Doctor Web discovers first encoder written in Go and develops decryption technique
Real-time threat news | Hot news | All the news | Virus alerts
October 11, 2016
New versions of ransomware Trojans appear every month. What makes this Trojan notable is that it is the first ransomware program written in Go, the language developed by Google. Doctor Web’s analysts had never before come across an encoder developed using this technology. Once launched, Trojan.Encoder.6491 installs itself on the system under the name Windows_Security.exe. Then, using the AES algorithm, the Trojan starts encrypting files on disks. However, files whose names contain the following strings are not encrypted:
tmp
winnt
Application Data
AppData
Program Files (x86)
Program Files
temp
thumbs.db
Recycle.Bin
System Volume Information
Boot
Windows
.enc
Instructions
Windows_Security.exe
The Trojan encrypts 140 different types of files, identifying them according to their extensions. Trojan.Encoder.6491 encrypts original file names with the Base64 method and appends the compromised files with the .enc extension. For example, the file name Test_file.avi is changed to VGVzdF9maWxlLmF2aQ==.enc.
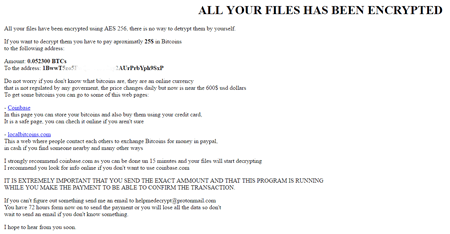
Then, in a browser window, the Trojan opens the file Instructions.html, which demands that a ransom be paid in the Bitcoin cryptocurrency:
It should be noted that Trojan.Encoder.6491 regularly checks the Bitcoin wallet to which the victim is to transfer the ransom amount. Once payment is made, the Trojan automatically decrypts the files, using an internal function.
Doctor Web’s security researchers have developed a new technique that can help decrypt files compromised by the malware. If you have fallen victim to Trojan.Encoder.6491, follow the recommendations below:
- Notify the police.
- Do not, under any circumstances, attempt to solve the problem by using some utility to reinstall, “optimize” or “clean” the operating system.
- Do not delete any files from your computer.
- Do not try to restore the encrypted data yourself.
- Contact Doctor Web’s technical support (its free decryption service is only available to users who have purchased commercial licenses for Dr.Web products).
- Attach a file encrypted by the Trojan to the request ticket.
- Wait for a response from technical support. Due to the large volume of requests, this may take some time.
Once again we would like to point out that the free decryption service is only available to users who have purchased commercial licenses for Dr.Web products. Doctor Web cannot guarantee that all of your files will be decrypted successfully. However, our specialists will do their best to recover the encrypted data.
Use Data Loss Prevention to protect your files from encryption ransomware
| More about encryption ransomware | Configuration presentations tutorial | Free decryption | Categorie "Encrypt everything" |