July 16, 2014
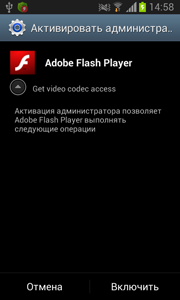
Dubbed Android.BankBot.21.origin by Doctor Web and distributed under the guise of Adobe Flash Player, the malware is designed to steal credit card information and to send and intercept SMS messages.
Once the Trojan has been installed and launched, it attempts to gain administrator privileges by displaying a corresponding system request every 0.1 seconds, giving users virtually no chance to decline it. In this way the malicious program guarantees itself a certain level of protection against its possible future removal.
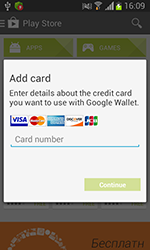
In order to get hold of credit card information, Android.BankBot.21.origin checks the availability of an active Google Play application window. If one is present, the malware displays a standard credit card information form used to associate a credit card with an account.
 |
 |
 |
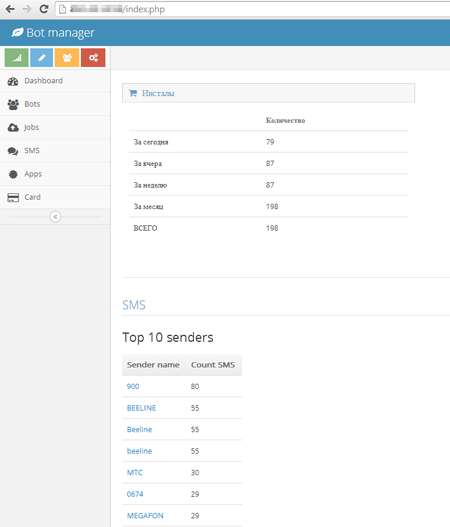
All the submitted information, such as the card number, expiration date and CVC code, and the address and phone number of the cardholder, is transmitted to the attackers' server. In addition, information about the infected device, including the handset model, IMEI, OS version, list of installed application and the contents of all the available short messages, also ends up on the criminals' server.
Apart from serving its main purpose—stealing valuable financial information—Android.BankBot. 21.origin can carry out a number of other actions when commanded by the attackers to do so. These commands can be sent directly by the control server as well as via short messages. In particular, the Trojan can intercept all incoming SMS messages and can also send specific text messages to certain numbers.
There are indications that this malicious program can be used by cybercriminals to automatically debit bank accounts, so Android handheld owners must take extra care and refrain from installing suspicious applications.
Dr.Web for Android detects and easily neutralises this threat.

![[VK]](http://st.drweb.com/static/new-www/social/no_radius/vkontakte.png)
![[Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
![[facebook]](http://st.drweb.com/static/new-www/social/no_radius/facebook.png)

Tell us what you think
To ask Doctor Web’s site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments