Doctor Web discovers Trojan that can buy Google Play apps
Real-time threat news | Hot news | Threats to mobile devices | All the news | Virus alerts
August 4, 2016
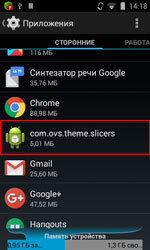
This Trojan, named Android.Slicer.1.origin, is usually installed by other malware programs on a device and executes functions specific to popular service utilities and SEO software. In particular, Android.Slicer.1.origin can show RAM consumption information and terminate running processes. In addition, it allows Bluetooth and Wi-Fi modules to be enabled or disabled. This Trojan does not create a shortcut on the screen, so the user cannot independently launch the application.
Although the Trojan may appear to be a benign application, it performs typical adware functions. Therefore, once Android.Slicer.1.origin is launched, or once the home screen is turned on/off, or the Wi-Fi module is disabled, the Trojan transmits (to the command and control (C&C) server) information about the IMEI identifier of the infected device, the MAC address of the Wi-Fi adapter, the name of the device’s manufacturer, and the operating system version. In turn, the C&C server replies with the following instructions:
- Add a shortcut to the home screen
- Display an advertisement
- Open advertising webpages in the browser or in a Google Play application
However, Android.Slicer.1.origin can also install specific applications including paid ones. For this purpose, it uses another Trojan—Android.Rootkit.40, which is similar to the SU utility used for working with root privileges. If Android.Rootkit.40 is in the /system/bin catalog, Android.Slicer.1.origin can automatically buy and install Google Play apps.
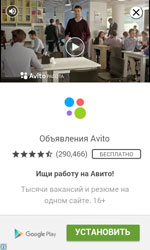
To do this, Android.Slicer.1.origin opens a section in one of the specified applications and, using the root privileges of Android.Rootkit.40, runs a standard uiautomator utility. Thus, the Trojan gets information about all the windows and interface elements displayed on the screen at that moment. Then Android.Slicer.1.origin searches for information about the buttons having the identifiers com.android.vending:id/buy_button (“Buy” and “Install” buttons) and com.android.vending:id/continue_button (“Continue”), determines their middle coordinates, and starts tapping them until they disappear from the screen. Therefore, Android.Slicer.1.origin can obey hacker commands to automatically purchase almost any paid software program and download free versions of applications, without the user’s knowledge.
Nevertheless, the Trojan’s abilities to covertly buy and install apps are limited. First, Android.Slicer.1.origin uses only those button identifiers that are represented in Android 4.3 and later. Second, Android.Rootkit.40 cannot operate on devices that have SELinux enabled, i.e., on Android 4.4 and later. Thus, Android.Slicer.1.origin can buy and download other programs only if the infected device runs Android 4.3.
Dr.Web for Android products successfully detect and remove Android.Slicer.1.origin, and, therefore, this malicious program poses no threat to Dr.Web users.