May 4, 2017
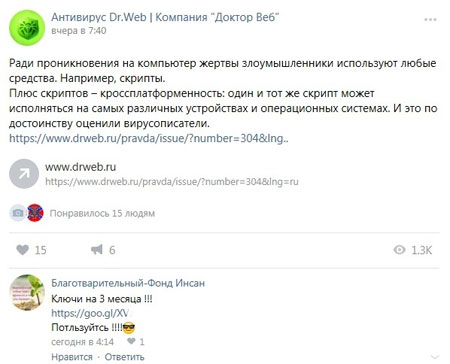
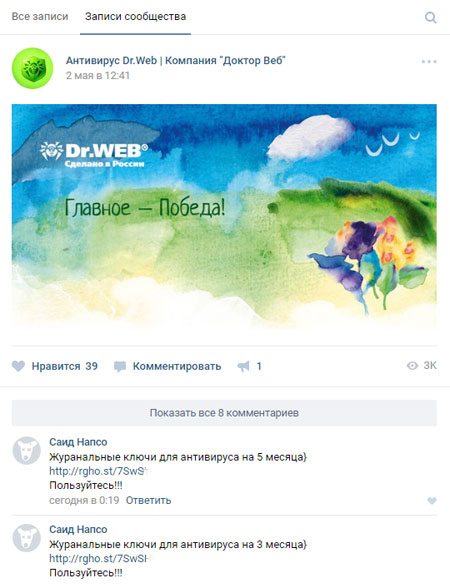
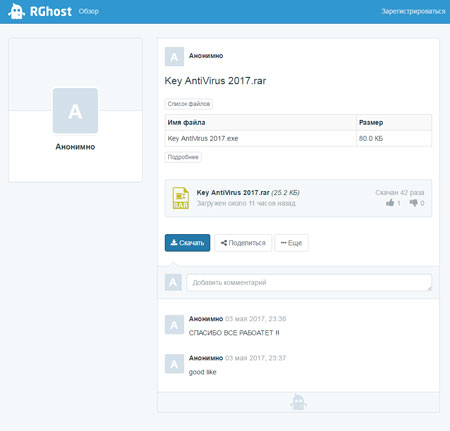
Recently, in the official “Doctor Web” group on the “VK” social network, messages appeared from anonymous users offering the option to download free license keys for the Dr.Web Anti-virus. Usually such messages contain a short link to RGhost file hosting. If a potential victim follows it, they will be asked if they want to download a 26 KB RAR archive. Naturally, moderators of the Doctor Web group try to delete such messages as quickly as possible, but sometimes they are not quick enough to remove them right after they are published.
The archive contains a small executable file that has an icon of a simple text document. All the examined samples of this application reveal that it is the same backdoor, but the cybercriminals have repacked the malicious program each time before publishing it online in order to avoid signature detection. As a result, the Trojan, named Trojan.MulDrop7.26387, is not immediately detected by the Dr.Web Anti-virus—each new sample of the virus is detected only after the virus databases get updated once again. Apparently, when distributing the Trojan under the guise of Anti-virus license keys, the cybercriminals were hoping to ensnare careless users who either don’t have Anti-virus software or use a free program for protection.
Trojan.MulDrop7.26387 is a multipurpose backdoor with quite an amusing, primitive range of functions. It is created on the basis of the widely known Remote Administration Tool (RAT) Njrat 0.7 Golden By Hassan Amiri, which is detected by Dr.Web as BackDoor.NJRat.1013.
After launch, the backdoor connects to its command and control (C&C) server and sends information about the infected computer, the serial number of a hard drive, the version and bitness of the installed operating system, the name of the computer, the name of the manufacturer, the version of the anti-virus, if present, and the availability of a connected webcam. The Trojan can execute the following commands of cybercriminals:
- Replace the Windows Desktop wallpaper;
- Turn off or restart the computer;
- Output a system message with the specified text on the screen;
- Swap the functions of mouse keys;
- Play a specific phrase using a voice synthesizer and speakers;
- Hide and then restore the Windows taskbar;
- Open or close the optical disc drive;
- Turn a display on and off;
- Open the specified link in a browser;
- Read, install or remove the specified value of the system registry;
- Receive a screenshot and send it to the C&C server;
- Download and launch the specified executable file;
- Refresh or remove the Trojan’s executable file;
One of the most dangerous functions of the backdoor is an embedded keylogger that records pressed keys. Upon command, this data is downloaded on the cybercriminals’ server. In addition, the Trojan is able to unexpectedly display on the infected computer SWF videos containing frightening images.
Doctor Web’s specialists note that such malicious programs, whose main purpose is to frighten or confuse users, are quite rare these days. The majority of Trojans are aimed at making a profit, and secondary school age children are the ones most likely to distribute viruses in order to frighten users just for “fun”.
Conventional wisdom says that there is no such thing as a free lunch, so all the different kinds of offers users come across to download license keys for commercial software are fraud anyway. Doctor Web advises users to be vigilant and not fall for such provocations.

![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments