Files compromised by CryptXXX can now be decrypted by Doctor Web
Real-time threat news | Hot news | All the news | Virus alerts
June 14, 2016
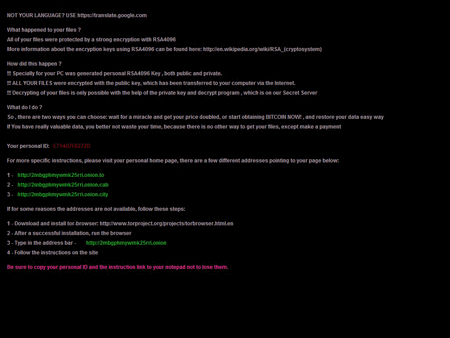
Trojan.Encoder.4393, also known under the name of CryptXXX, is a typical ransomware Trojan. It has several modifications that are being spread all over the world. To make more money on their illegal activity, virus makers created a special service responsible for paid file decryption. A certain interest rate goes to those who distribute the Trojan. All the CryptXXX modifications connect to one C&C server. Websites that offer the paid file decryption use the TOR network. Wide geography of the infection cases proves the popularity of this affiliate program and of the Trojan itself among attackers. All encrypted files are appended with the *.crypt extension, and files containing cybercriminals' demands are named as de_crypt_readme.txt, de_crypt_readme.html, and de_crypt_readme.png.
If you have fallen victim to this malicious program, and files on your computer were encrypted before June 2016, it is possible to restore the compromised data. However, it depends on several conditions and especially on the user’s actions.
- Do not remove any files from your computer or reinstall the operating system. It is also not recommended to use the infected computer until you get detailed instructions from Doctor Web technical support.
- If you have run anti-virus scanning, do not try to cure or remove detected threats—technical support specialists may need them when searching for the decryption key.
- Try to remember as much about the infection circumstances as possible: received dubious email messages, programs downloaded from the Web, or visited websites.
- If you have the email message with the attachment that infected your computer once it was opened, do not remove it—our specialists may need it to identify the version of the Trojan.
To decrypt files compromised with CryptXXX, go to the Doctor Web decryption service page. Free decryption services are only available to users who have valid commercial Dr.Web licenses and whose systems—at the moment of infection—were protected by Dr.Web Security Space (Windows) or by Dr.Web Anti-virus for OS X or Linux (version 10 or later) or by Dr.Web Enterprise Security Suite (6+). Other users can purchase Dr.Web Rescue Pack by sending the standard request form: the service is charged if the analysis shows that your files can be recovered. Besides, clients who used this service can get free two-year license for Dr.Web Security Space for 1 computer. To find more information about ransomware Trojans, follow this link.