was to load webpages on the command of cybercriminals.
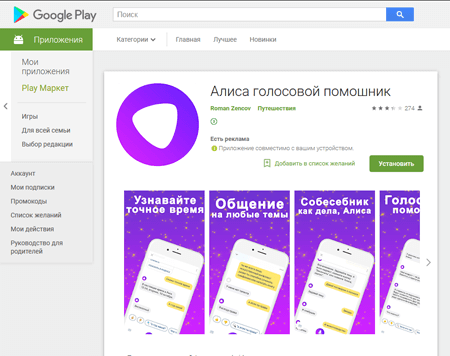
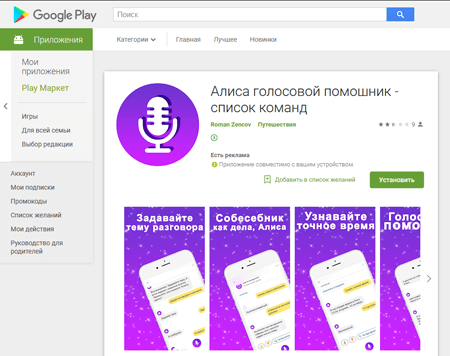
The pages of malicious applications found on Google Play are displayed below:
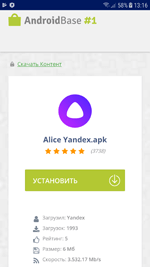
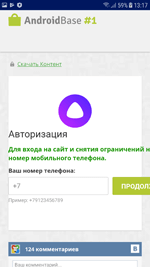
Once launched, Android.Click.245.origin establishes a connection with the command and control server and waits for the task. Depending on the IP address of the connected device, the Trojan gets a link to a particular website that must be loaded. The malicious program follows this link and displays a specific page using WebView. If the device is connected to the Internet via Wi-Fi, the user is invited to download an application by clicking the corresponding button. For example, if a victim runs the fake virtual assistant program, Alice, a file called “Alice Yandex.apk” is prepared for downloading.
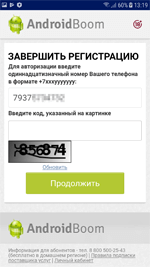
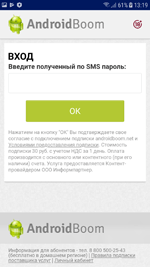
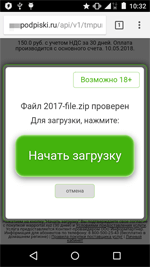
When attempting to download the file, the user is asked to enter his phone number for some authorization or download confirmation. Upon entering the phone number, the user receives a confirmation code that must be entered on the website to complete the “download”. The victim is then subscribed to a paid service rather than getting the intended program.
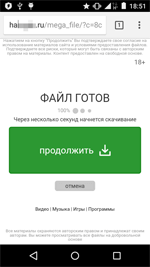
If the infected device is connected to the Internet via a mobile connection, the website loaded by the Trojan makes several redirections. Android.Click.245.origin then finally opens the website in Google Chrome. On this loaded page, the user is invited to click “Continue” to download a file. He is then redirected to another website where the download is supposed to start. Upon clicking “Start download”, the victim is automatically subscribed to one of the expensive services requiring daily payment using the Wap-Click technology. In addition, access to services like that is granted without having to enter a phone number or receiving a confirmation code via SMS.
If the Trojan does not get the task, it downloads several pictures from the Internet and displays them on the screen.
Subscription to unwanted services is one of the most popular and well known source of illegal income for cybercriminals. However, subscribing to such premium services via Wap-Click is especially dangerous because the user is not informed about new subscriptions in any way. Dishonest content providers often use this scheme to trick people into subscribing.
To save money, smartphone and tablet owners should be careful when browsing websites and not click any suspicious links or buttons. Users should also install software distributed only by known and reliable developers and use anti-virus.
Dr.Web for Android has successfully detected all known modifications of Android.Click.245.origin, so the Trojan does not pose any threat to our users.
#Android, #Google_Play, #mobile, #paid_subscription, #fraud
Your Android needs protection
Use Dr.Web
- The first Russian Anti-virus for Android
- More than 135 million downloads on Google Play alone
- Free for users of Dr.Web home products

![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments