New Trojan for Android can mount DDoS attacks
All the news | Virus alerts
December 26, 2012
After installation, Android.DDoS.1.origin creates an application icon, similar to that of Google Play. If the user decides to use the fake icon to access Google Play, the original application will be launched, which significantly reduces the risk of any suspicion.
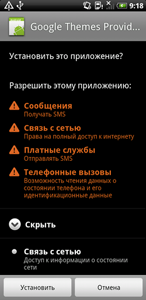 |  |
When launched, the Trojan tries to connect to a remote server and, if successful, it transmits the phone number of the compromised device to criminals and then waits for further SMS commands. Supported directives include attack a specified server and send SMS. If criminals want the Trojan to attack a server, a command message will contain the parameter [server:port]. Upon receipt of such a command Android.DDoS.1.origin starts to send data packets at the specified address. If the malicious program is required to send an SMS, the command message will contain the message text and the number to which it should be sent. Activities of the Trojan can lower performance of the infected handset and affect the well-being of its owner, as access to the Internet and SMS are chargeable services. Should the device send messages to premium numbers, malicious activities will cost the user even more.
It is not quite clear yet how the Trojan spreads but most probably criminals employ social engineering tricks and disguise the malware as a legitimate application from Google.
It is worth noting that the code of Android.DDoS.1.origin is heavily obfuscated. Given that the Trojan can carry out attacks on web sites and send various text messages to any number, including those of content providers, we can assume that the malware can also be used to conduct illegal activities for third parties (e.g, attack a competitor's site, promote products with SMS or subscribe users to chargeable services by sending SMS to short numbers).
Doctor Web's virus analysts continue to examine Android.DDoS.1.origin. Devices running Dr.Web products for Android are well protected from this Trojan.